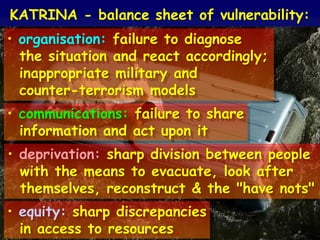
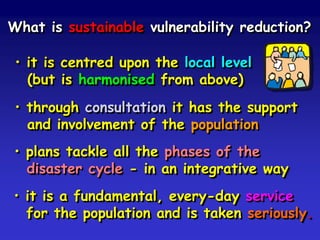
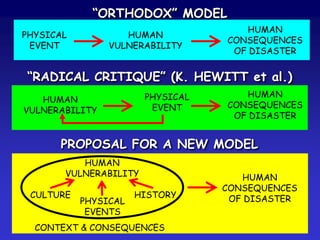
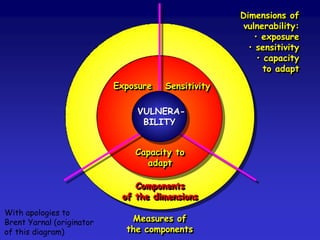
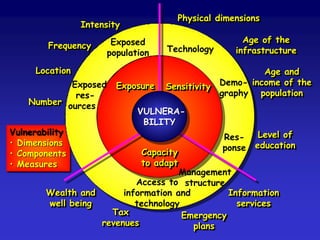
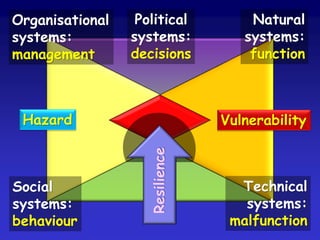
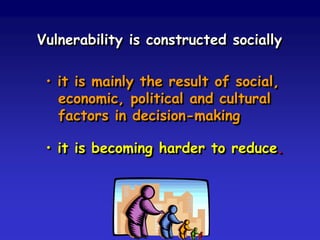
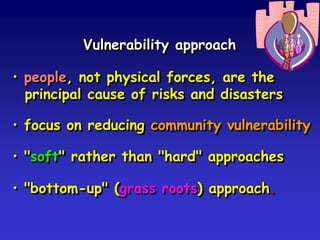
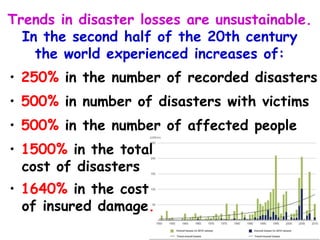
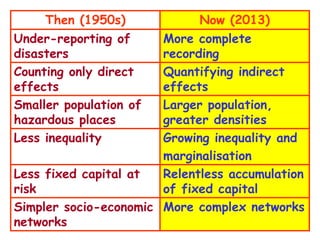
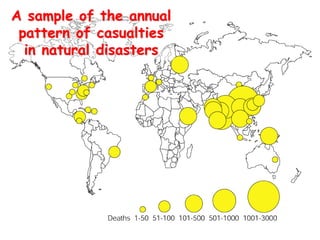
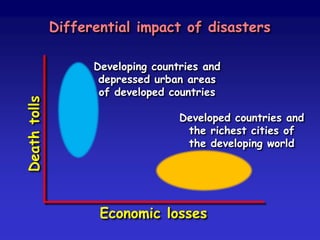
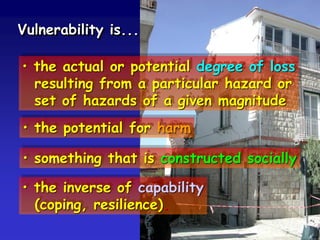
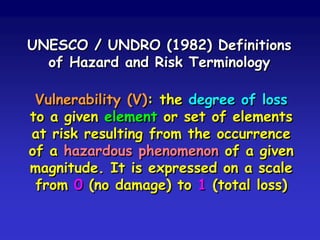
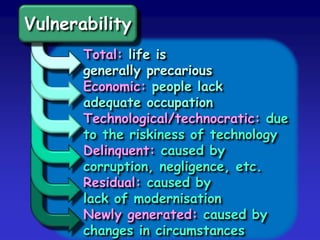
The document discusses the concept of vulnerability analysis. It begins by outlining the components of risk such as magnitude, frequency, and duration of hazards. It then examines how vulnerability is socially constructed and influenced by economic, political, and cultural factors. Trends show disasters are increasing in number and cost. The document explores how vulnerability has changed from the 1950s to now due to factors like population growth, urbanization, and inequality. It provides definitions of vulnerability and discusses approaches to reducing vulnerability through community-focused, bottom-up methods. The conclusion suggests disaster risk reduction programs aim to be sustainable and integrated across all phases of the disaster cycle.

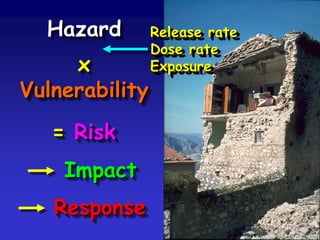
![(Hazard x Vulnerability x Exposure)
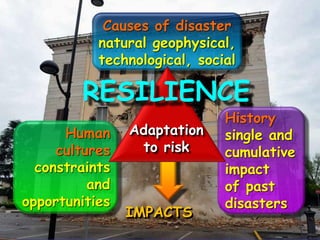
Resilience
= Risk
[ → Impact → Response]
Hazard x (Vulnerability / Resilience)
[x Exposure]
= Risk
[ → Impact → Response]
....alternatively:-](https://image.slidesharecdn.com/vulnerability-090910042904-phpapp02/85/Vulnerability-to-Disasters-18-320.jpg)
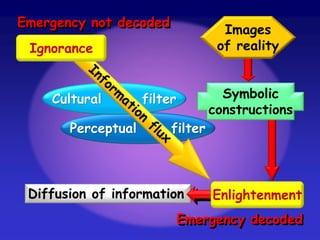
![Long term
Short term
Emic components
Etic components
METAMORPHOSIS
OF CULTURE
Experiences of culture
[mass-media and consumer culture]
Accumulated cultural traits and beliefs
Inherited cultural background
Ideological
(non-scientific)
interpretations
of disaster
Learned
(scientific)
interpretations
of disaster](https://image.slidesharecdn.com/vulnerability-090910042904-phpapp02/85/Vulnerability-to-Disasters-26-320.jpg)

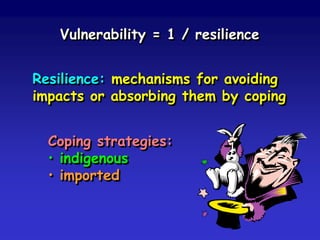
![What is resilience [resiliency]?
• a combination of resistance and
adaptation (coping, capacity, capability)
• ability to maintain livelihoods and tenor
of life in the face of disaster shocks
• local autonomy and self-sufficiency.](https://image.slidesharecdn.com/vulnerability-090910042904-phpapp02/85/Vulnerability-to-Disasters-36-320.jpg)






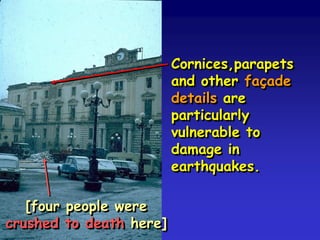





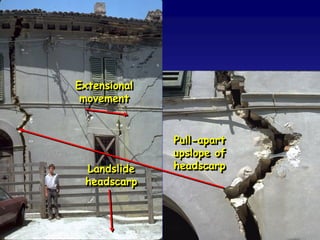



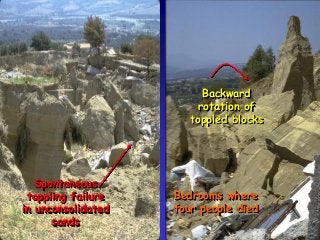
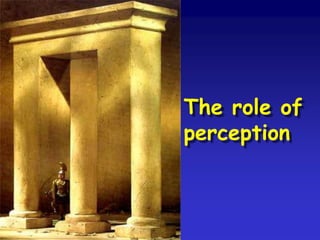
![Cornices,parapets
and other façade
details are
particularly
vulnerable to
damage in
earthquakes.
[four people were
crushed to death here]](https://image.slidesharecdn.com/vulnerability-090910042904-phpapp02/85/Vulnerability-to-Disasters-80-320.jpg)