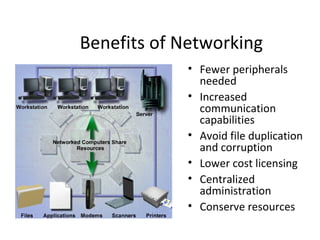
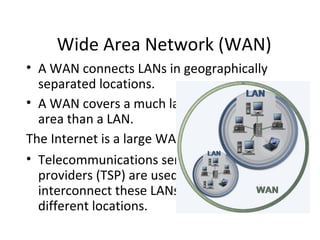
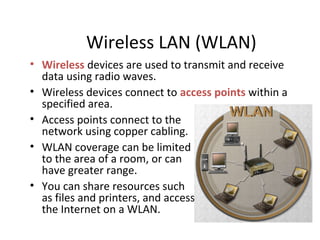
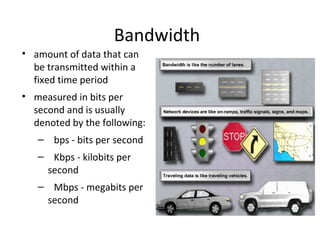
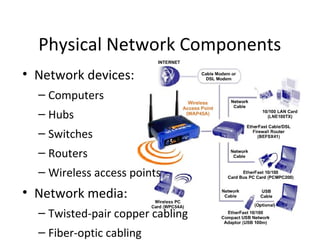
This document discusses computer networks and their components. It describes the principles of networking and different types of networks including local area networks (LANs), wide area networks (WANs), and wireless LANs. The document also discusses peer-to-peer and client/server network models, bandwidth, modes of data transmission, internet protocols, and physical network components like cables, hubs, switches, and routers.