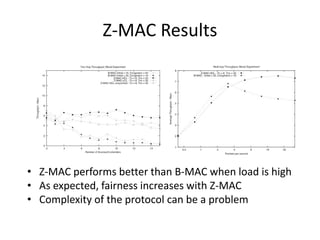
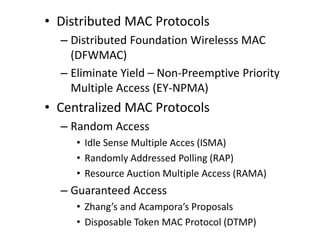
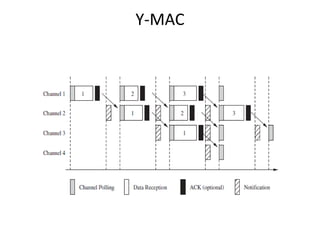
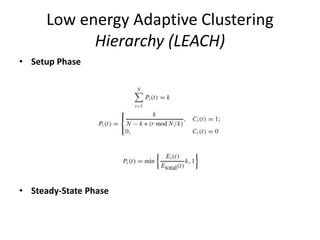
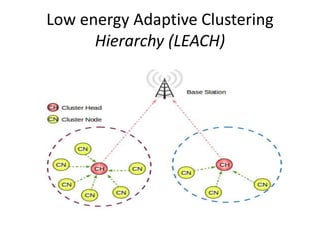
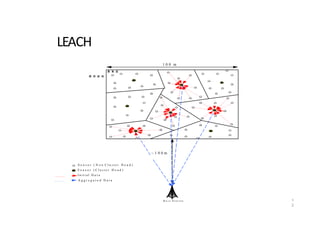
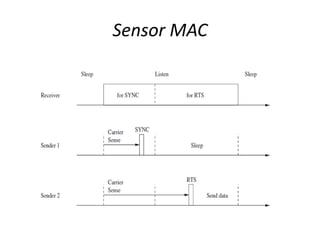
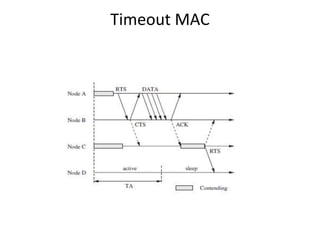
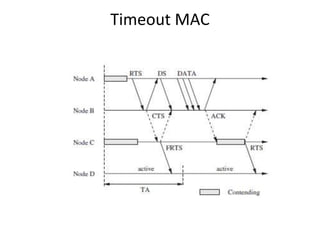
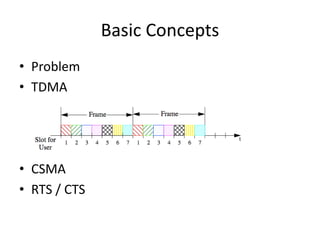
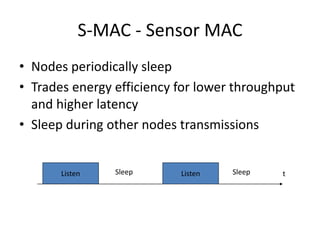
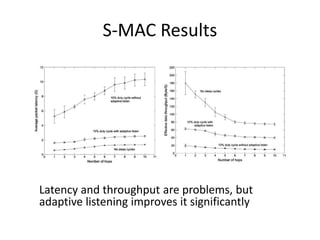
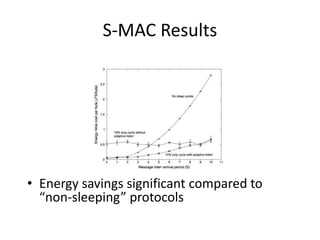
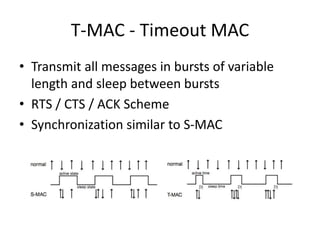
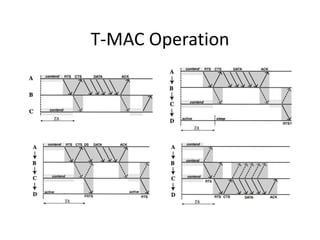
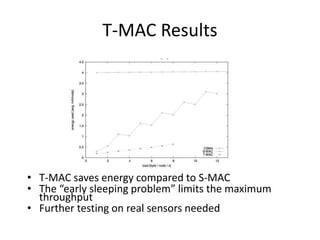
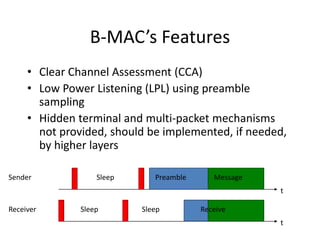
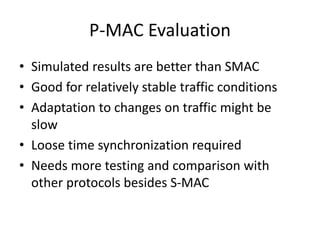
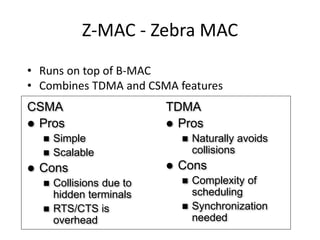
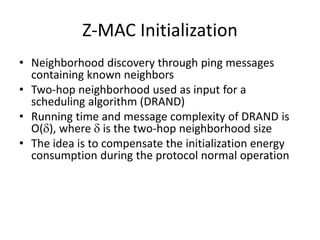
This document provides an overview of various medium access control (MAC) protocols for wireless sensor networks. It discusses distributed and centralized MAC protocols, including DFWMAC, EY-NPMA, ISMA, RAP, RAMA, Zhang's and Acampora's proposals, and DTMP. It also covers hybrid access protocols like RRA, PRMA, RRA-ISA, DQRUMA, and MASCARA. Additionally, it summarizes MAC protocols like S-MAC, T-MAC, B-MAC, P-MAC, Y-MAC, and Z-MAC and discusses their key characteristics and performance results.
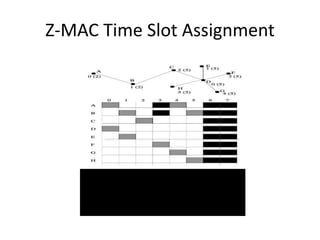
![Z-MAC Transmission Control
The Transmission Rule:
• If owner of slot
– Take a random backoff within To
– Run CCA and, if channel is clear, transmit
• Else
– Wait for To
– Take a random backoff within [To,Tno]
– Run CCA and, if channel is clear, transmit](https://image.slidesharecdn.com/wsnprotocols-220109032009/85/Wsn-protocols-69-320.jpg)