This document provides an introduction to concurrent programming with Akka Actors. It discusses concurrency and parallelism, how the end of Moore's Law necessitated a shift to concurrent programming, and introduces key concepts of actors including message passing concurrency, actor systems, actor operations like sending messages, and more advanced topics like routing, supervision, testing, configuration and remote actors.



![CREATE
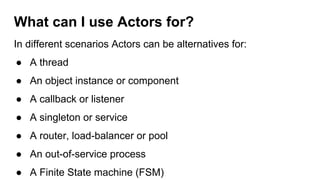
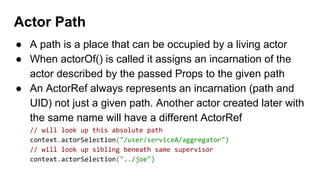
val system = ActorSystem("LogSystem")
val loggerActor = system.actorOf(
Props[LoggerActor],
name = "loggeractor")](https://image.slidesharecdn.com/introductiontoconcurrentprogrammingwithakkaactors-170327041020/85/Introduction-to-concurrent-programming-with-akka-actors-25-320.jpg)

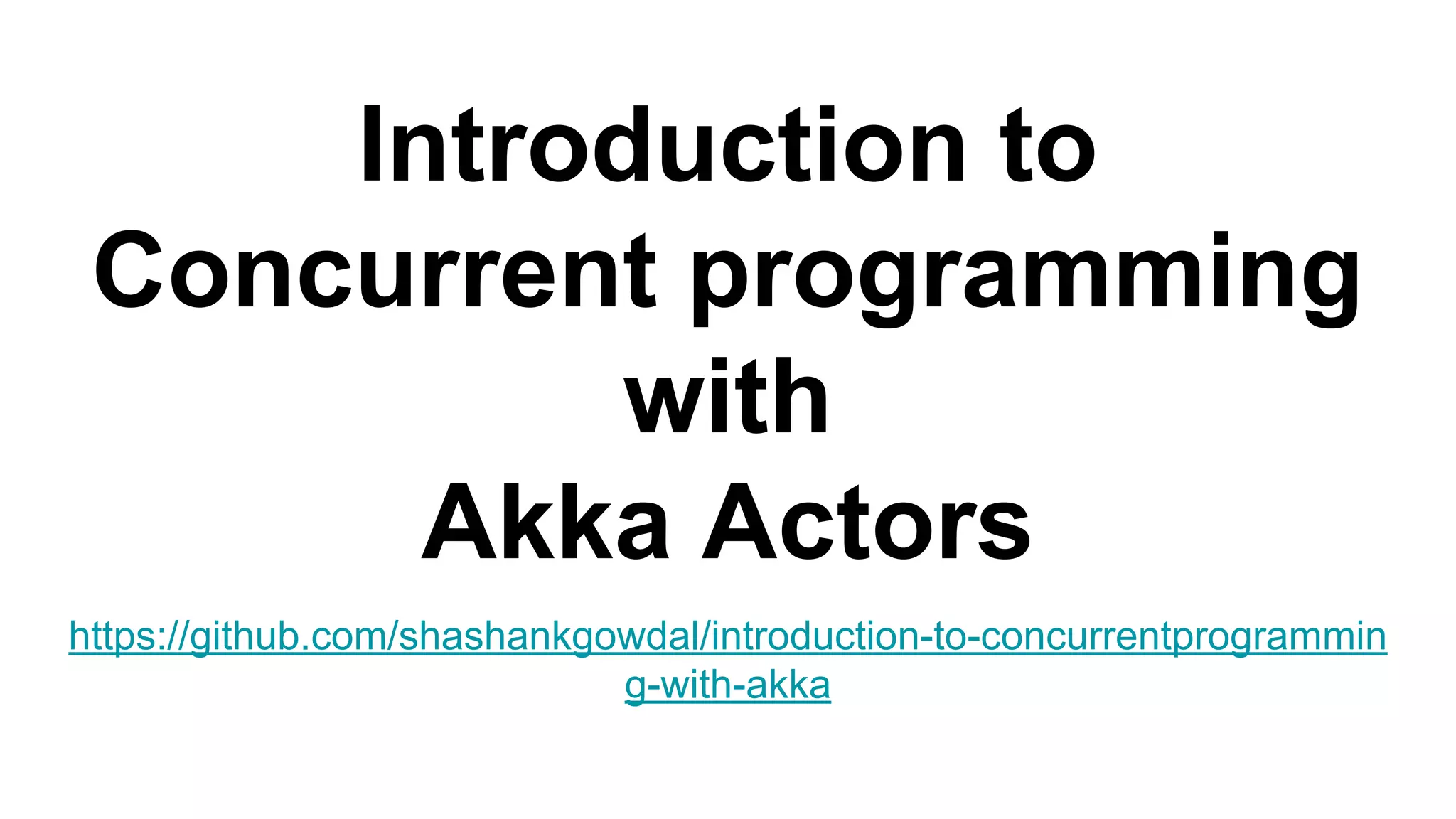
![● Entity that directs the message from source to the destination actor
● Router is also a type of actor
● Does not make use of the store-and-forward mechanism
● Routers dispatch the incoming messages directly to the destination
actor’s mailboxes
system.actorOf(Props[MyActor].withRouter(RoundRobinRouter(nrOfInstances = 5)))
Routers](https://image.slidesharecdn.com/introductiontoconcurrentprogrammingwithakkaactors-170327041020/85/Introduction-to-concurrent-programming-with-akka-actors-48-320.jpg)
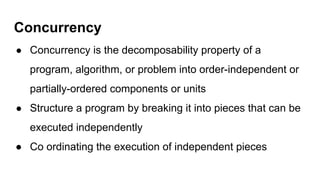
![def preStart(): Unit = ()
def postStop(): Unit = ()
def preRestart(reason: Throwable, message: Option[Any]): Unit = {
context.children foreach { child ⇒
context.stop(child)
}
postStop()
}
def postRestart(reason: Throwable): Unit = {
preStart()
}
Actor API](https://image.slidesharecdn.com/introductiontoconcurrentprogrammingwithakkaactors-170327041020/85/Introduction-to-concurrent-programming-with-akka-actors-50-320.jpg)
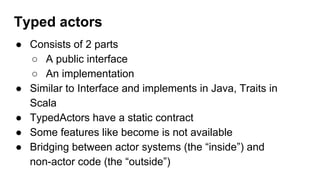
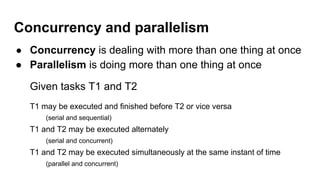
![def squareDontCare(i: Int): Unit //fire-forget
def square(i: Int): Future[Int] //non-blocking send-request-reply
def squareNowPlease(i: Int): Option[Int] //blocking send-request-reply
def squareNow(i: Int): Int //blocking send-request-reply
@throws(classOf[Exception]) //declare it or you will get an UndeclaredThrowableException
def squareTry(i: Int): Int //blocking send-request-reply with possible exception
//Creating an actorRef of a TypedActor
val mySquarer: Squarer = TypedActor(system).typedActorOf(TypedProps[SquarerImpl]())
com.shashank.akka.basic.TypedActorExample
Typed actors](https://image.slidesharecdn.com/introductiontoconcurrentprogrammingwithakkaactors-170327041020/85/Introduction-to-concurrent-programming-with-akka-actors-54-320.jpg)