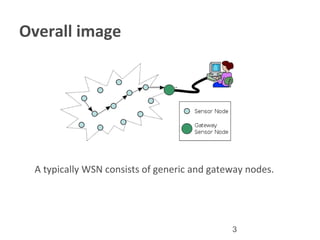
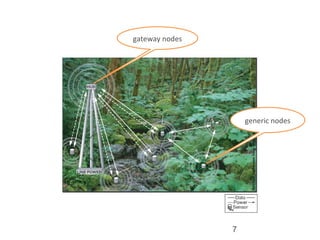
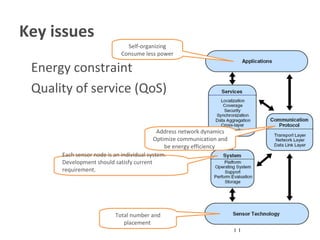
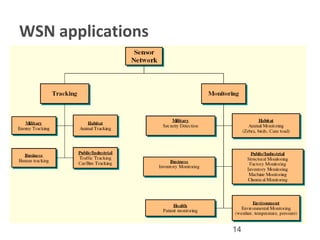
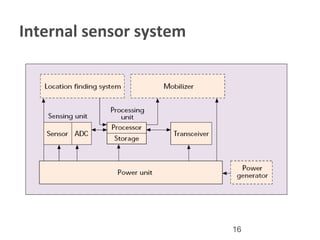
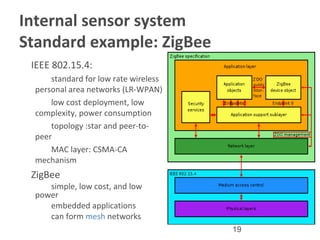
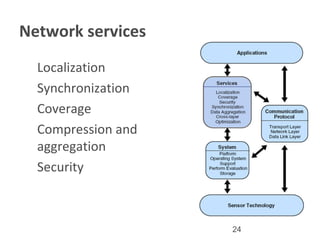
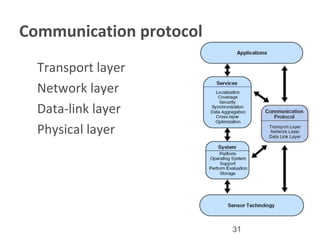
Wireless sensor networks consist of distributed sensors that monitor conditions like temperature and sound and transmit data to a central location. They have two types - structured networks which are pre-planned and unstructured which are randomly deployed. The document reviews issues in wireless sensor networks like energy constraints and quality of service. It also discusses network services, internal sensor systems, applications, and communication protocols. Open research areas are identified in localization, coverage, security, cross-layer optimization and mobility support to improve energy efficiency and performance.