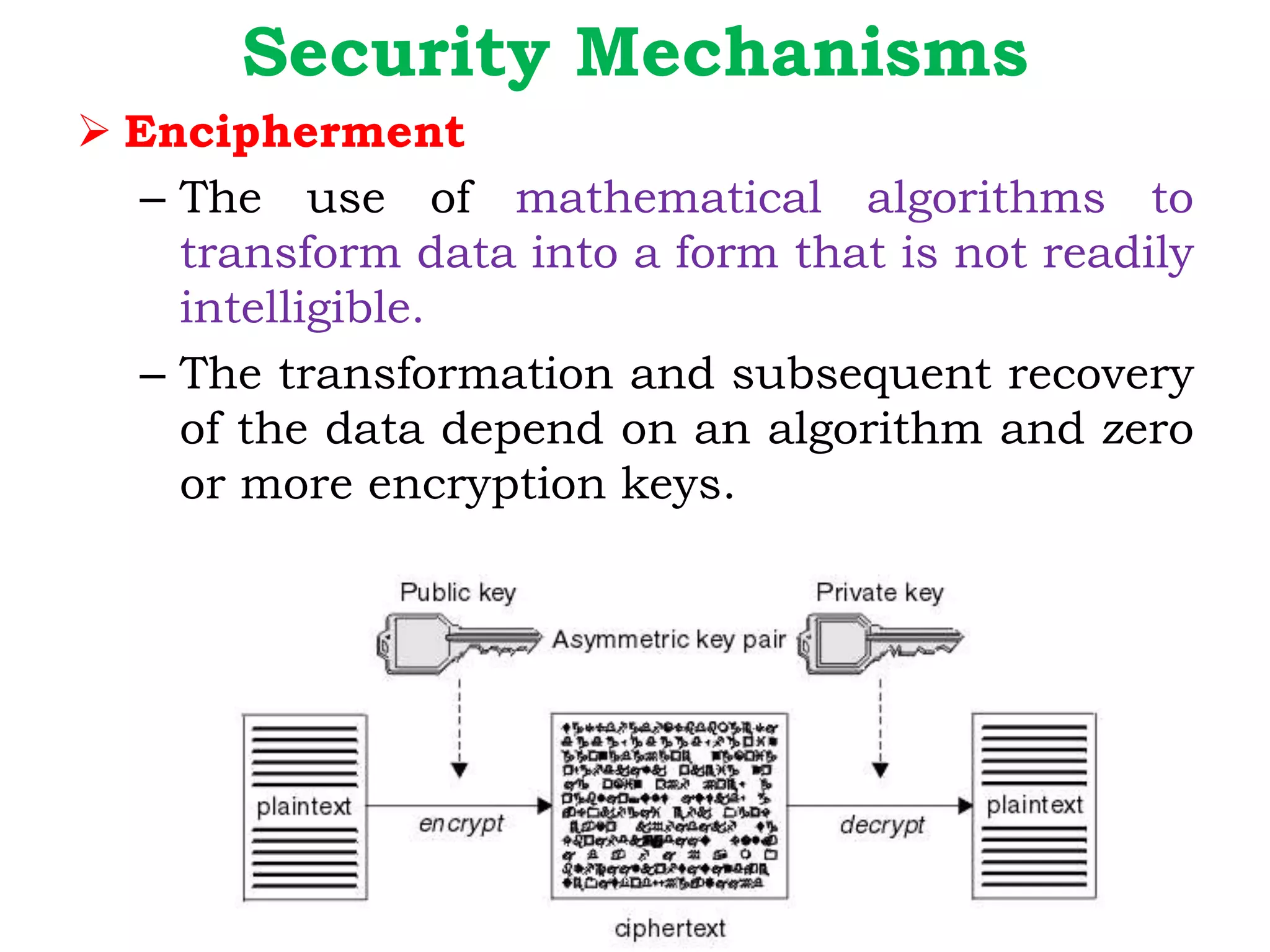
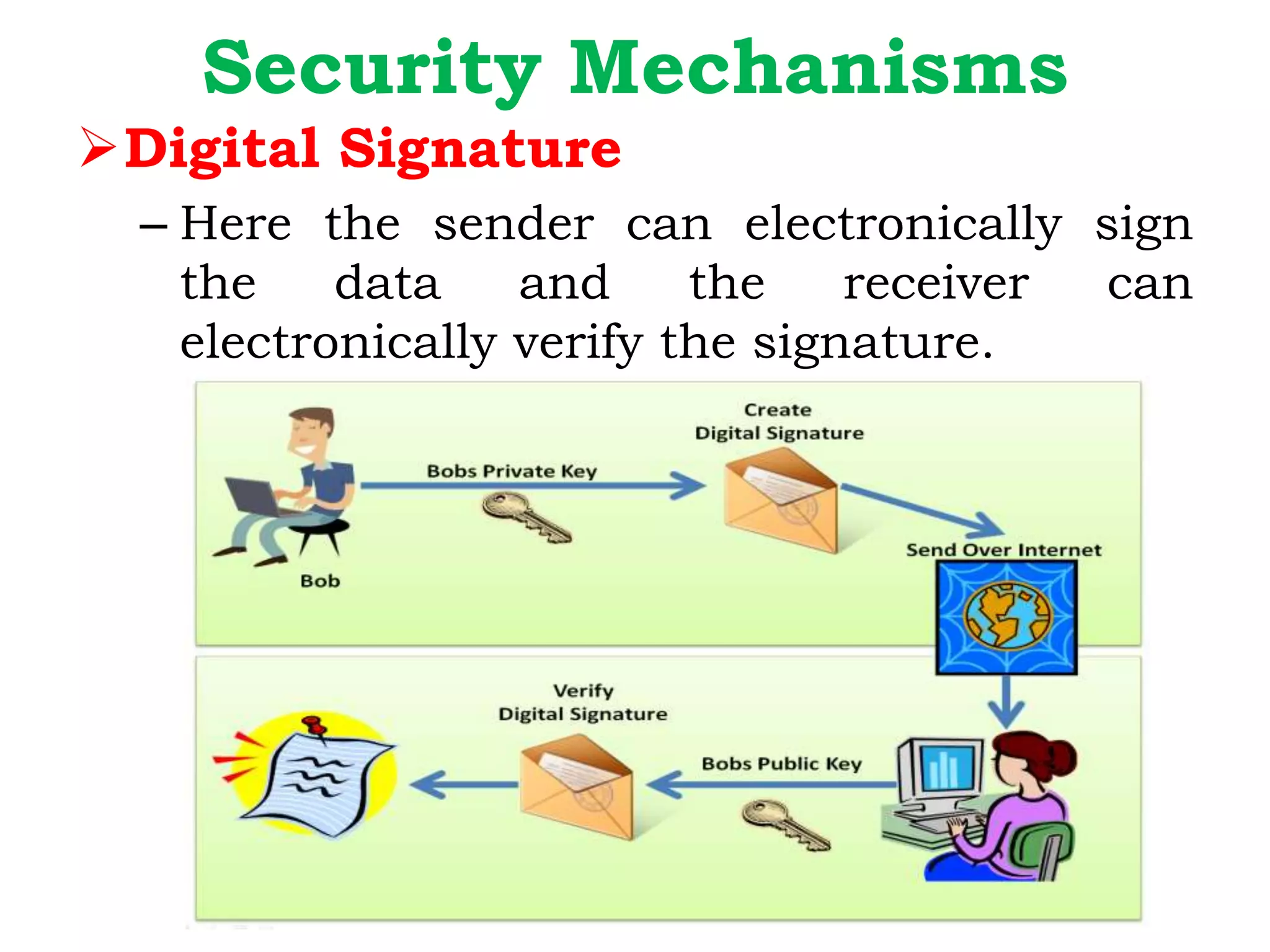
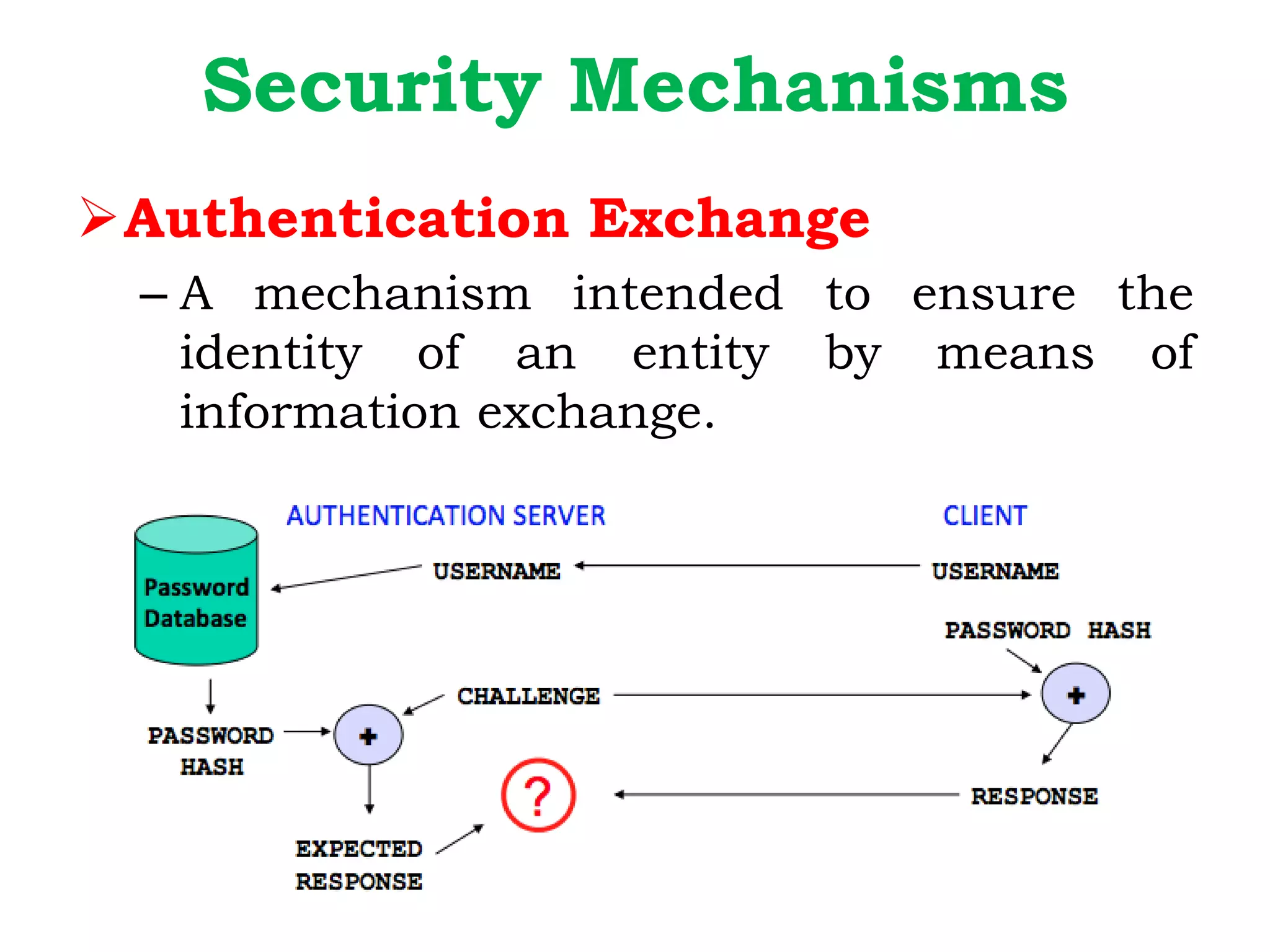
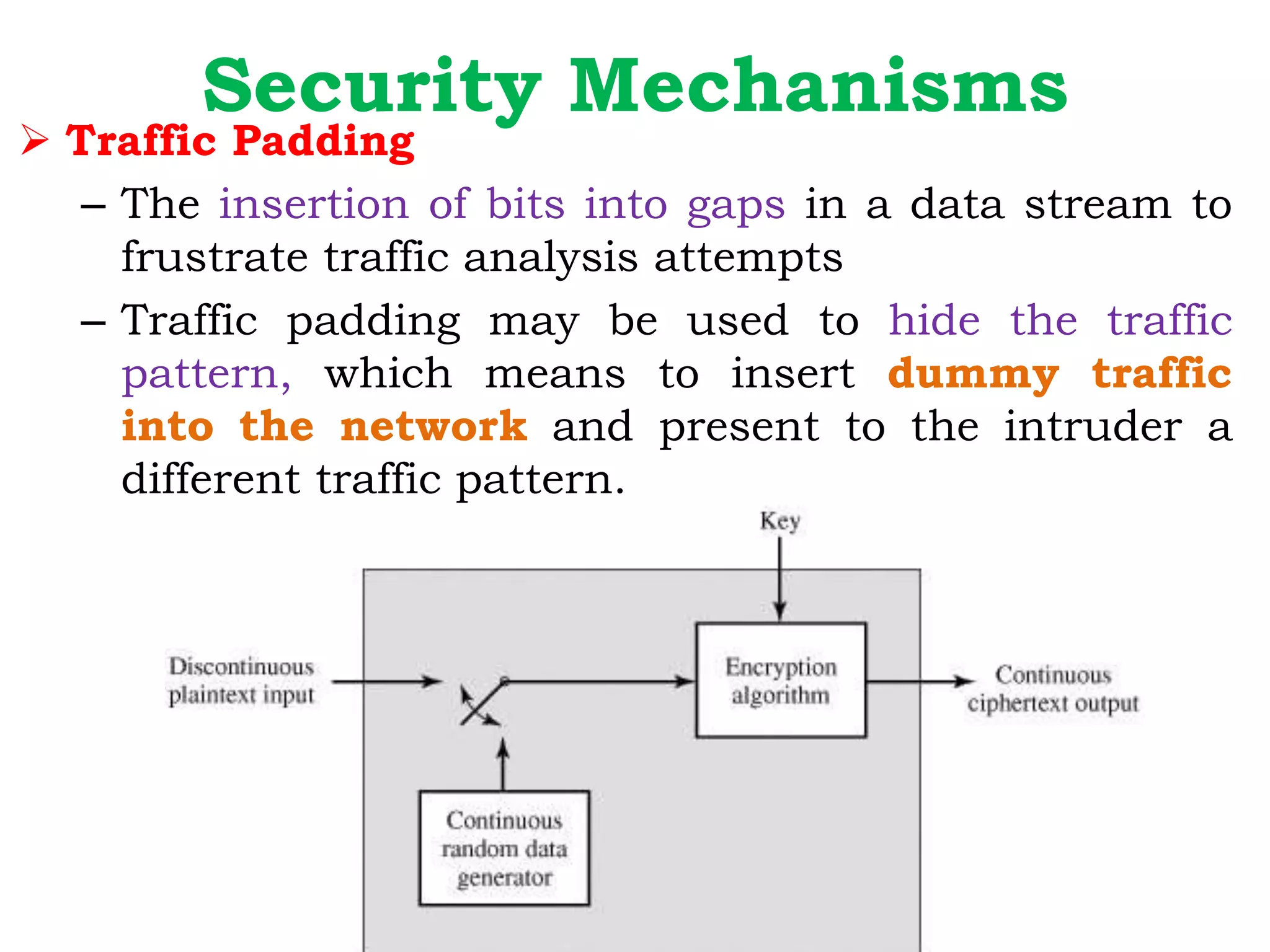
This document provides information about the CS8792 CRYPTOGRAPHY & NETWORK SECURITY course. It discusses cryptography, the course outcomes, syllabus, and key concepts in cryptography including symmetric encryption, asymmetric encryption, data integrity algorithms, and authentication protocols. It also covers essential network and computer security requirements, legal and ethical issues, security policies, OSI security architecture including security attacks, mechanisms, and services.


![The U.S. Department of Justice [DOJ]
categorizes computer crime based on
the role that the computer plays in the
criminal activity, as follows:
Computers as targets
Computers as storage devices
Computers as communications tools](https://image.slidesharecdn.com/cnsunit1-slide-220111071646/75/CRYPTOGRAPHY-NETWORK-SECURITY-unit-1-9-2048.jpg)