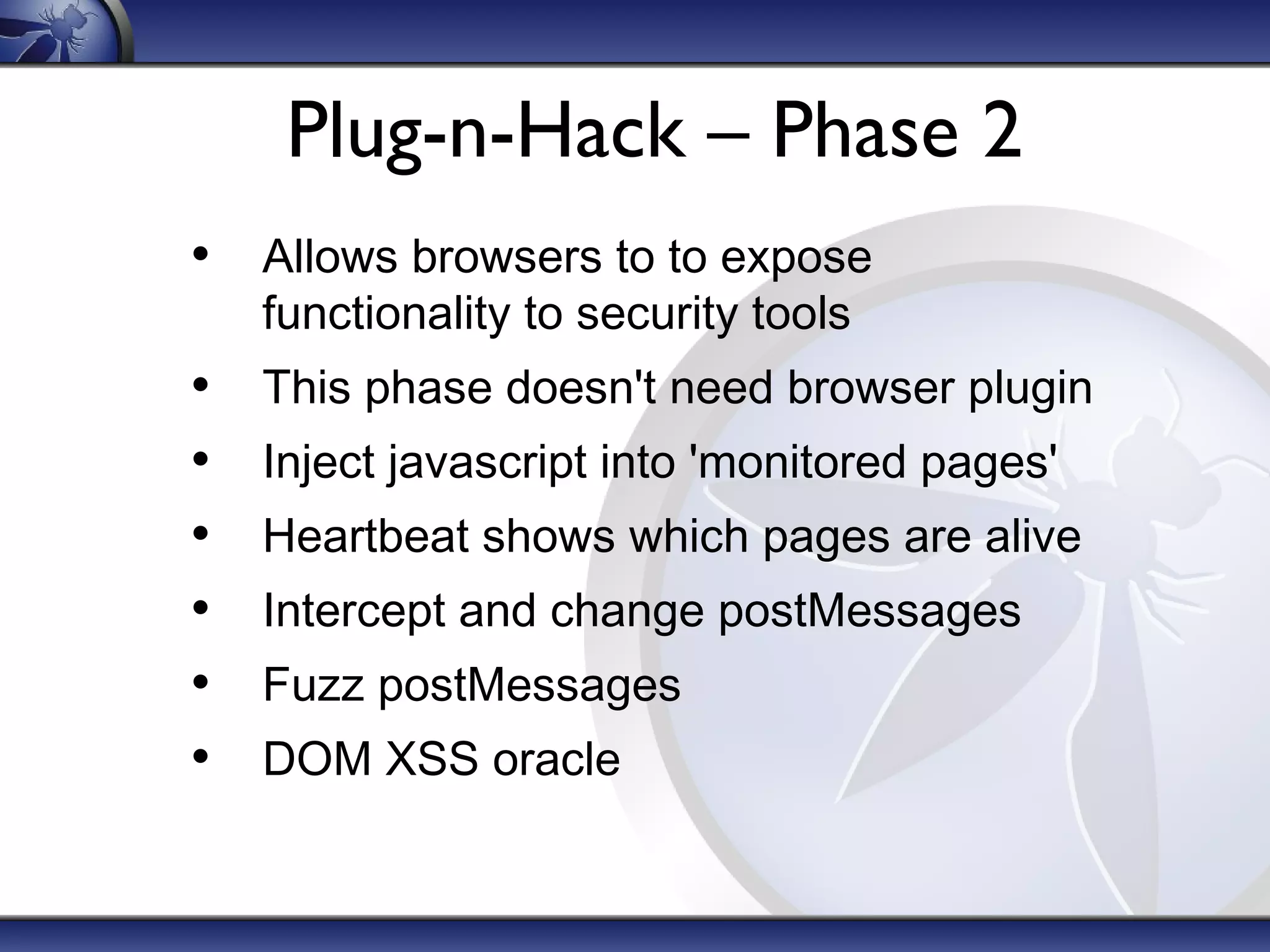
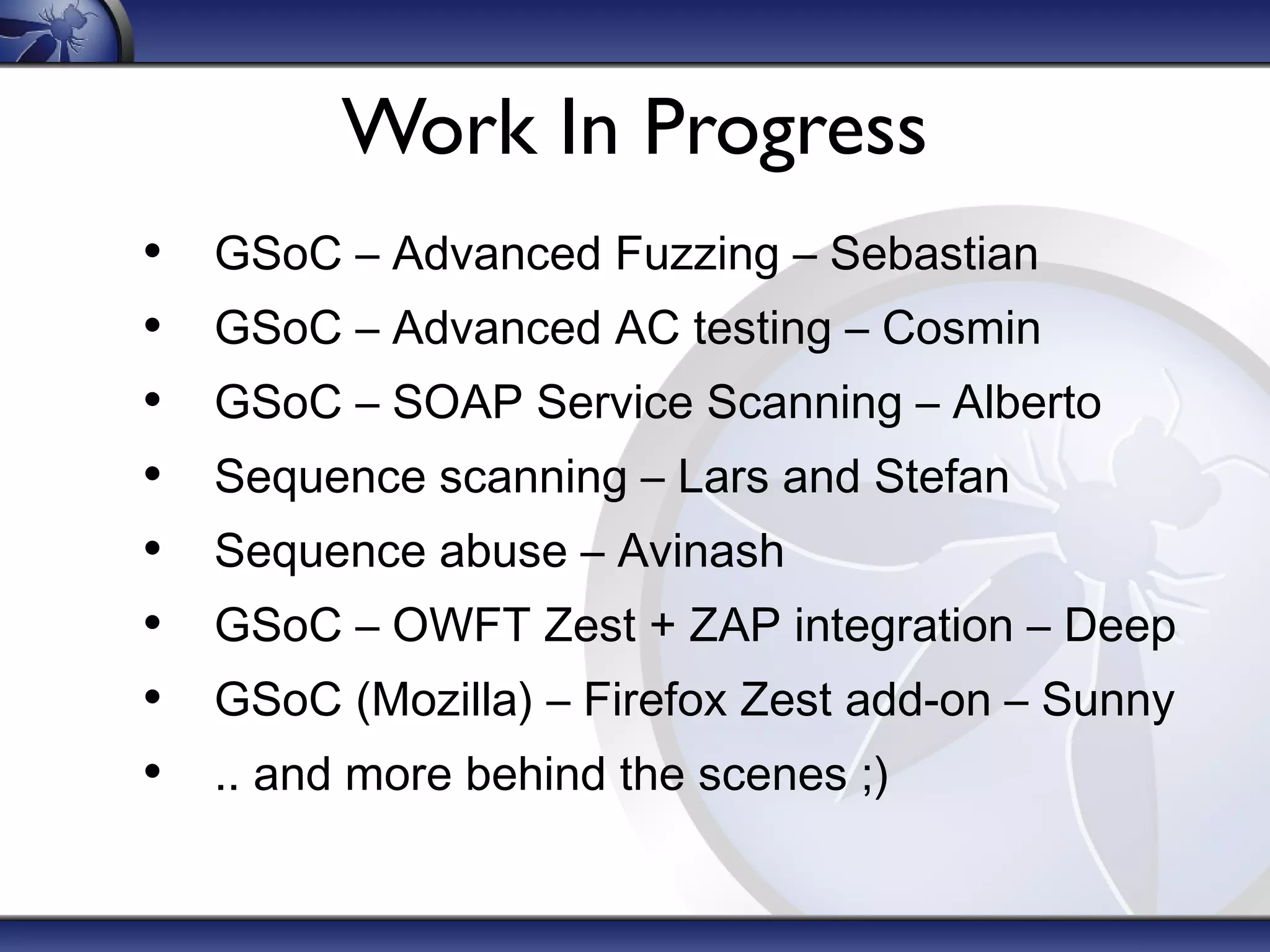
The document discusses the advanced features of OWASP ZAP, an open source web application penetration testing tool. It provides an overview of ZAP's main features like its intercepting proxy, scanners, spiders, and add-ons marketplace. It then describes some advanced features in more depth, including contexts for organizing tests, advanced scanning options, scripting with languages like Zest, and the Plug-n-Hack framework for deeper browser integration. The document concludes by noting various work-in-progress projects and encouraging involvement in ZAP's ongoing development.