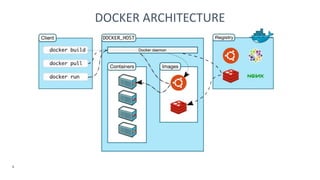
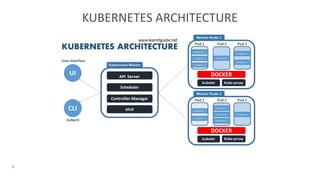
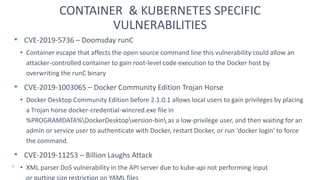
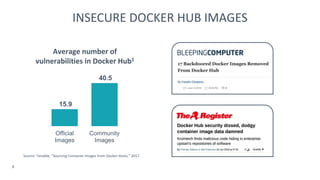
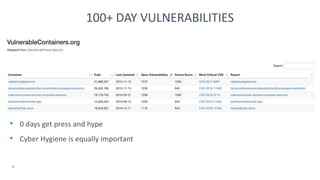
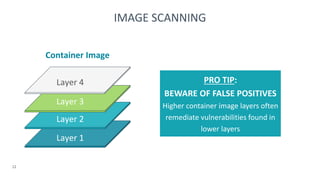
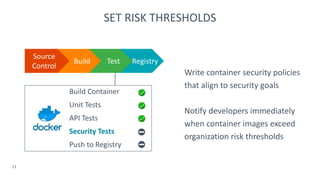
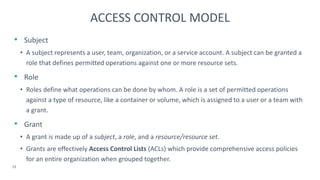
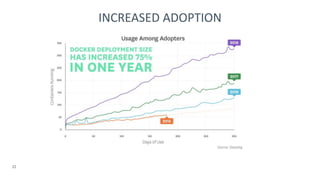
The document discusses container security, focusing on visibility, vulnerabilities, access control, and organizational challenges. It highlights critical vulnerabilities in Docker and Kubernetes, emphasizing the importance of adopting security best practices, including image scanning, access control models, and collaborative threat modeling. Additionally, it advocates for shared responsibility in security across teams to ensure effective risk management and compliance.