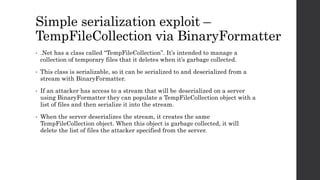
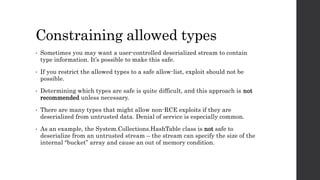
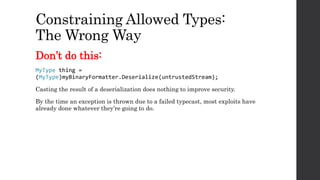
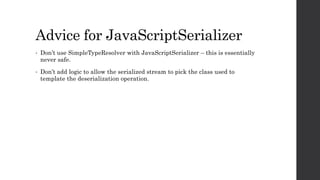
Jonathan Birch from Microsoft discusses how misuse of serialization in .NET can lead to remote code execution (RCE) vulnerabilities. He explains how serialization works and how untrusted data streams containing type information can be exploited to instantiate dangerous classes and execute arbitrary code. He provides advice on how to prevent these vulnerabilities, such as using serialization formats without type information, constraining allowed types, and validating streams have not been modified.