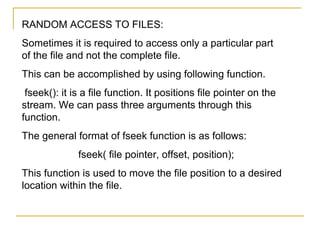
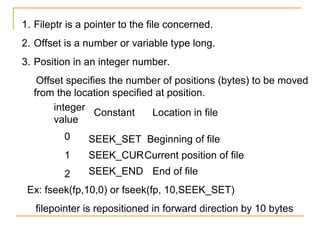
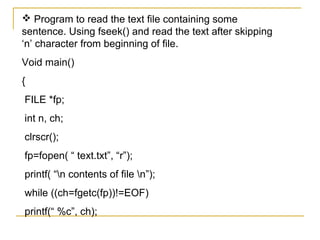
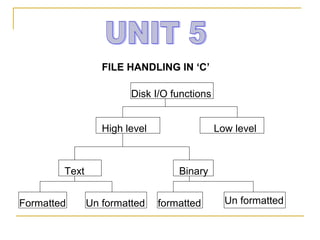
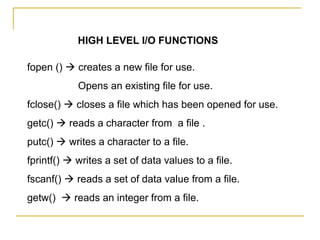
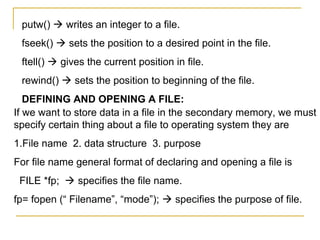
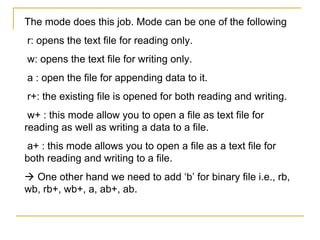
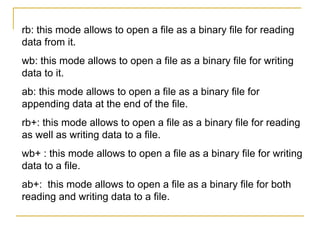
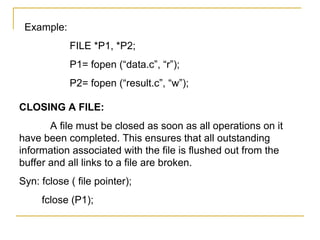
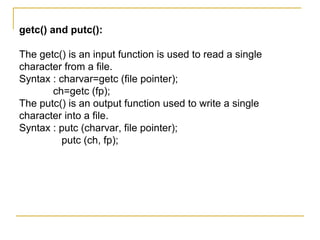
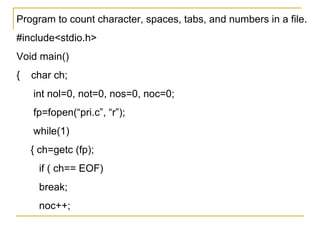
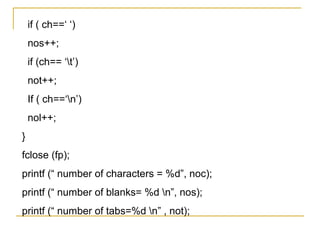
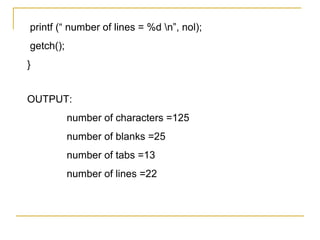
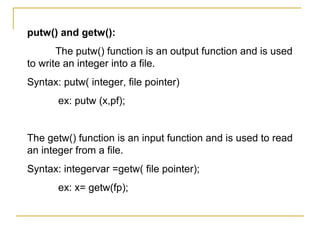
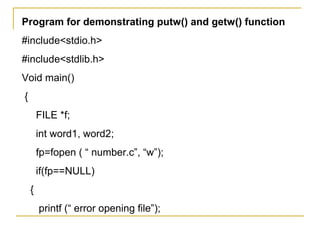
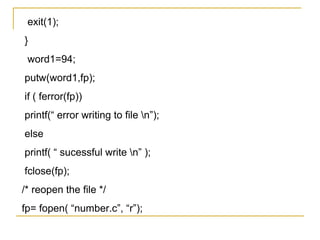
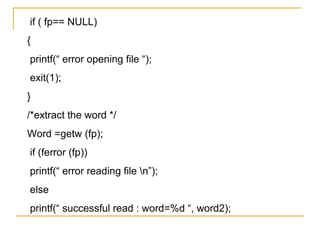
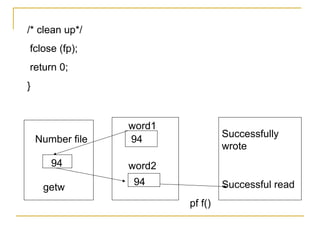
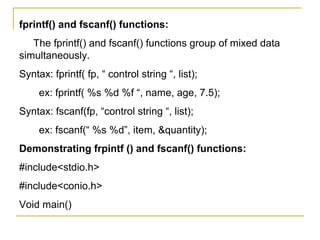
This document discusses file handling in C programming. It describes the high level and low level methods of performing file operations in C using functions like fopen(), fclose(), getc(), putc(), fprintf(), fscanf(), getw(), putw(), fseek(), and ftell(). It explains how to open, read, write, close and perform random access on files. Functions like fopen(), fclose() are used to open and close files while getc(), putc(), fprintf(), fscanf() are used to read and write data from files.
![{
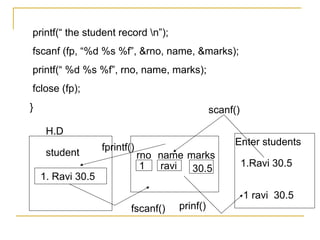
FILE *fp;
int rno;
char name[30];
float marks;
fp=fopen(“ student.c”, “w”);
printf( “ enter student record n”);
scanf(“ %d %s %f “,& rno, name, &marks);
fprintf( “ fp, “ %d %s %f “, rno, name, marks);
fclose( fp);
fp= fopen(“ student.c”, “r”);](https://image.slidesharecdn.com/unit5-130410135714-phpapp02/85/Unit5-19-320.jpg)