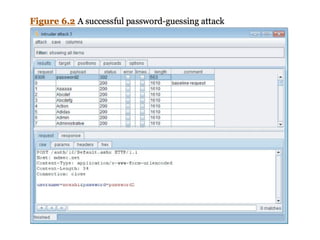
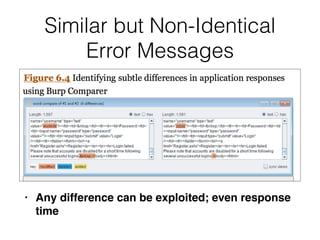
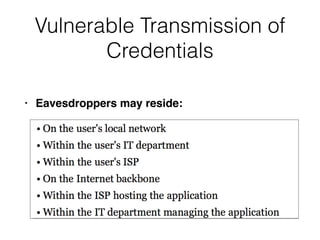
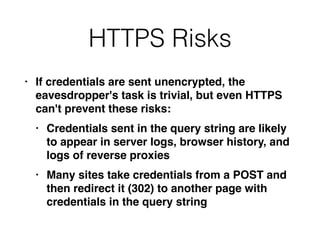
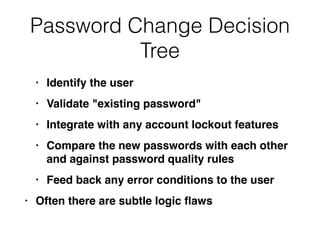
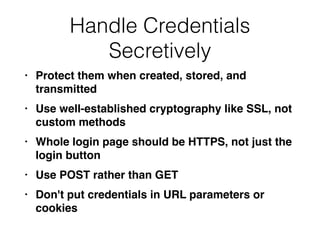
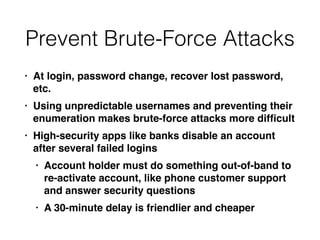
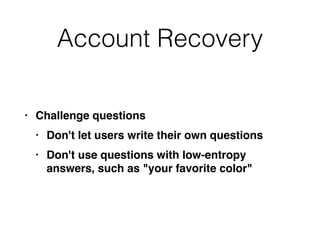
Chapter 6 of 'Securing Web Applications' discusses various authentication attack vectors and their defenses, highlighting that over 90% of applications use username and password authentication. It emphasizes the need for stronger methods like two-factor authentication, secure credential storage, and validated password change functionalities to mitigate risks such as brute-force attacks, username enumeration, and insecure transmission of credentials. The chapter also outlines best practices for securing authentication processes, including the implementation of multi-stage logins, proper logging of events, and protecting user data from vulnerabilities.