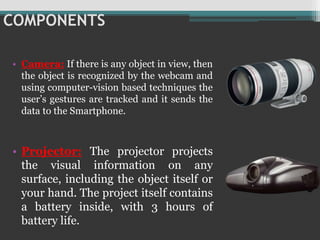
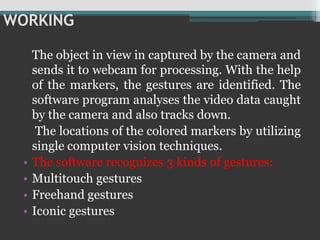
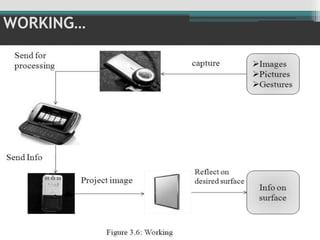
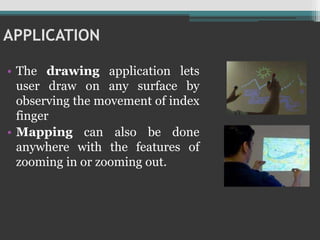
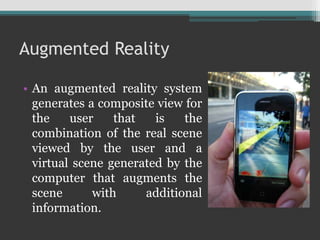
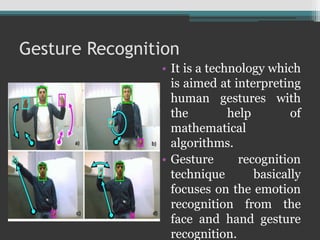
The document discusses Sixth Sense technology, which enables interaction with digital information through hand gestures, enhancing the connection between the physical and digital worlds. Introduced by Steve Mann and popularized by Pranav Mistry, it utilizes components like a camera, projector, and mirror for functionality, with applications in mapping, communication, and education. While it offers advantages such as portability and cost-effectiveness, it also has limitations, and its future potential includes the development of new devices.