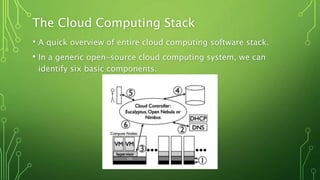
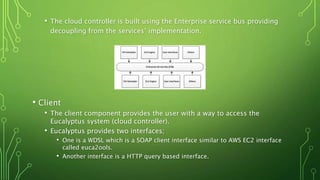
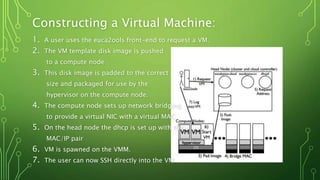
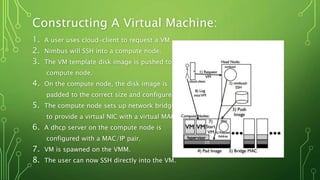
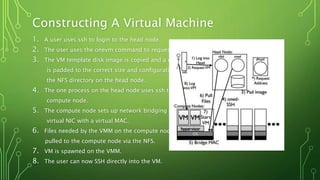
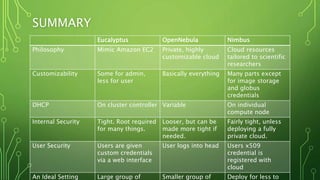
The document discusses three open-source cloud computing platforms: Eucalyptus, Nimbus, and OpenNebula, detailing their architecture, functionalities, and suitability for various applications. Eucalyptus is designed for Infrastructure as a Service (IaaS) with components like cloud and storage controllers, while Nimbus focuses on leasing remote resources for scientific applications. OpenNebula emphasizes centralization and customizability for private clouds, allowing users to configure virtual machines via an SSH-accessed head node.