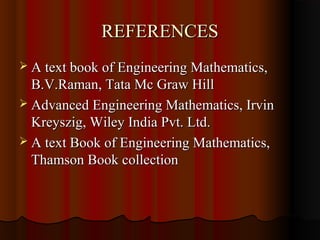
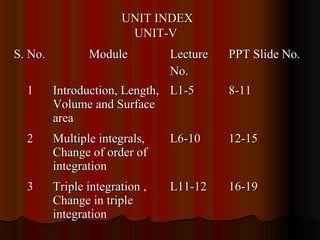
The document outlines the contents of a Mathematics-I course including ordinary differential equations, linear differential equations, mean value theorems, functions of several variables, curvature, applications of integration, multiple integrals, series and sequences, vector differentiation and integration. It provides textbooks and references for the course and outlines 12 lectures covering applications of integration such as length, volume, surface area and multiple integrals including change of order and change of variables in double and triple integrals.

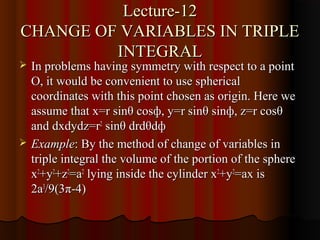
![Lecture-1
APPLICATIONS OF INTEGRATION
Here we study some important applications of
integration like Length of arc, Volume,
Surface area etc.,
RECTIFICATION: The process of finding the
length of an arc of the curve is called
rectification.
Length of an arc S=∫[1+(dy/dx)2]1/2](https://image.slidesharecdn.com/m1unit-vjntuworld-130410133015-phpapp01/85/M1-unit-v-jntuworld-8-320.jpg)
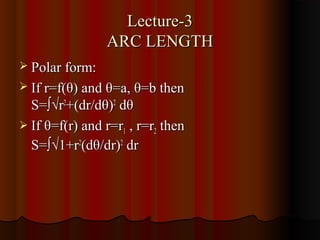
![Lecture-2
LENGTH OF
CURVE(RECTIFICATION)
The process of finding the length of an arc of
the curve is called rectification. We can find
length of the curve in Cartesian form, Polar
form and Parametric form.
Length of curve in cartesian form: S= ∫[1+
(dy/dx)2]1/2
Length of curve in parametric form:
S=∫√(dx/dθ)2+(dy/dθ)2 dθ](https://image.slidesharecdn.com/m1unit-vjntuworld-130410133015-phpapp01/85/M1-unit-v-jntuworld-9-320.jpg)
![Lecture-7
MULTIPLE INTEGRALS
Let y=f(x) be a function of one variable
defined and bounded on [a,b]. Let [a,b] be
divided into n subintervals by points x 0,…,xn
such that a=x0,……….xn=b. The generalization
of this definition ;to two dimensions is called a
double integral and to three dimensions is
called a triple integral.](https://image.slidesharecdn.com/m1unit-vjntuworld-130410133015-phpapp01/85/M1-unit-v-jntuworld-14-320.jpg)