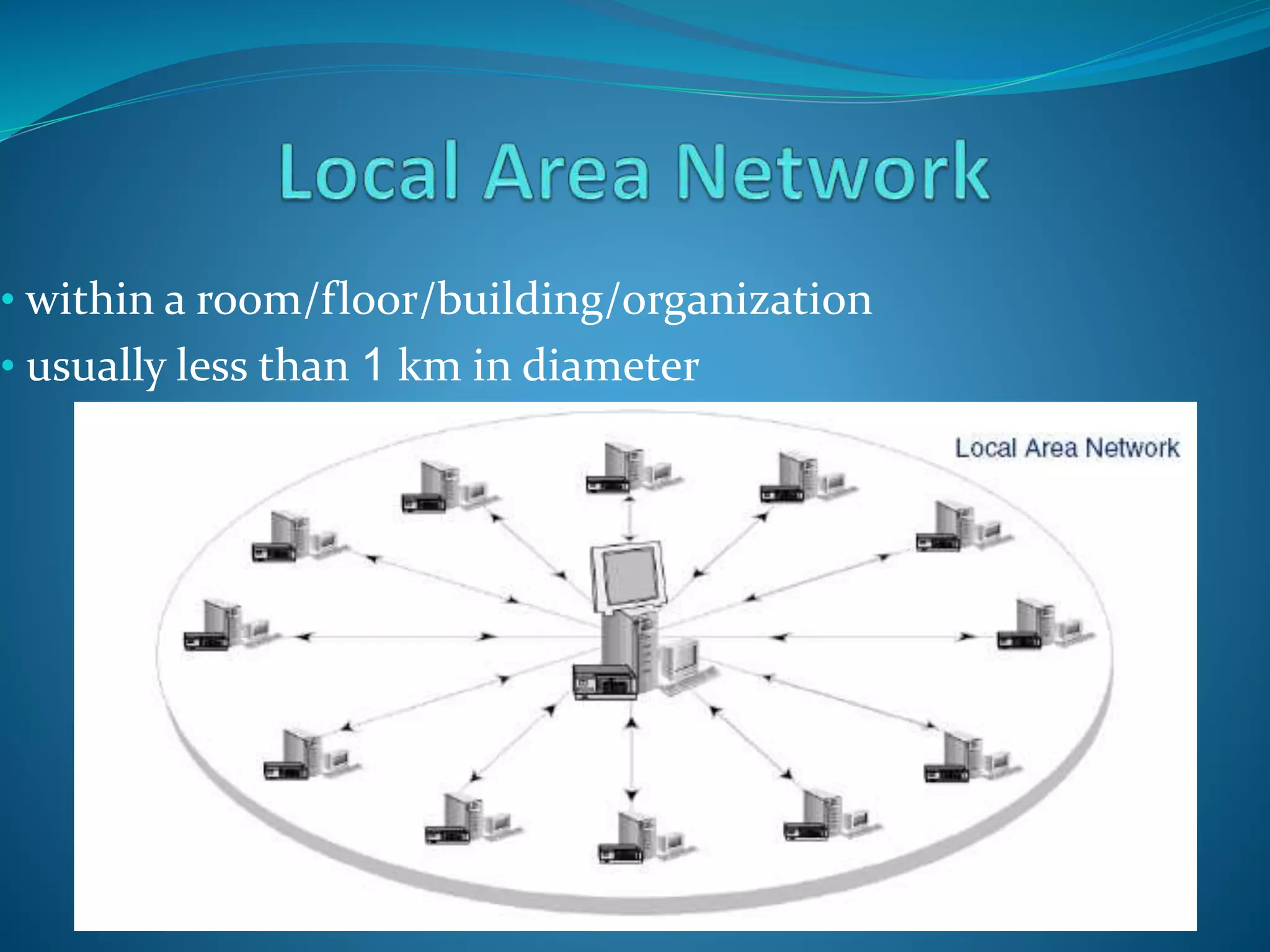
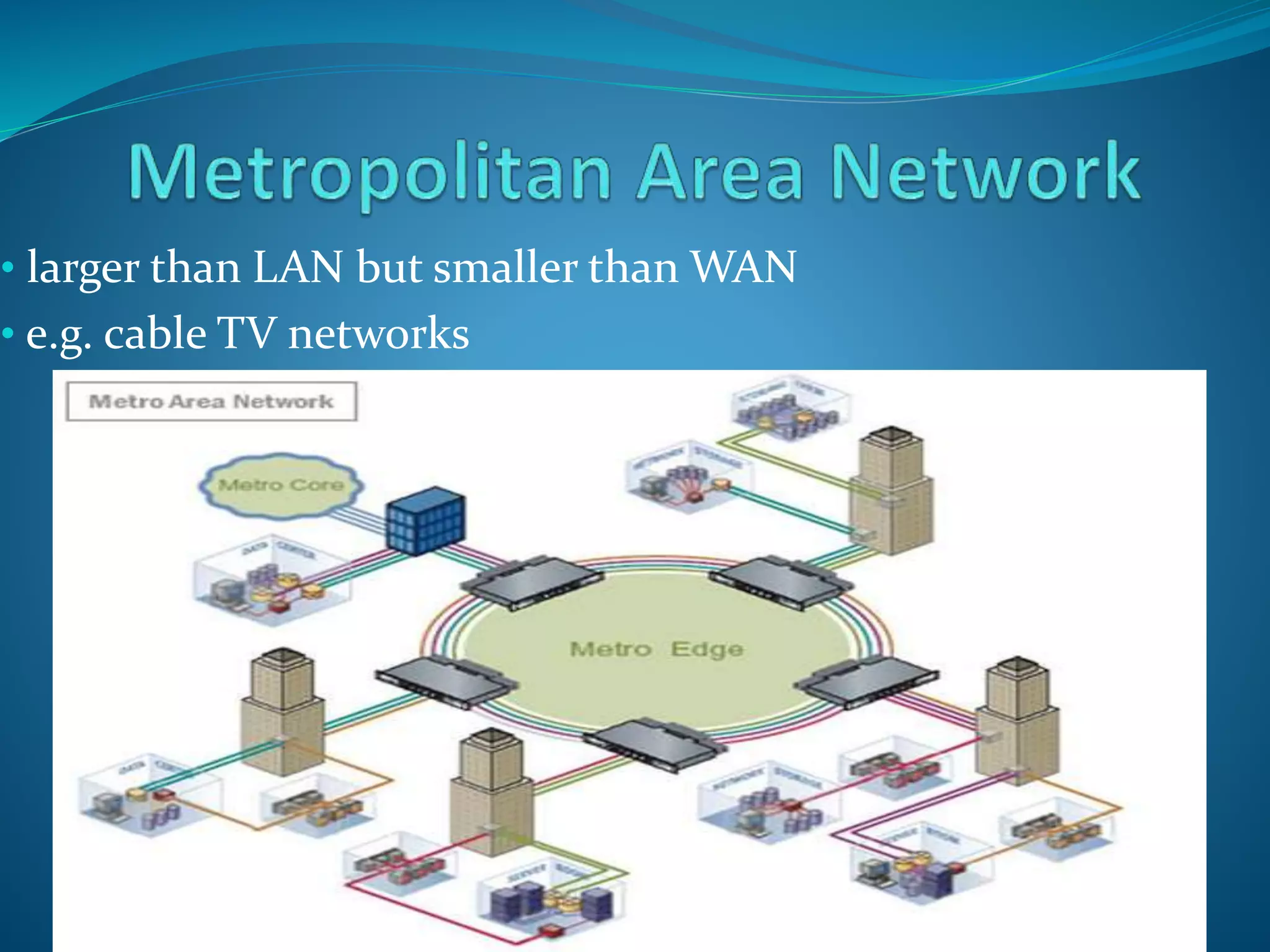
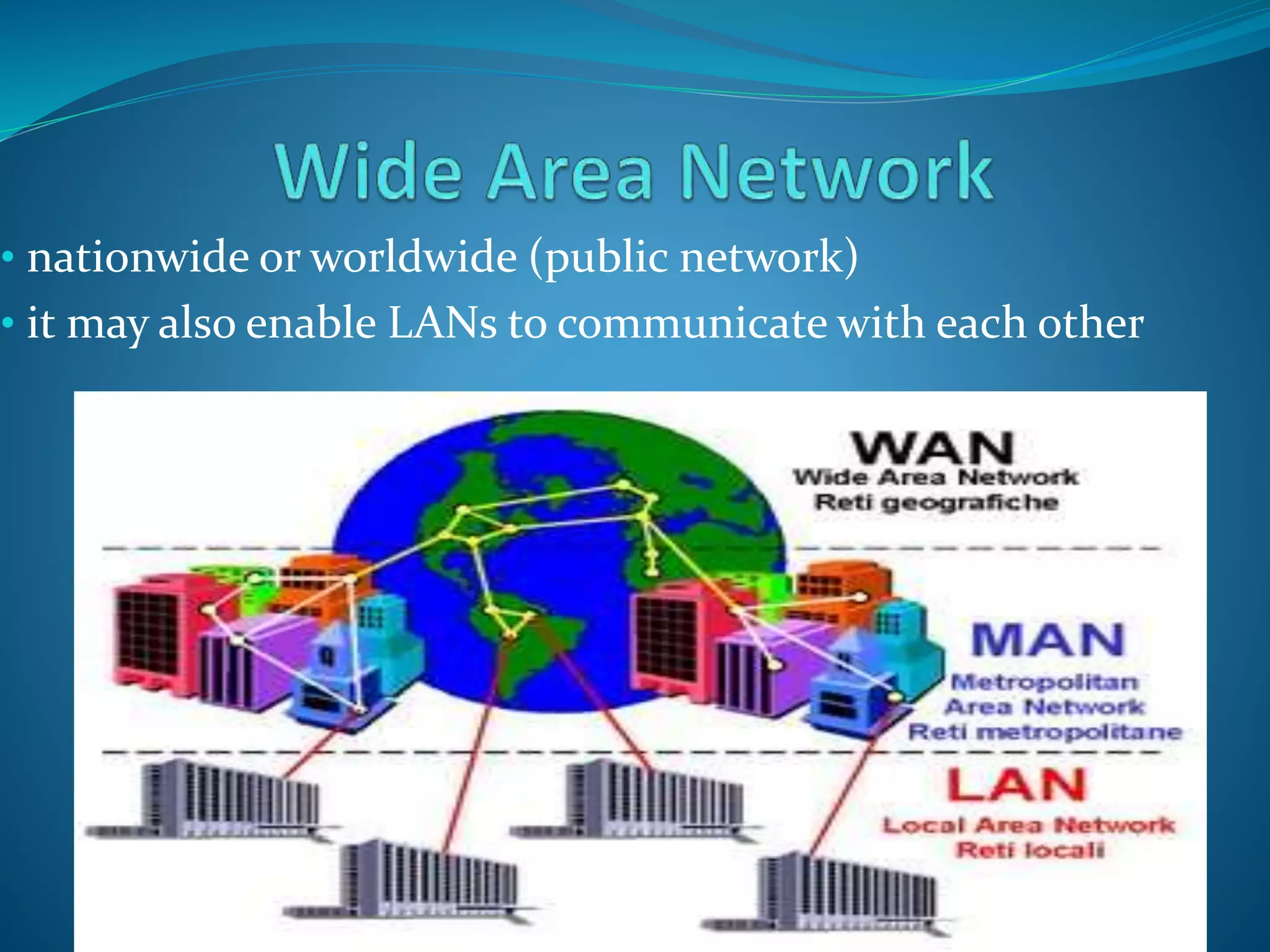
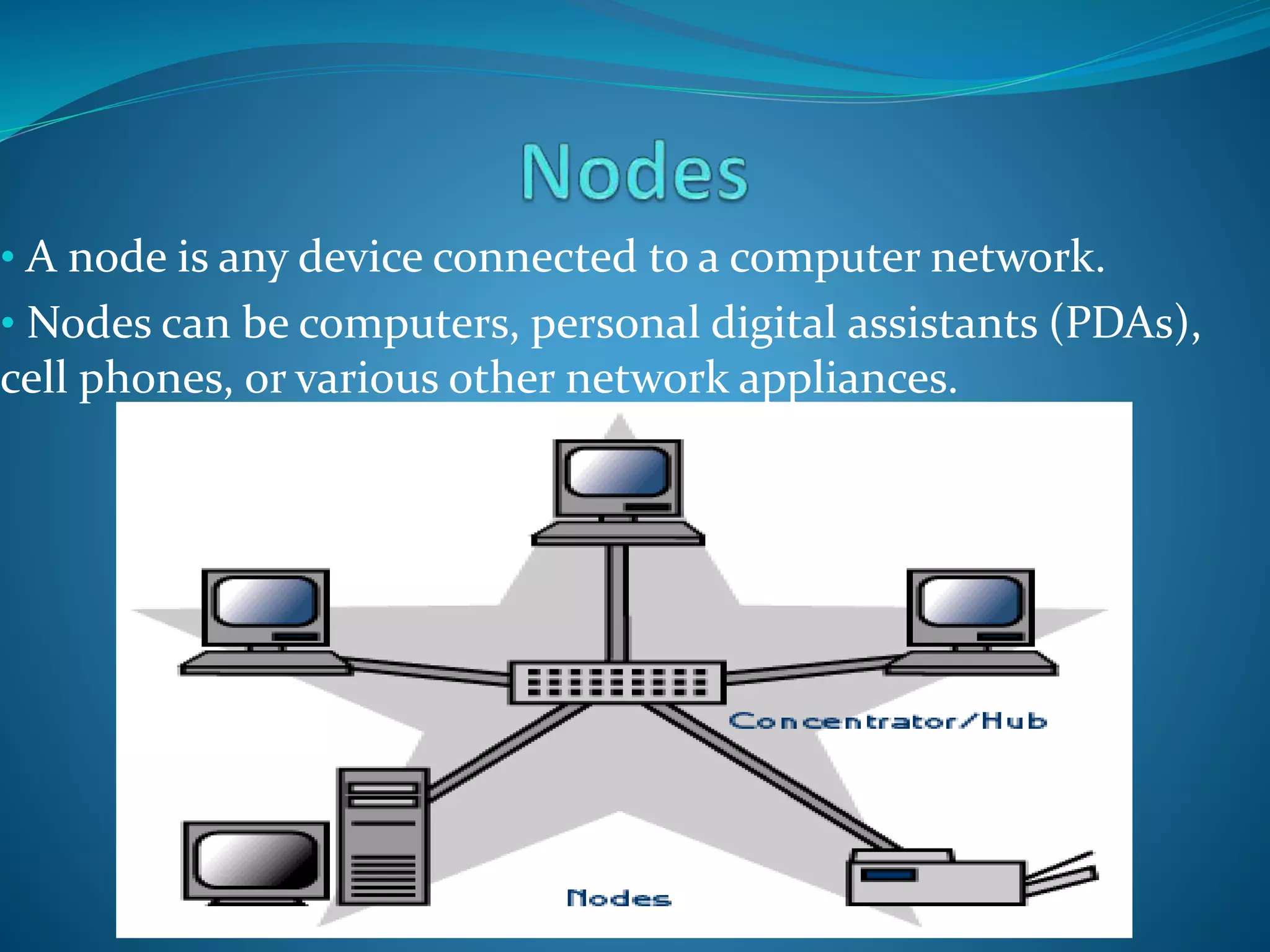
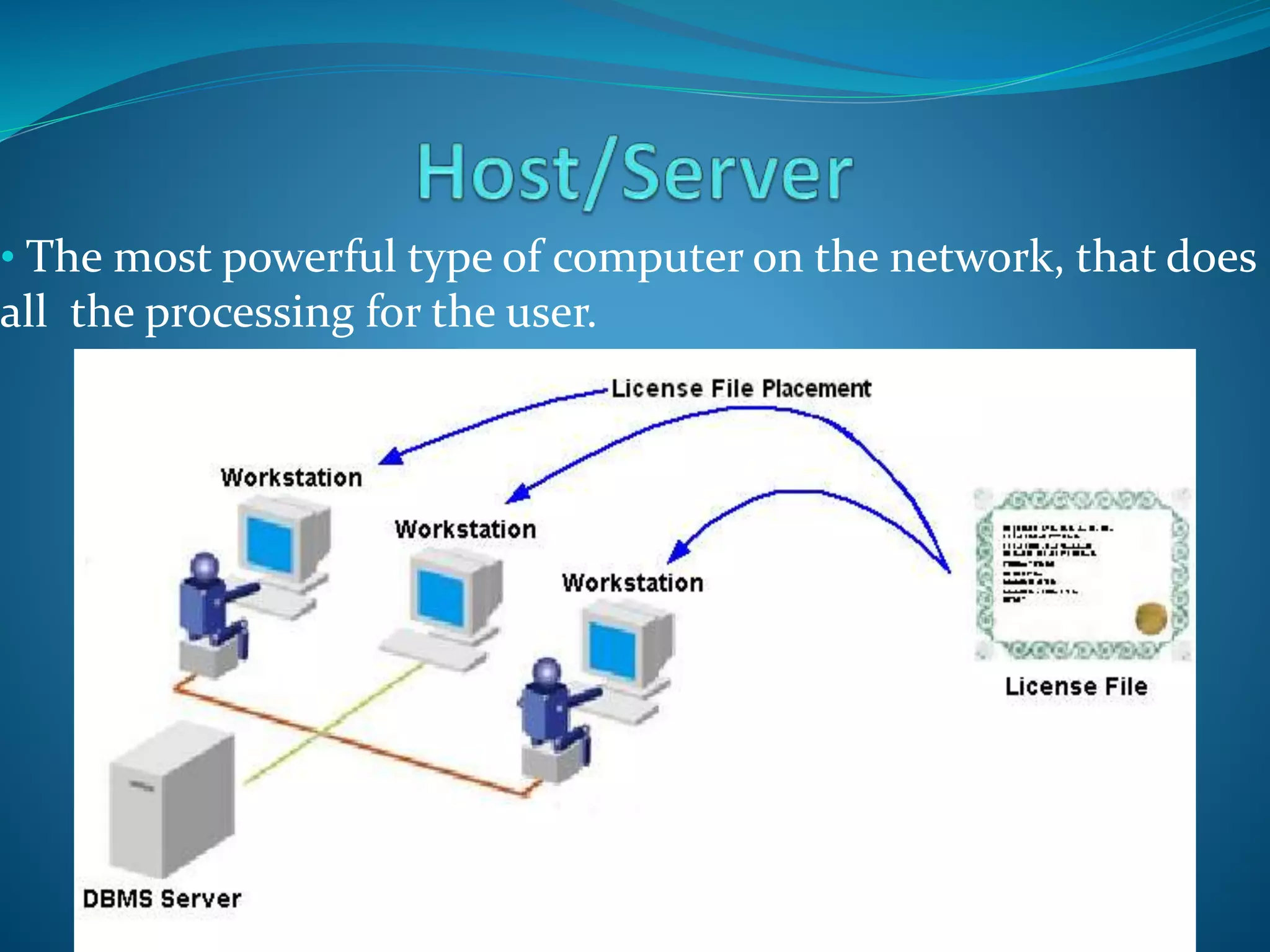
A computer network allows computers to share resources and exchange information. There are several types of networks including local area networks (LANs) within a building, metropolitan area networks (MANs) within a city, and wide area networks (WANs) that span large geographical areas. Networks provide benefits like resource sharing, reliability, reduced costs, and improved communication. They connect using various wired and wireless technologies and different network topologies.