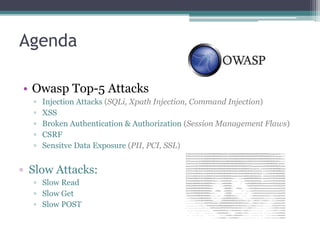
The presentation discusses the OWASP Top 5 web attacks, including SQL injection, XSS, and broken authentication, with prevention measures for each type. It explains the mechanisms of various attack vectors such as command injection and CSRF, along with their impact and mitigation strategies. Additionally, it covers sensitive data exposure and slow attacks, providing guidance on safeguarding applications and networks.
![Broken Auth
• Protection:
▫ Password Change Controls
▫ Password Strength
▫ Password Expiration
▫ Password Storage
▫ Protection In Transit
▫ Avoid Cookieless Session
▫ Avoid homegrown authentication schema
▫ Look into IP/Location/Browser/OS combination
▫ Always have unique session ID bound with IP
▫ Double-check password on certain activity
▫ Expire sessions early
▫ Don’t forget logout button [which should destroy the server/client session]](https://image.slidesharecdn.com/presentationonattacks-150820183936-lva1-app6892/85/Presentation-on-Web-Attacks-10-320.jpg)

![Slow Attacks - Protection
• Drop Connections which HTTP method not supported by URL
• Limit the header and message body to a minimal reasonable length
• Set an absolute connection timeout, if possible.
• Try to maximize server max no of connections
• Define minimum incoming data rate
• Define max no of concurrent connections from same IP
• Blacklist the known attack user-agents [Slowloris uses *MSIE*MSOffice 12*]](https://image.slidesharecdn.com/presentationonattacks-150820183936-lva1-app6892/85/Presentation-on-Web-Attacks-20-320.jpg)