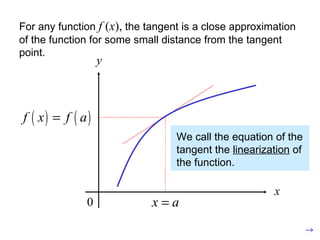
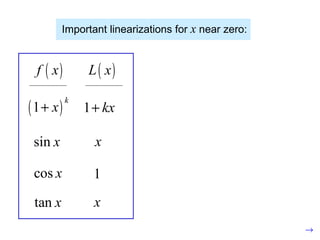
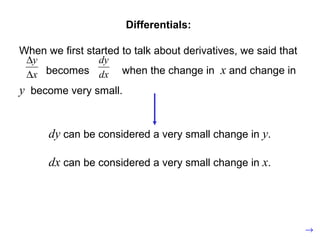
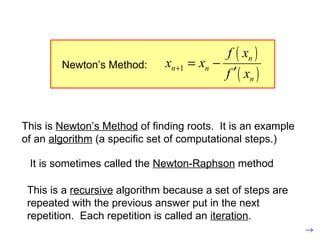
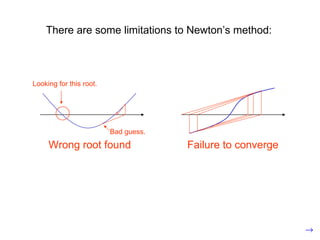
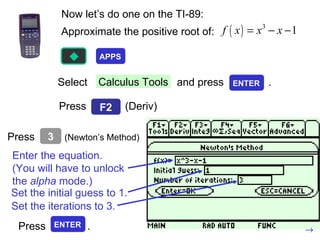
This document discusses linear approximations, differentials, and Newton's method for finding roots of functions. Linear approximations provide a linear equation that closely models a nonlinear function near a given point. Differentials represent very small changes in the variables of a function. Newton's method is an iterative algorithm that finds roots by taking successive guesses, using the slope of the tangent line at each guess to get closer to the root with each iteration. The document provides examples of applying these concepts to find how changes in variables impact a function and to approximate roots of equations.