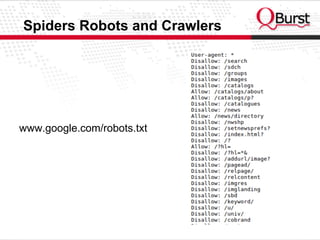
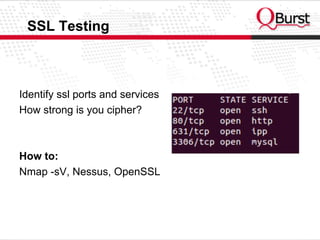
This document summarizes web application security testing. It discusses understanding how web applications work and common security risks. It then outlines the main steps of a security test: information gathering, configuration management testing, authentication testing, authorization testing, business logic testing, data validation testing, and denial of service testing. Specific techniques are provided for each step like using tools like Nikto, ZAP, and Hydra or manually testing authentication, injections, error handling, and more.























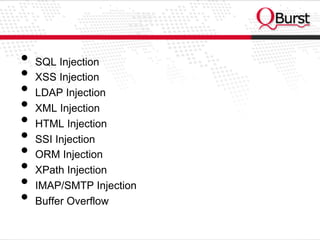

![Testing for SQL Wildcard Attacks
SELECT * FROM Article WHERE Content LIKE '%foo%'
SELECT TOP 10 * FROM Article WHERE Content LIKE
'%_[^!_%/%a?F%_D)_(F%)_%([)({}%){()}£$&N%_)$*£()
$*R"_)][%](%[x])%a][$*"£$-9]_%'](https://image.slidesharecdn.com/webapplicationsecuritytesting-130607074438-phpapp02/85/Web-application-security-Testing-32-320.jpg)



