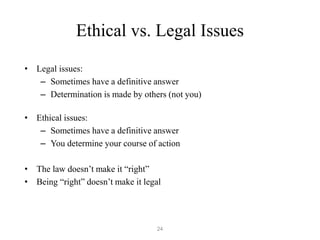
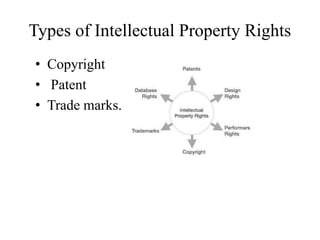
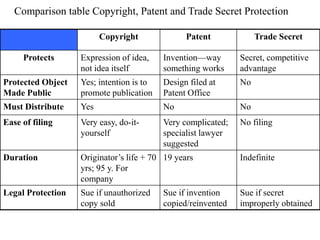
This document discusses various legal, privacy, and ethical issues related to computer security. It begins by explaining the differences between legal and ethical issues, noting that legal issues have definitive answers determined by others, while ethical issues require determining your own course of action. The document then provides overviews of intellectual property rights like copyrights, patents, and trademarks. It explains what types of works copyright protects, how long copyright lasts, and what constitutes infringement. It also discusses how patents protect inventions and processes, not ideas. Finally, the document compares key aspects of copyright, patent, and trade secret protection.