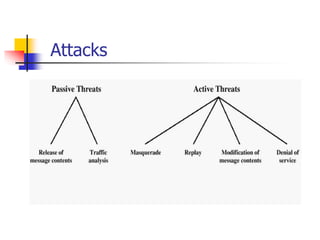
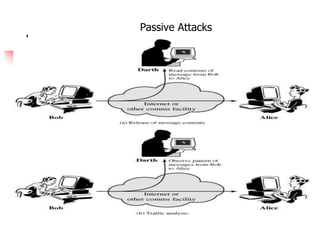
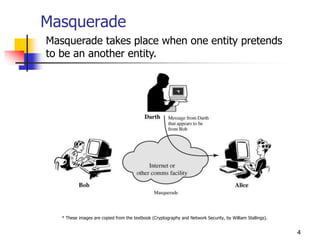
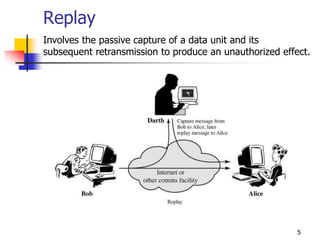
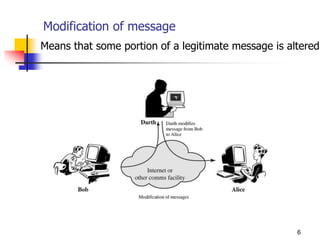
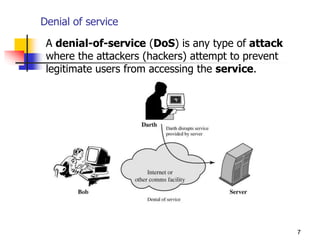
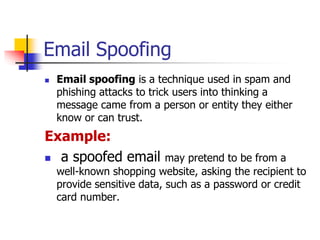
This document discusses different types of cyber attacks including passive attacks like eavesdropping and masquerading, active attacks like denial of service, and methods attackers use like spoofing, backdoors, brute force attacks, and dictionary attacks. It provides details on how each attack compromises security through unauthorized access, modification of data, denial of service, or repudiation.