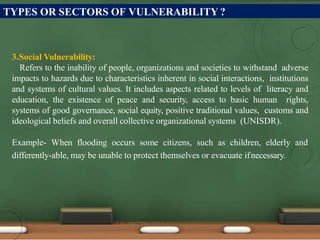
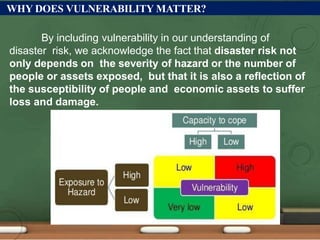
This document defines vulnerability and discusses it from different perspectives. Vulnerability refers to the susceptibility of individuals, communities, or systems to harm from hazards. It is determined by physical, social, economic, and environmental factors that influence the ability to prepare for, respond to, and recover from disasters. The document outlines four main types of vulnerability: physical, economic, social, and environmental. Understanding vulnerability is important for assessing disaster risk. Approaches to reducing vulnerability include building codes, insurance, economic diversity, awareness raising, and preparedness measures.