The document provides an overview of socket programming in Linux, explaining the fundamental concepts including socket types, communication domains, and the client/server model. It covers network addressing specifics for both MAC and IP addresses, as well as details about IPv4 addressing and subnetting. Additionally, it presents examples of socket programming through client and server code, illustrating the functionality of TCP and UDP protocols in network communications.
![ <sys/un.h> include file.
struct sockaddr_un {
sa_family_t sun_family; /* AF_UNIX */
char sun_path[]; /* pathname */
};
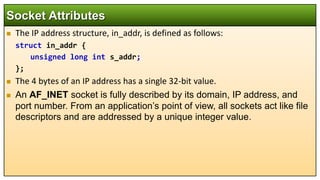
In the AF_INET domain, the address is specified using a structure called
sockaddr_in, defined in netinet/in.h, which contains at least these members:
struct sockaddr_in {
short int sin_family; /*AF_INET*/
unsigned short int sin_port; /*Port number*/
struct in_addr sin_addr; /*Internet address*/
};
Socket Attributes](https://image.slidesharecdn.com/ch15sockets-240517162755-6b21fc96/85/Linux-Systems-Prograramming-Unix-Domain-Internet-Domain-TCP-UDP-Socket-Programming-29-320.jpg)
![#include <sys/types.h>
#include <sys/socket.h>
#include <stdio.h>
#include <netinet/in.h>
#include <arpa/inet.h>
#include <unistd.h>
#include <stdlib.h>
#include <string.h>
int main(int argc, char *argv[]) {
int server_sockfd, client_sockfd;
int server_len, client_len;
struct sockaddr_in server_address;
struct sockaddr_in client_address;
char msg[1024], reply[]="Wa Elikum Salam";
if (argc !=2){
printf("Usege:%s Port_Number n",argv[0]);
exit(0);
}
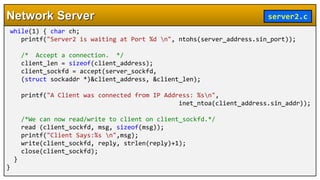
Network Server server2.c](https://image.slidesharecdn.com/ch15sockets-240517162755-6b21fc96/85/Linux-Systems-Prograramming-Unix-Domain-Internet-Domain-TCP-UDP-Socket-Programming-54-320.jpg)
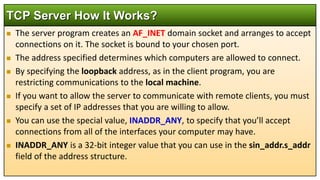
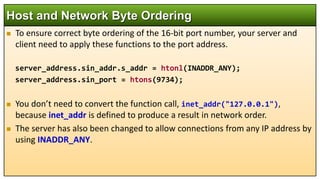
![/* Remove any old socket and create an unnamed socket for the server. */
server_sockfd = socket(AF_INET, SOCK_STREAM, 0);
/* Name the socket. */
server_address.sin_family = AF_INET;
server_address.sin_addr.s_addr = htonl(INADDR_ANY);
server_address.sin_port = htons(atoi(argv[1]));
server_len = sizeof(server_address);
bind(server_sockfd, (struct sockaddr *)&server_address, server_len);
/* Create a connection queue and wait for clients. */
listen(server_sockfd, 5);
Network Server server2.c](https://image.slidesharecdn.com/ch15sockets-240517162755-6b21fc96/85/Linux-Systems-Prograramming-Unix-Domain-Internet-Domain-TCP-UDP-Socket-Programming-55-320.jpg)
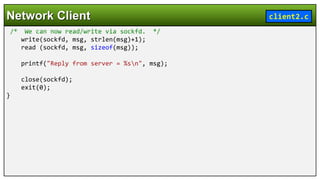
![#include <sys/types.h>
#include <sys/socket.h>
#include <stdio.h>
#include <netinet/in.h>
#include <arpa/inet.h>
#include <unistd.h>
#include <stdlib.h>
#include <string.h>
int main(int argc, char *argv[]) {
int sockfd; int len; char msg[512] = "Assalam O Alikum";
struct sockaddr_in address; int result;
if (argc!=3){
printf("Usage:%s Server_IP_Address Port_Numbern",
argv[0]);
printf("Usage:%s 192.168.10.7 8080n",argv[0]);
exit(0);
}
Network Client client2.c](https://image.slidesharecdn.com/ch15sockets-240517162755-6b21fc96/85/Linux-Systems-Prograramming-Unix-Domain-Internet-Domain-TCP-UDP-Socket-Programming-57-320.jpg)
![/* Create a socket for the client. */
sockfd = socket(AF_INET, SOCK_STREAM, 0);
/* Name the socket, as agreed with the server. */
address.sin_family = AF_INET;
address.sin_addr.s_addr = inet_addr(argv[1]);
address.sin_port = htons(atoi(argv[2]));
len = sizeof(address);
/* Now connect our socket to the server's socket. */
result = connect(sockfd,(struct sockaddr *)&address,len);
if(result == -1) {
perror("oops: client2");
exit(1);
}
Network Client client2.c](https://image.slidesharecdn.com/ch15sockets-240517162755-6b21fc96/85/Linux-Systems-Prograramming-Unix-Domain-Internet-Domain-TCP-UDP-Socket-Programming-58-320.jpg)

![#include <netinet/in.h>
#include <arpa/inet.h>
#include <unistd.h>
#include <netdb.h>
#include <stdio.h>
#include <stdlib.h>
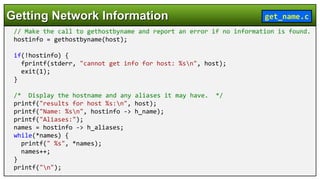
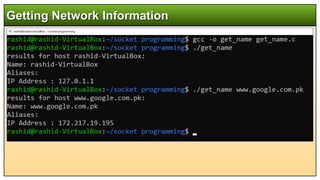
int main(int argc, char *argv[]){
char *host, **names, **addrs;
struct hostent *hostinfo;
/* Set the host in question to the argument supplied with
the getname call, or default to the user's machine. */
if(argc == 1) {
char myname[256];
gethostname(myname, 255); host = myname;
}
else
host = argv[1];
Getting Network Information get_name.c](https://image.slidesharecdn.com/ch15sockets-240517162755-6b21fc96/85/Linux-Systems-Prograramming-Unix-Domain-Internet-Domain-TCP-UDP-Socket-Programming-67-320.jpg)
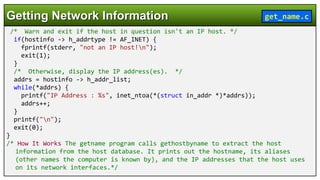
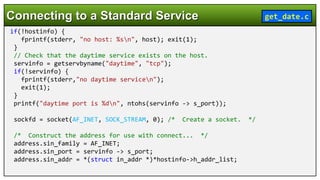
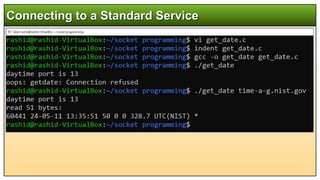
![#include <sys/socket.h>
#include <netinet/in.h>
#include <netdb.h>
#include <stdio.h>
#include <unistd.h>
#include <stdlib.h>
int main(int argc, char *argv[]) {
char *host; int sockfd; int len, result;
struct sockaddr_in address;
struct hostent *hostinfo;
struct servent *servinfo;
char buffer[128];
if(argc == 1)
host = "localhost";
else
host = argv[1];
//Find the host address and report an error if none is found.
hostinfo = gethostbyname(host);
Connecting to a Standard Service get_date.c](https://image.slidesharecdn.com/ch15sockets-240517162755-6b21fc96/85/Linux-Systems-Prograramming-Unix-Domain-Internet-Domain-TCP-UDP-Socket-Programming-71-320.jpg)
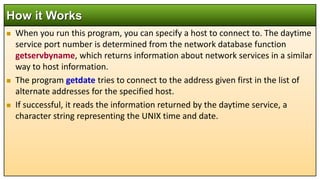
![len = sizeof(address);
// ...then connect and get the information.
result = connect(sockfd, (struct sockaddr *) &address, len);
if(result == -1) {
perror("oops: getdate"); exit(1);
}
result = read(sockfd, buffer, sizeof(buffer));
buffer[result] = '0';
printf("read %d bytes: %s", result, buffer);
close(sockfd);
exit(0);
}
Connecting to a Standard Service get_date.c](https://image.slidesharecdn.com/ch15sockets-240517162755-6b21fc96/85/Linux-Systems-Prograramming-Unix-Domain-Internet-Domain-TCP-UDP-Socket-Programming-73-320.jpg)
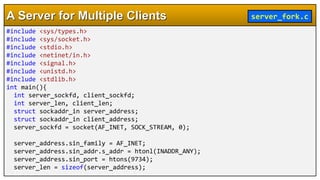

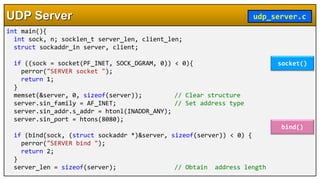
![#include <sys/ioctl.h>
#include <stdio.h>
#include <string.h>
#include <ctype.h>
#include <unistd.h>
#include <stdlib.h>
#include <signal.h>
#include <wait.h>
#include <sys/types.h>
#include <sys/socket.h>
#include <sys/un.h>
#include <netdb.h>
static char buf[BUFSIZ]; // Buffer for messages
UDP Server udp_server.c](https://image.slidesharecdn.com/ch15sockets-240517162755-6b21fc96/85/Linux-Systems-Prograramming-Unix-Domain-Internet-Domain-TCP-UDP-Socket-Programming-84-320.jpg)
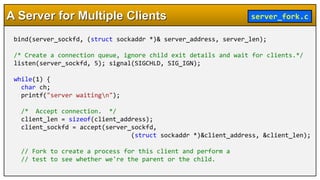
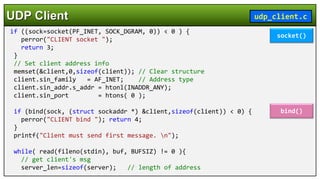
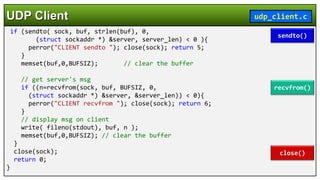
![#include <stdio.h>
#include <ctype.h>
#include <unistd.h>
#include <stdlib.h>
#include <signal.h>
#include <wait.h>
#include <sys/types.h>
#include <sys/socket.h>
#include <sys/un.h>
#include <netdb.h>
static char buf[BUFSIZ]; // Buffer for messages
UDP Client udp_client.c](https://image.slidesharecdn.com/ch15sockets-240517162755-6b21fc96/85/Linux-Systems-Prograramming-Unix-Domain-Internet-Domain-TCP-UDP-Socket-Programming-88-320.jpg)
![int main(int argc, char *argv[]) {
int sock, n;
socklen_t server_len;
struct sockaddr_in server, client;
struct hostent *host; // For host information
if ( argc < 3 ){ // We need server name & port #
printf("usage: %s server_name port_no n",argv[0]);
return 1;
} // Server information
if (!(host=gethostbyname(argv[1]))){
perror("CLIENT gethostname ");
return 2;
} // Set server address info
memset(&server, 0, sizeof(server)); // Clear structure
server.sin_family = AF_INET; // Address type
memcpy(&server.sin_addr, host->h_addr,host->h_length);
server.sin_port = htons(atoi(argv[2]));
UDP Client udp_client.c
gethostbyname()](https://image.slidesharecdn.com/ch15sockets-240517162755-6b21fc96/85/Linux-Systems-Prograramming-Unix-Domain-Internet-Domain-TCP-UDP-Socket-Programming-89-320.jpg)
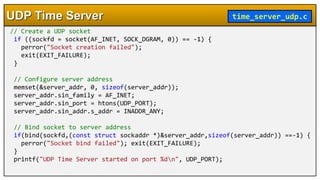
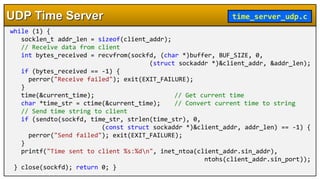
![#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <time.h>
#include <unistd.h>
#include <arpa/inet.h>
#define UDP_PORT 13
#define BUF_SIZE 1024
int main() {
int sockfd;
struct sockaddr_in server_addr, client_addr;
char buffer[BUF_SIZE];
time_t current_time;
UDP Time Server time_server_udp.c](https://image.slidesharecdn.com/ch15sockets-240517162755-6b21fc96/85/Linux-Systems-Prograramming-Unix-Domain-Internet-Domain-TCP-UDP-Socket-Programming-93-320.jpg)
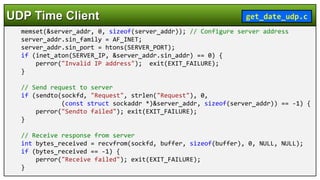
![#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <unistd.h>
#include <arpa/inet.h>
#define SERVER_IP "127.0.0.1" // Change to the IP address of your UDP time server
#define SERVER_PORT 13
int main() {
int sockfd;
struct sockaddr_in server_addr;
char buffer[1024];
if ((sockfd = socket(AF_INET, SOCK_DGRAM, 0)) == -1) {// Create a UDP socket
perror("Socket creation failed");
exit(EXIT_FAILURE);
}
UDP Time Client get_date_udp.c](https://image.slidesharecdn.com/ch15sockets-240517162755-6b21fc96/85/Linux-Systems-Prograramming-Unix-Domain-Internet-Domain-TCP-UDP-Socket-Programming-96-320.jpg)
![// Null-terminate the received data to print it as a string
buffer[bytes_received] = '0';
// Print the received time from the server
printf("Received time from server: %sn", buffer);
// Close the socket
close(sockfd);
return 0;
}
UDP Time Client get_date_udp.c](https://image.slidesharecdn.com/ch15sockets-240517162755-6b21fc96/85/Linux-Systems-Prograramming-Unix-Domain-Internet-Domain-TCP-UDP-Socket-Programming-98-320.jpg)
