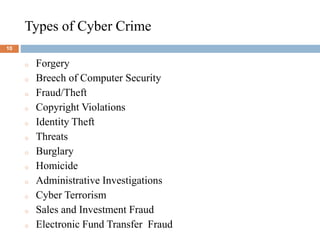
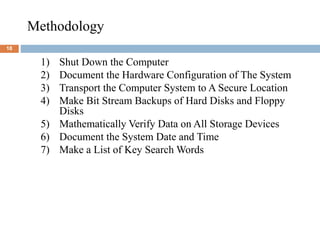
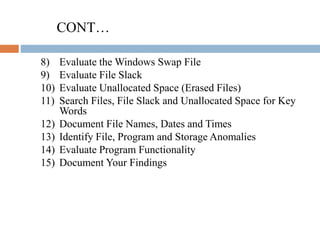
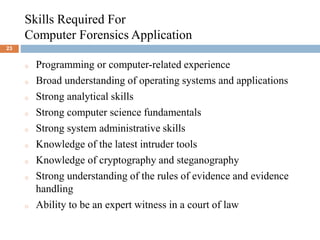
This document provides an overview of computer forensics. It defines computer forensics as the process of identifying, preserving, analyzing and presenting digital evidence in a legally acceptable manner. The document discusses the history, goals, and methodology of computer forensics, as well as who uses these services and the skills required. Computer forensics is used to find evidence for a variety of computer crimes and cybercrimes to assist in arrests and prosecutions.