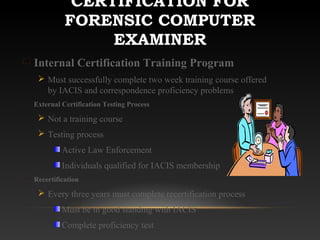
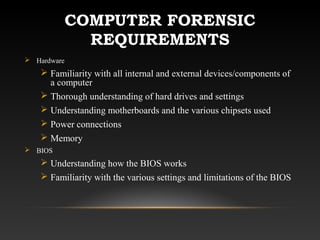
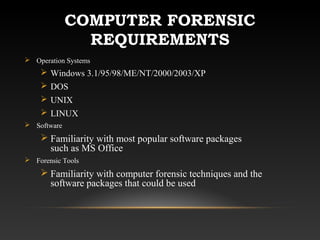
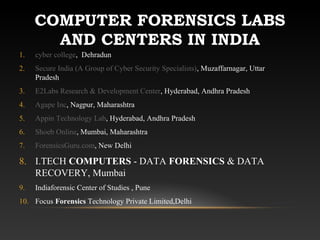
This document provides an overview of computer forensics. It defines computer forensics as the process of preserving, identifying, extracting, documenting and interpreting computer data for legal evidence. The document then outlines the history of computer forensics, the steps involved which include acquisition, identification, evaluation and presentation, certifications available, requirements to work in the field, how evidence is collected, uses of computer forensics in criminal and civil cases, advantages like ability to search large amounts of data quickly, and disadvantages such as costs and ensuring no evidence tampering. It also lists some computer forensics labs and centers in India.