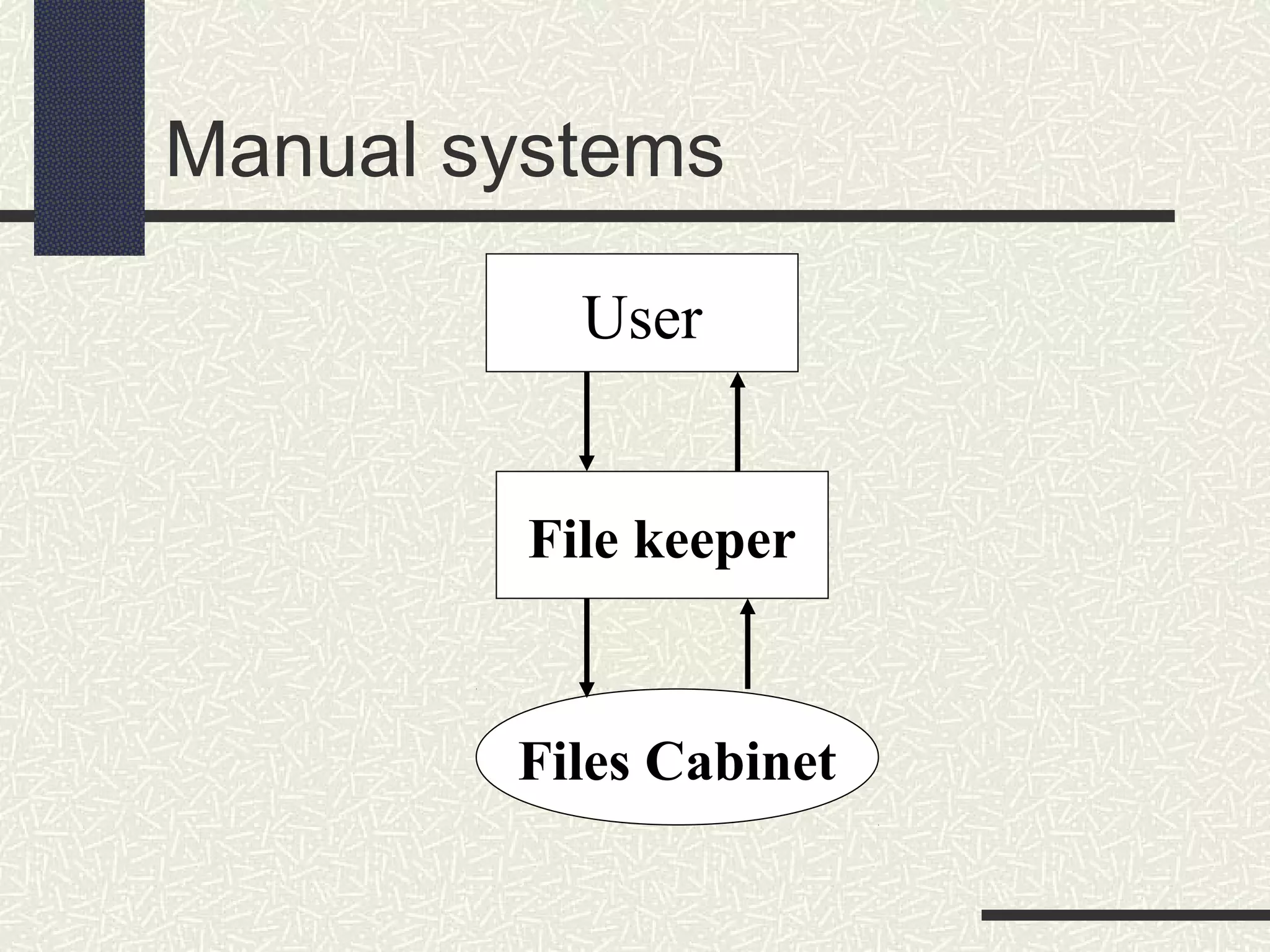
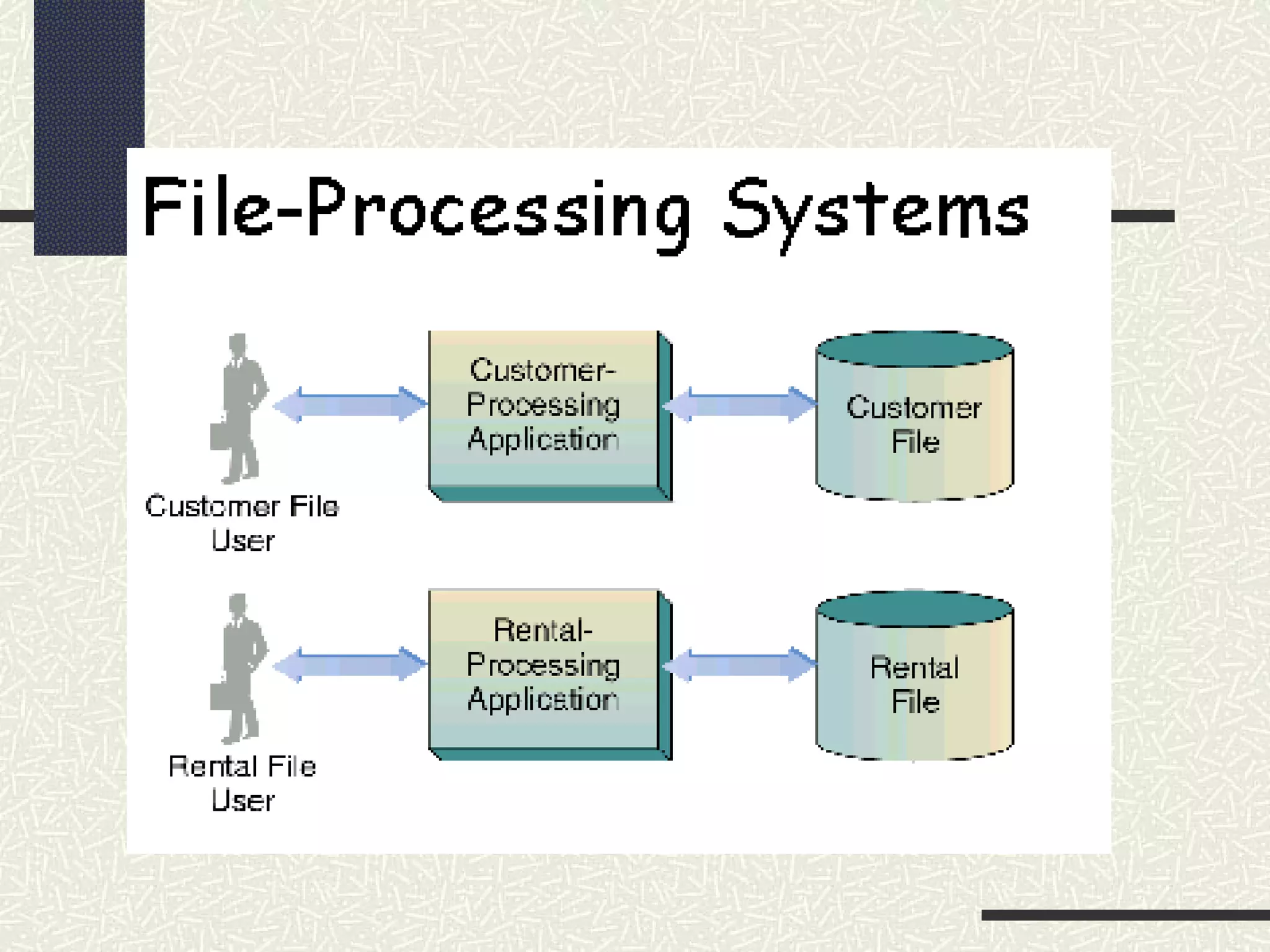
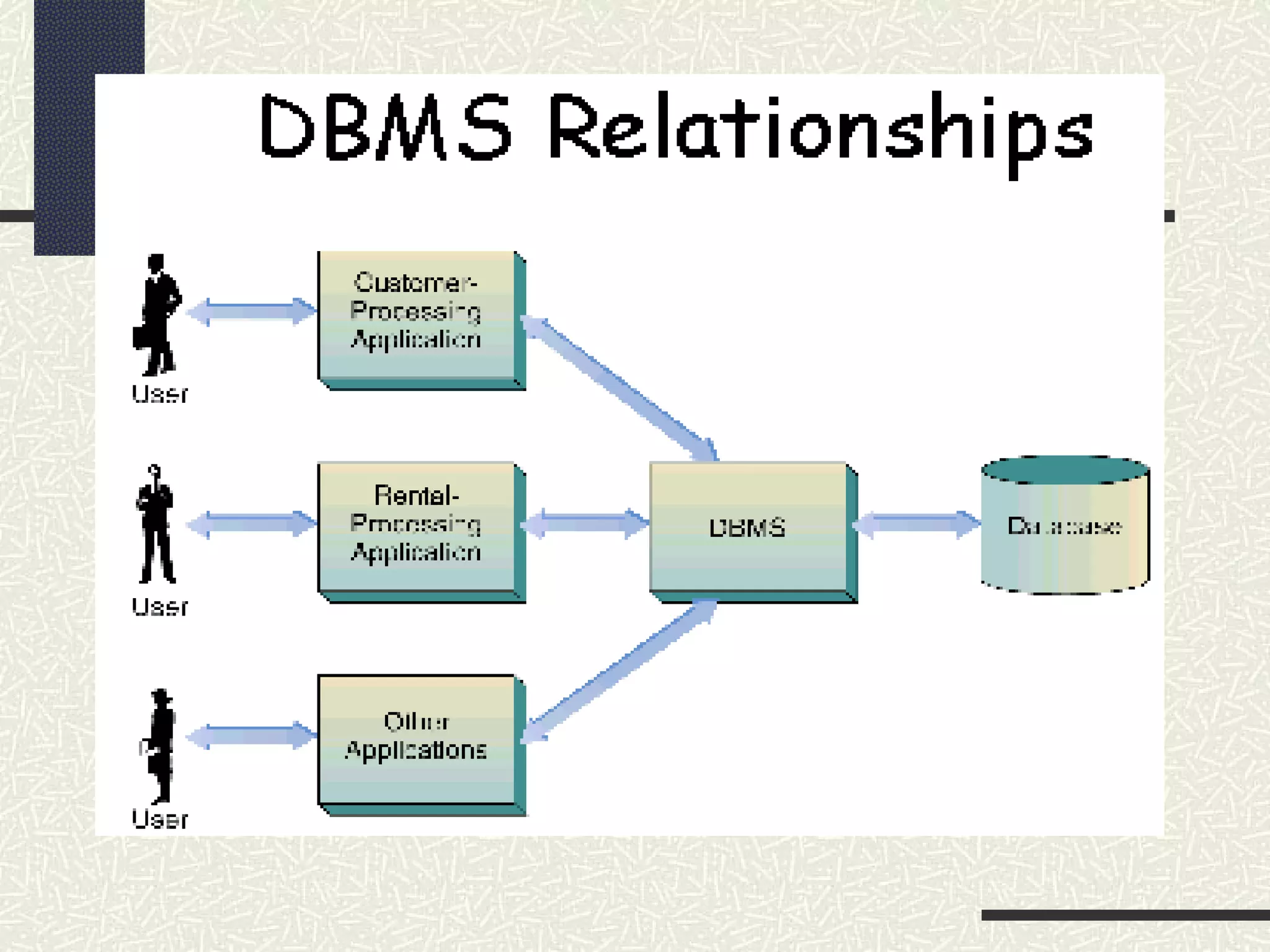
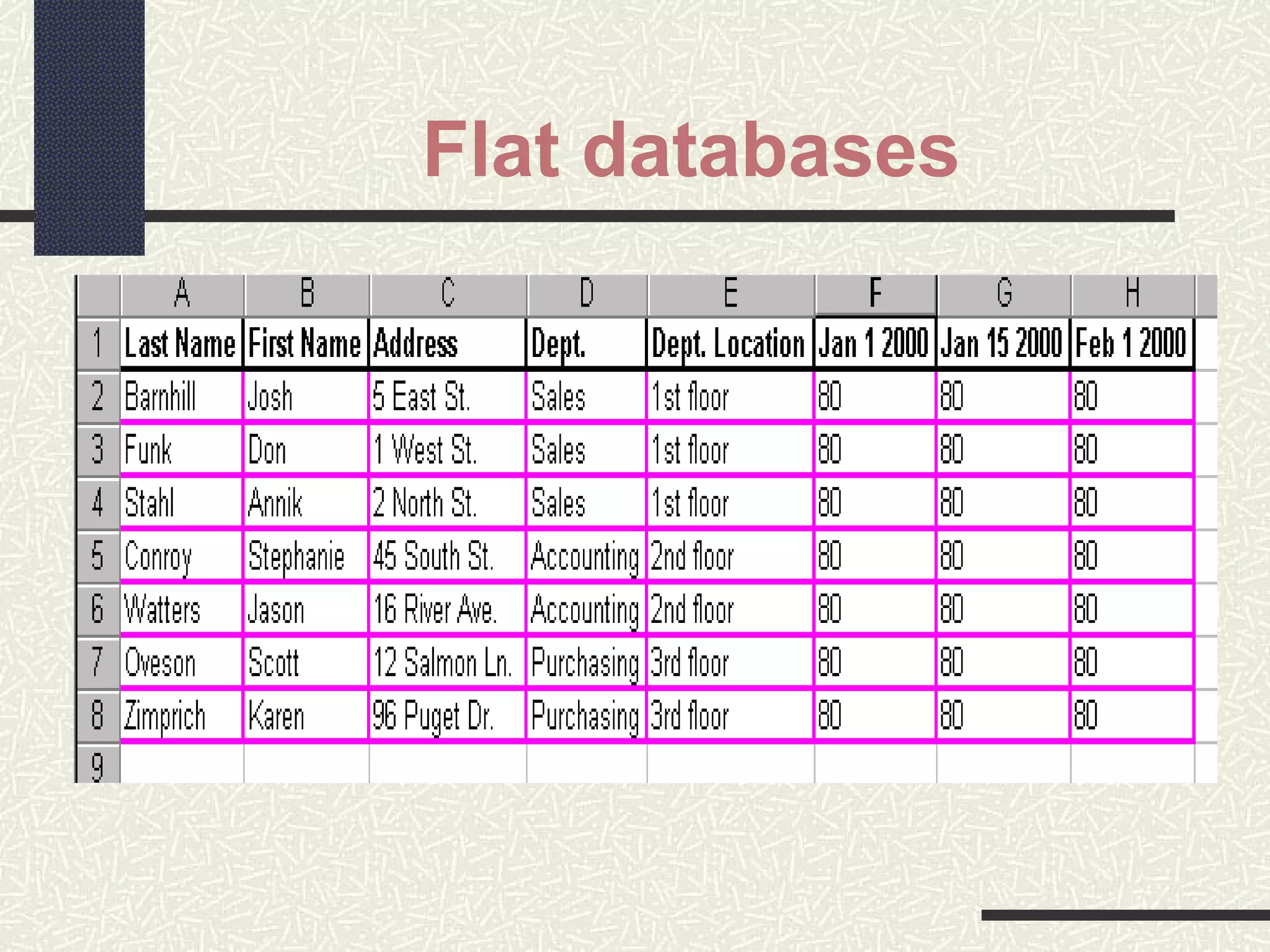
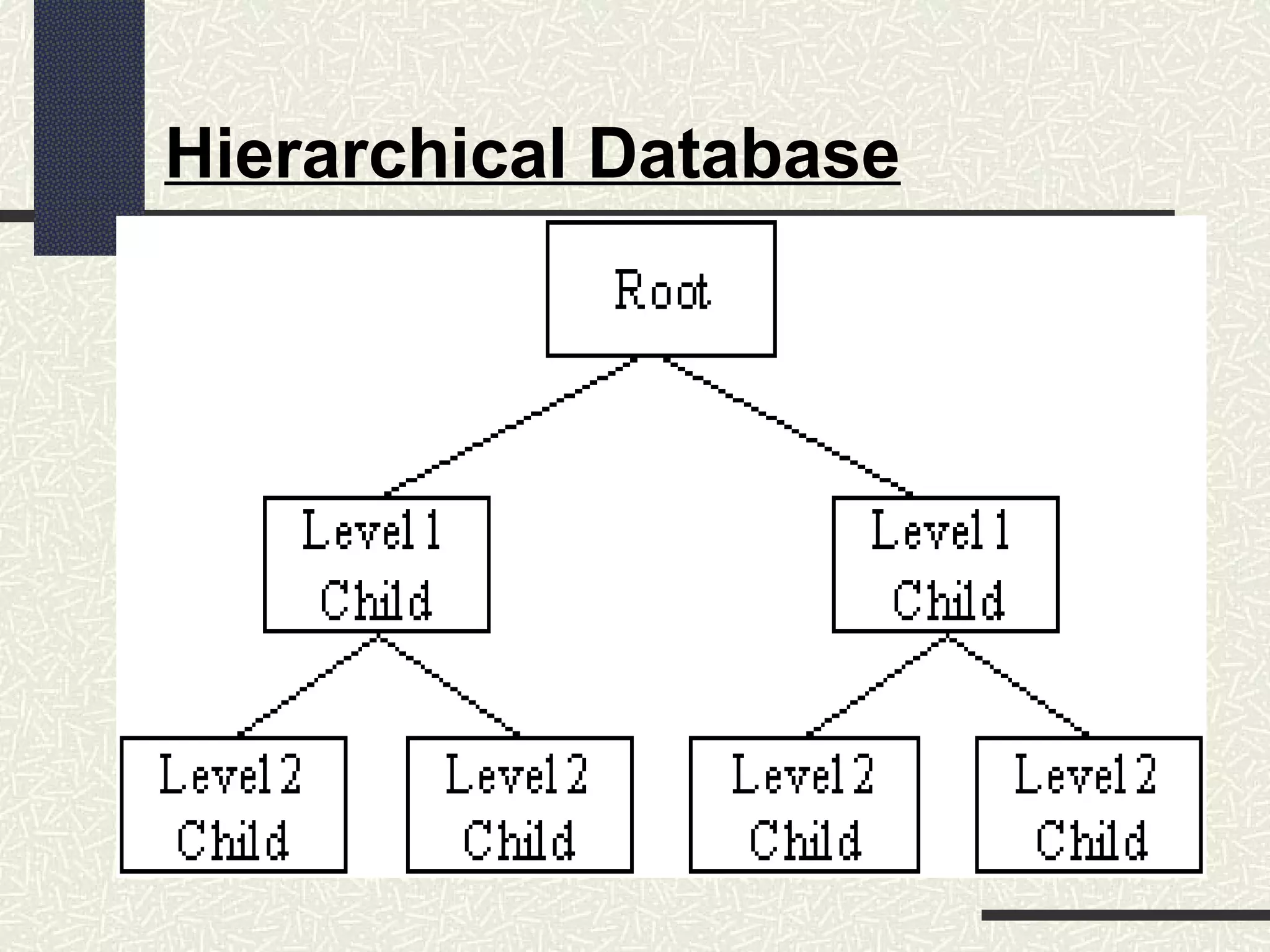
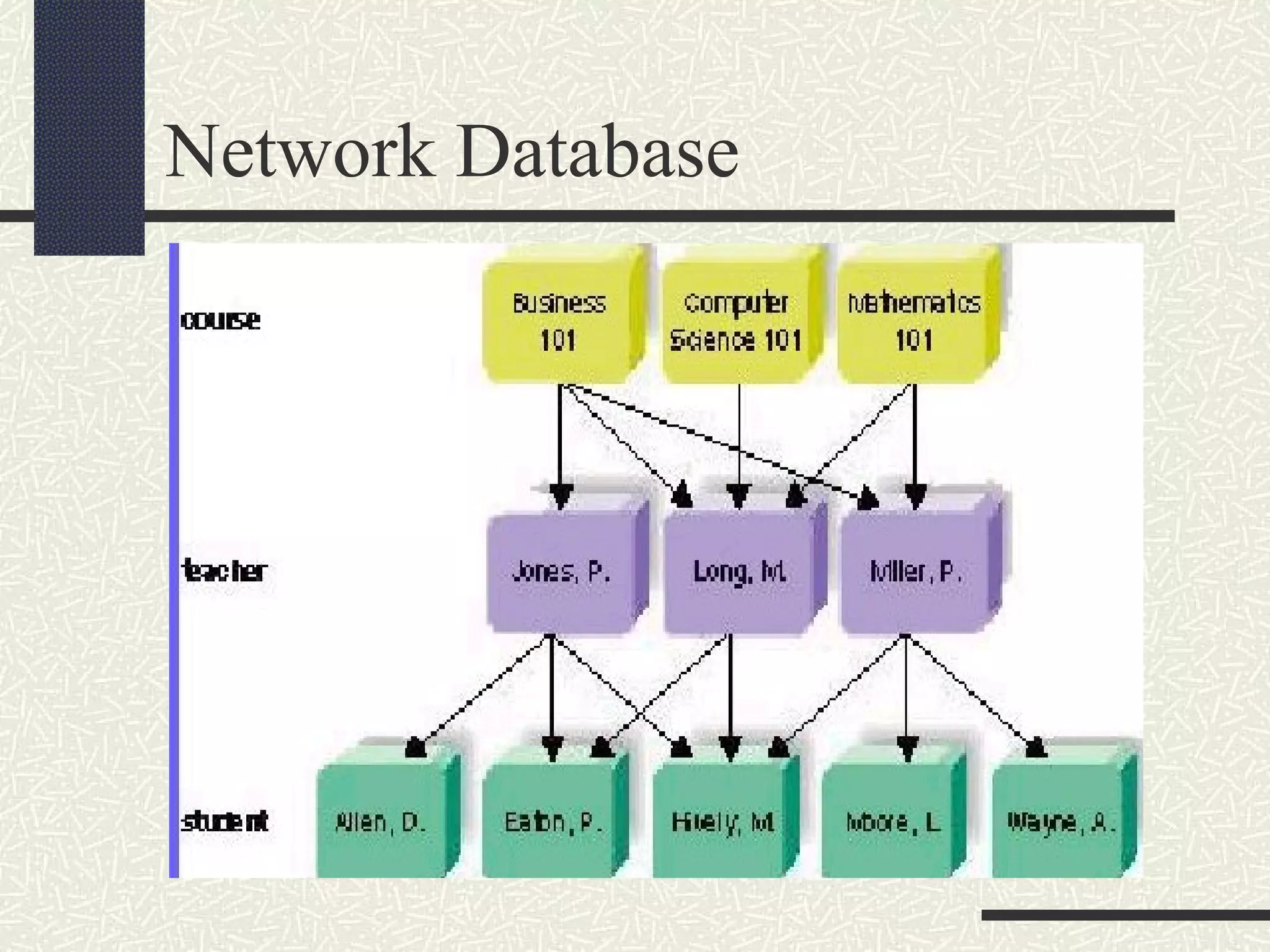
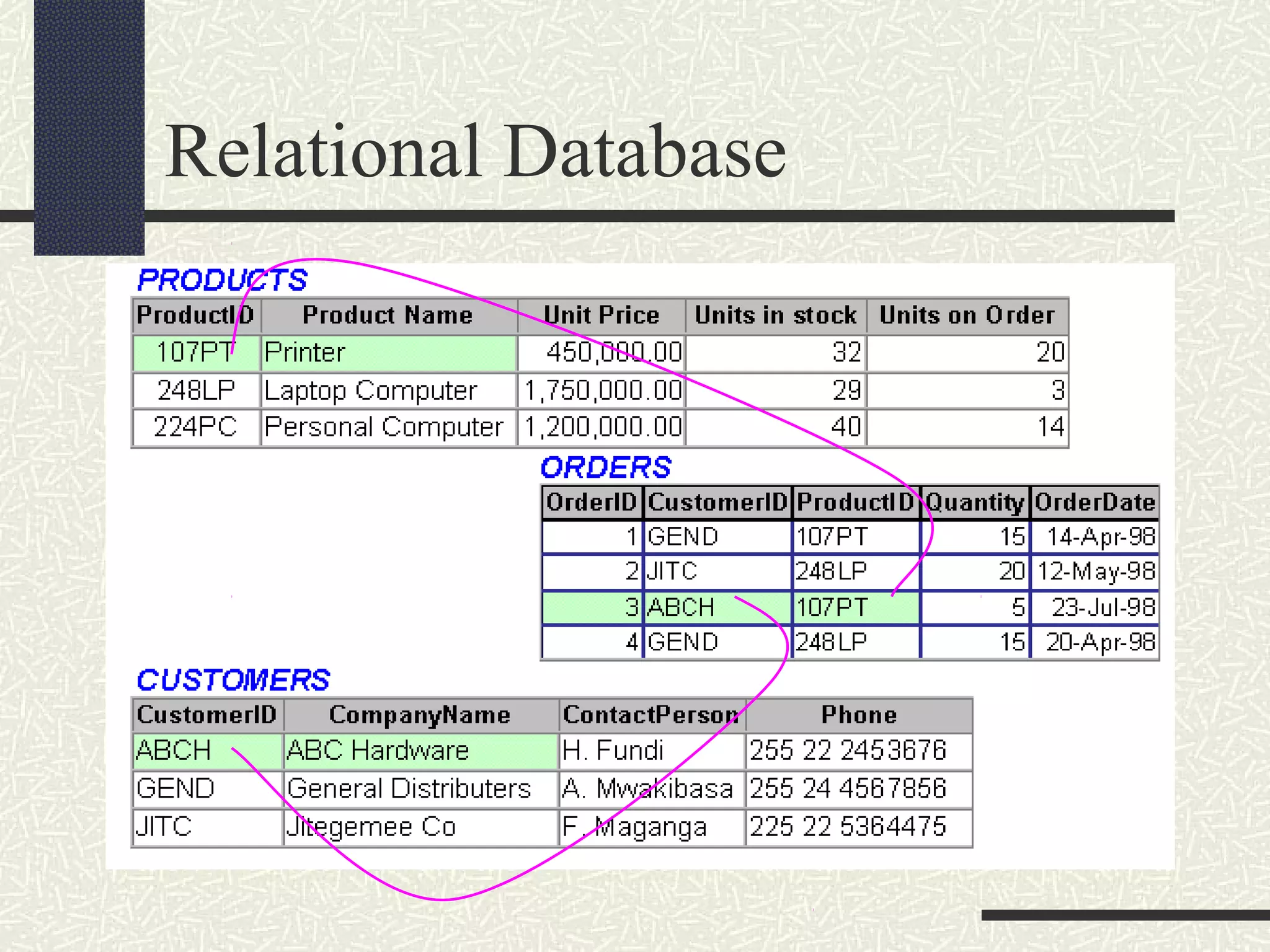
This document provides an introduction to database concepts. It defines what a database is and gives examples. It also defines key database terminology like data, fields, records, tables, and relationships. Additionally, it discusses the history of databases from manual systems to file processing systems to modern database management systems. DBMSs allow for centralized, organized data storage and retrieval and overcome many of the limitations of earlier data storage methods. The document also briefly describes different types of database models and relational database concepts like tables, primary keys, and foreign keys.