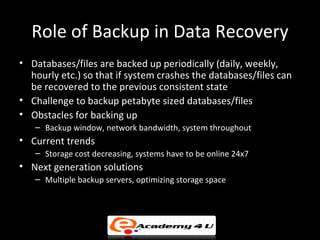
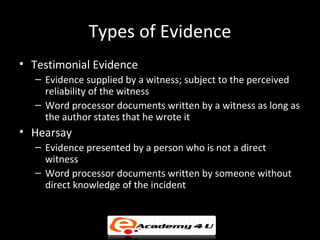
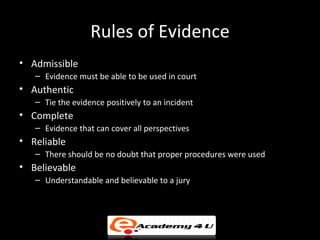
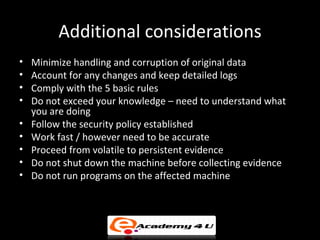
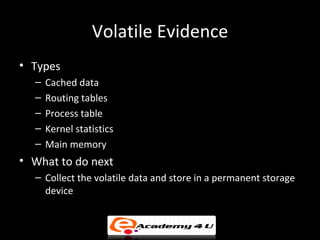
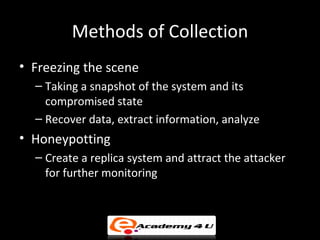
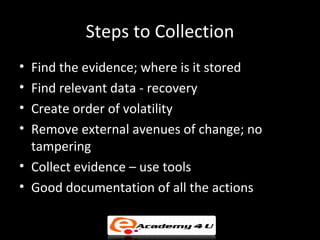
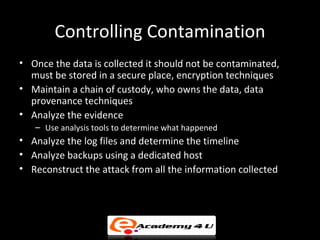
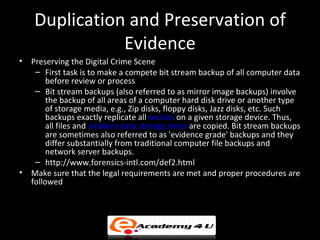
This document discusses best practices for collecting, preserving, and analyzing digital evidence. It covers topics such as data recovery, backup solutions, hidden data recovery techniques, evidence collection methods, and standards for ensuring digital evidence is authenticated and verified. The goal is to extract useful information from seized devices and recovered data in a way that can be used in a court of law to identify attackers and reconstruct security incidents.