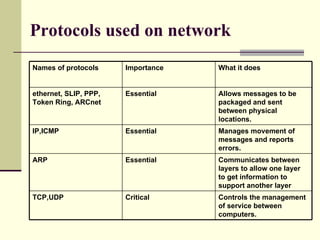
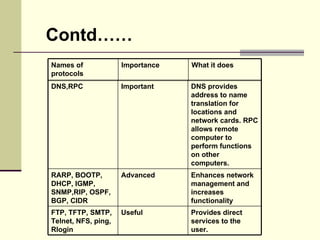
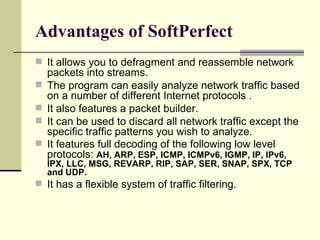
This document discusses network protocol analyzers. It describes what a network protocol analyzer is and some of its common uses, such as analyzing network problems, detecting intrusions, and monitoring network usage. It then lists some important network protocols like TCP, UDP, IP, and Ethernet and what they are used for. The document goes on to describe several popular network protocol analyzer tools, including Wireshark, Snort, Netcat, and Tcpdump. It provides more details on the Softperfect network analyzer tool, highlighting advantages like its ability to defragment packets and filter traffic.