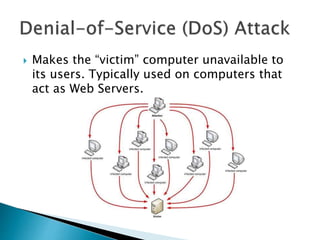
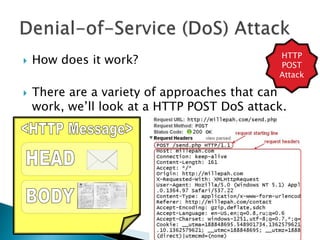
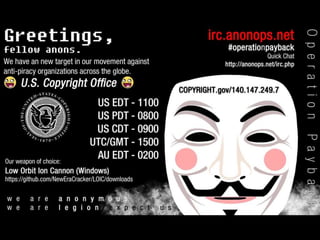
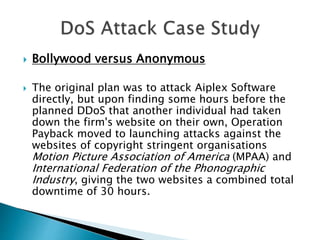
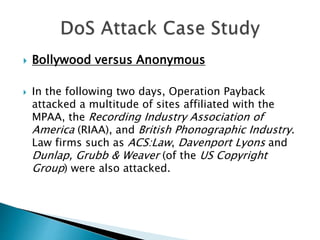
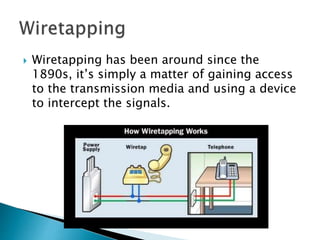
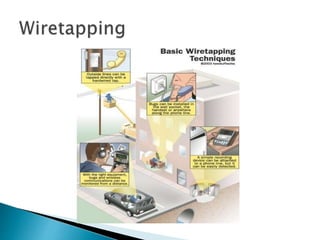
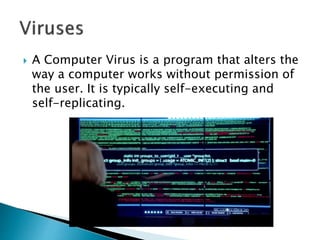
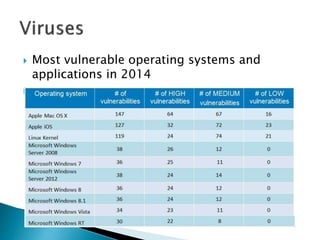
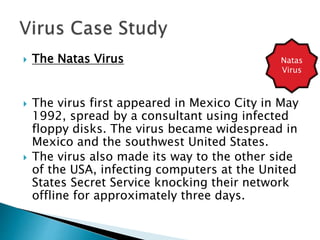
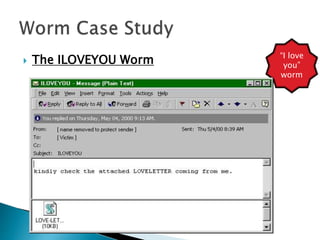
The document discusses various types of computer security threats including denial-of-service (DoS) attacks, wiretapping, viruses, worms, and trojans. It provides examples of each type of threat and how they work, such as how a HTTP POST DoS attack can overload a server with slow connections. The document also discusses the conflict between Bollywood and the hacktivist group Anonymous over piracy and retaliation through DDoS attacks. Finally, it covers computer viruses in more detail, describing different categories like boot sector, file infector, macro, multipartite, and polymorphic viruses.