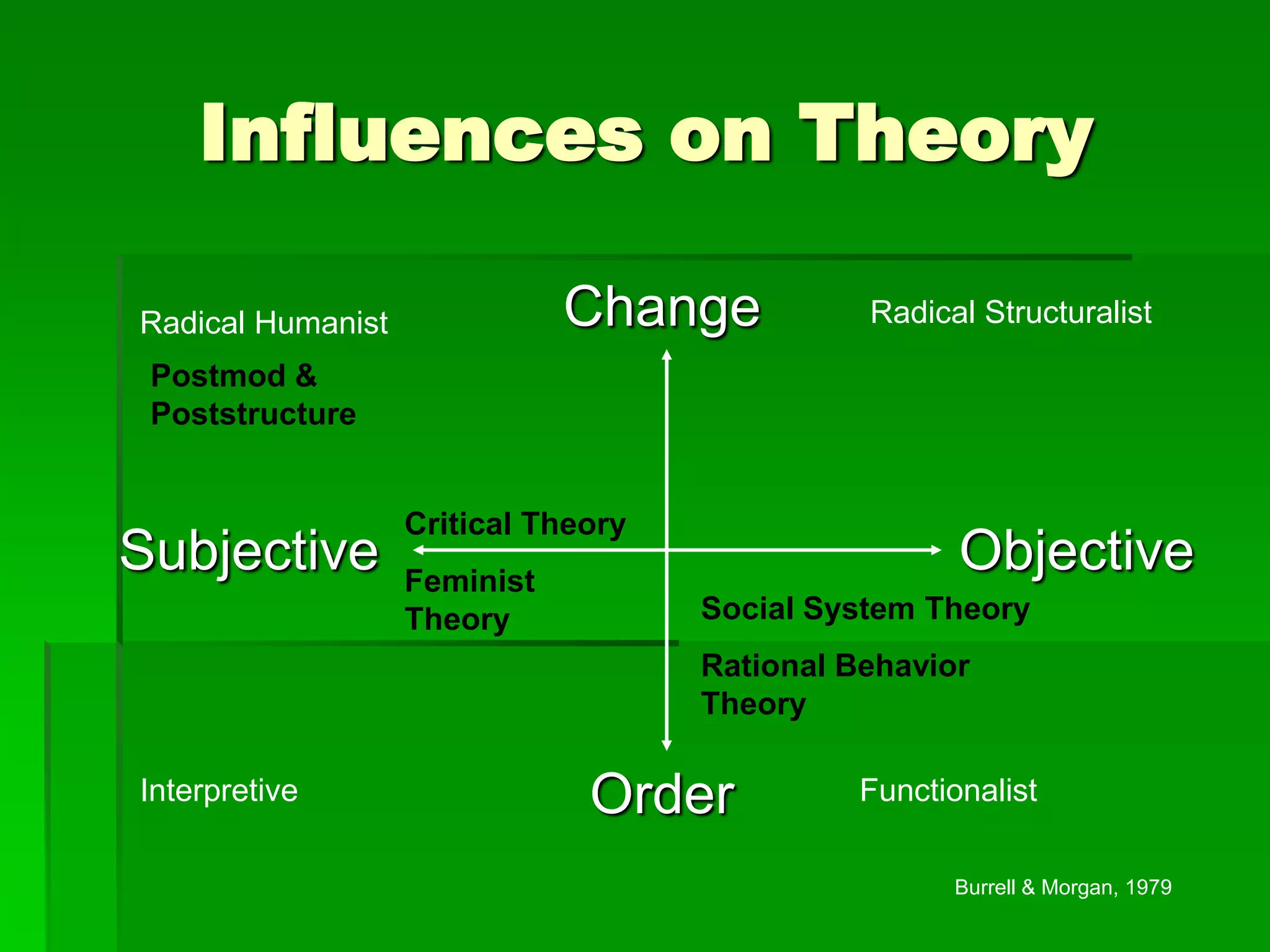
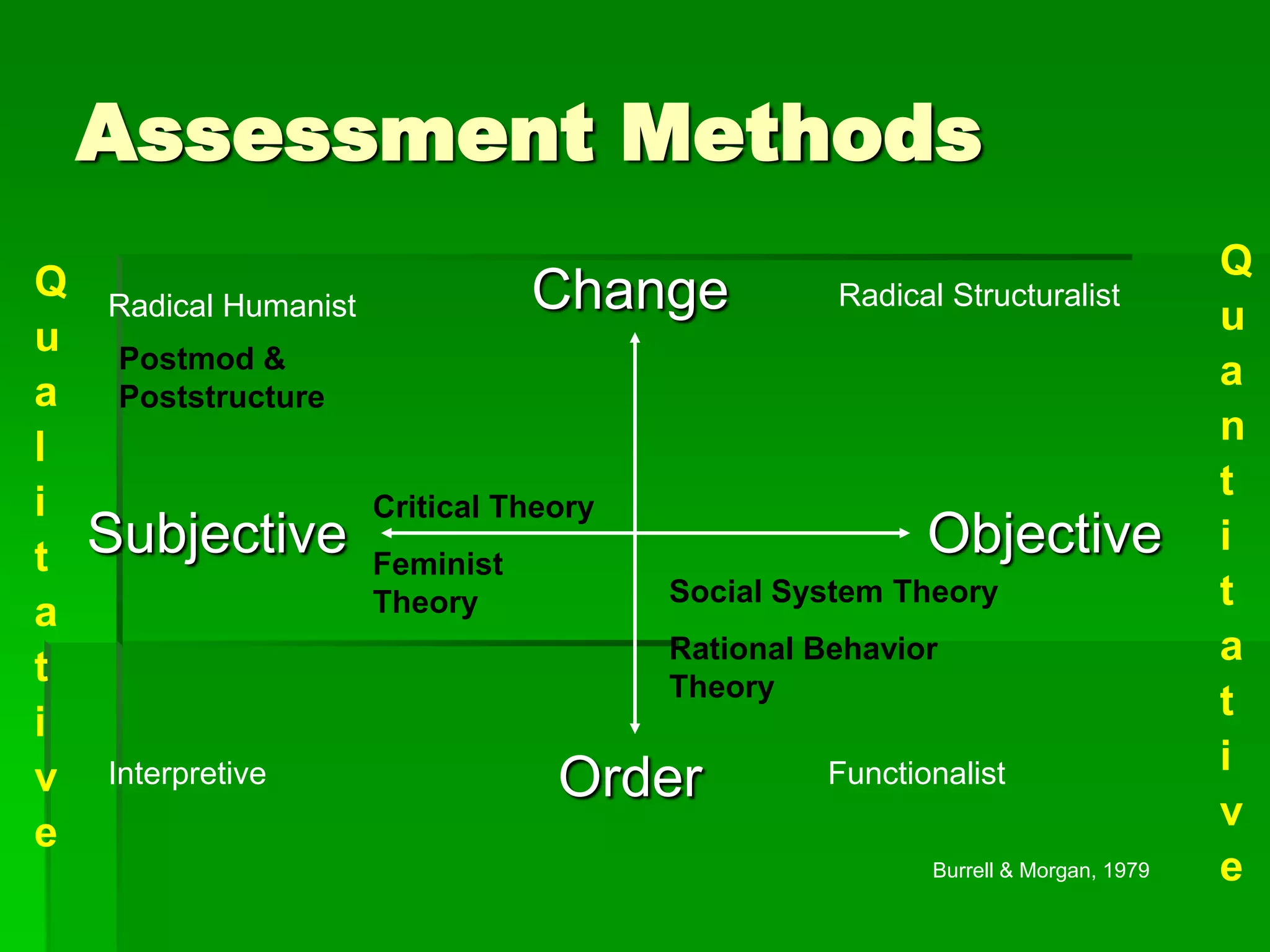
This document discusses different epistemological approaches and their influence on assessment methods. It presents an epistemological continuum ranging from objective to subjective and order to change. It then examines theories like critical theory, feminist theory, and postmodernism that take more subjective and change-oriented approaches. These alternative theories focus on issues like power, gender, and the social construction of knowledge. The document concludes that different epistemological stances can lead researchers to ask different questions and use varying methodologies like qualitative vs. quantitative approaches.