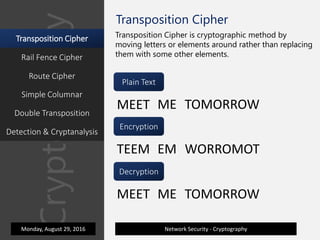
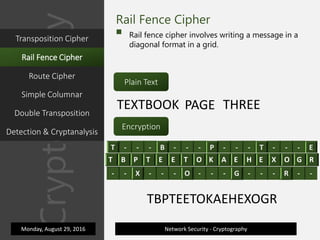
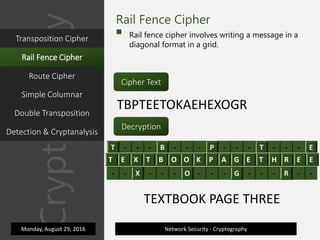
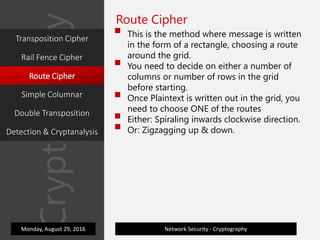
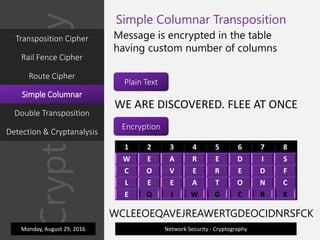
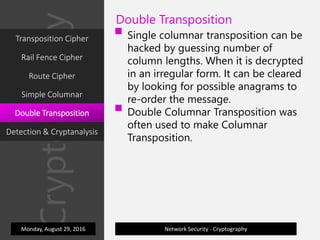
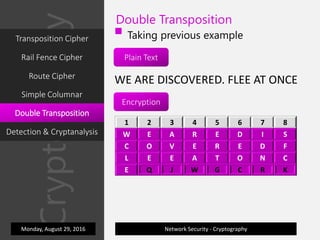
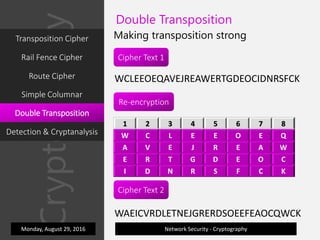
1) The document discusses various transposition ciphers including the rail fence cipher, route cipher, simple columnar transposition, and double transposition cipher. It explains how each cipher works through encrypting and decrypting sample messages.
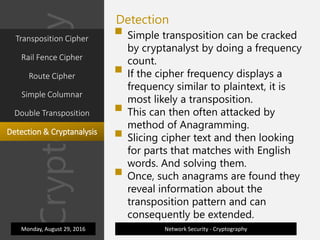
2) Detection methods for transposition ciphers are also covered, such as frequency analysis and finding anagrams in the ciphertext. Simpler transposition ciphers can be vulnerable to these kinds of cryptanalysis techniques.
3) Genetic algorithms are mentioned as a way for cryptanalysts to find the most likely decryption key through probability calculations.