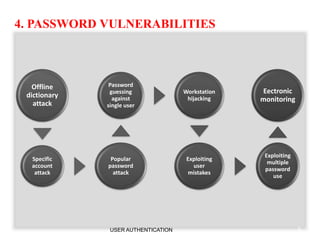
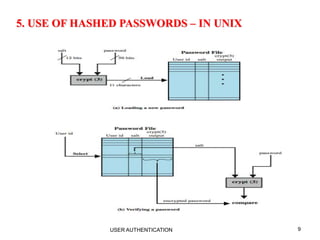
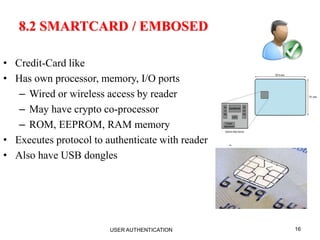
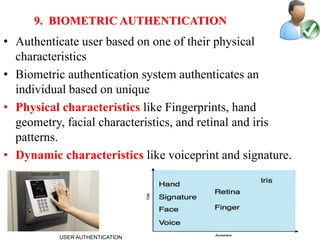
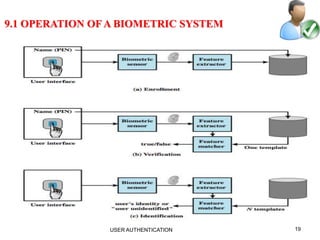
The document discusses user authentication, a fundamental security process for verifying identities in systems. It covers various means of authentication, including passwords, tokens, and biometrics, detailing their vulnerabilities and advantages. Techniques for enhancing password security and the operation of biometric systems are also explored.