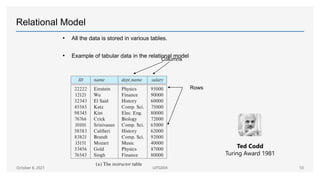
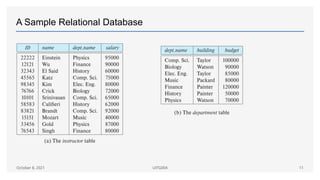
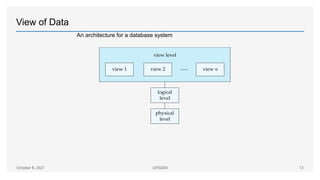
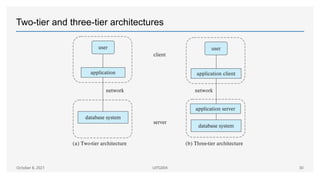
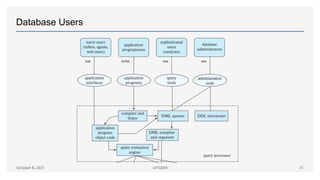
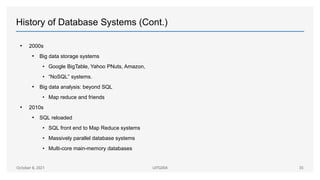
The document provides an introduction to database management systems (DBMS), outlining their purpose, components, and applications in various sectors such as sales, finance, and education. It discusses issues like data redundancy, inconsistency, and integrity, while explaining database models, transaction management, and the roles of database administrators. Additionally, it traces the history of database systems from early data processing to modern big data solutions.