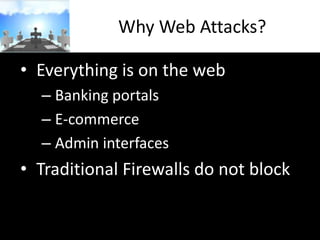
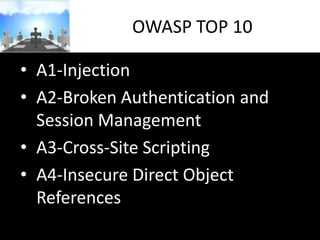
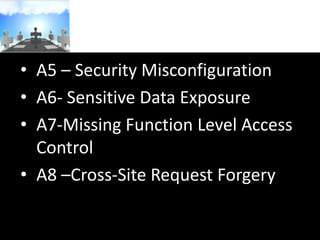
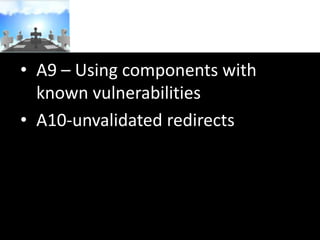
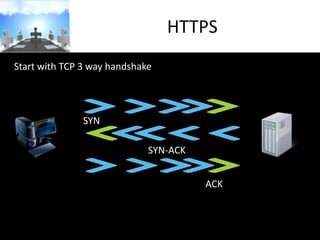
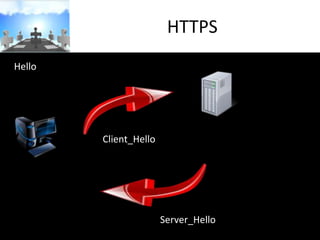
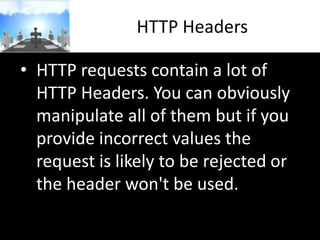
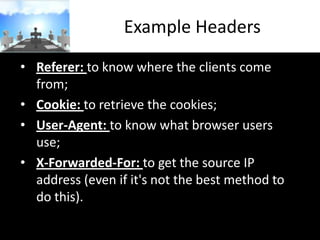
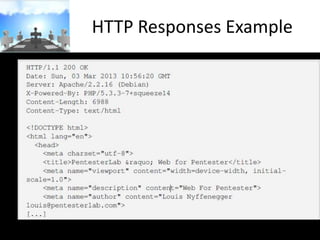
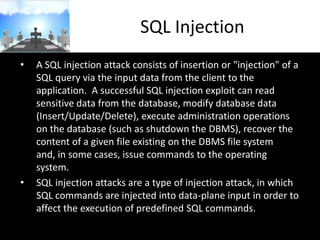
The document discusses various web-based attacks such as SQL injection, cross-site scripting (XSS), and cross-site request forgery (CSRF). It provides an overview of these attacks, including how they work and examples. It also covers related topics like the HTTP protocol, URLs, cookies, and the OWASP Top 10 list of most critical web application security risks.