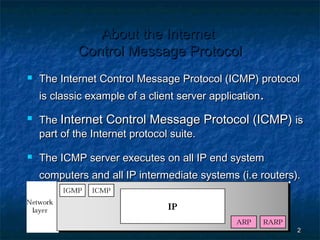
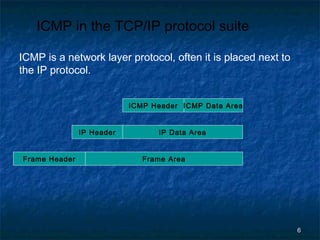
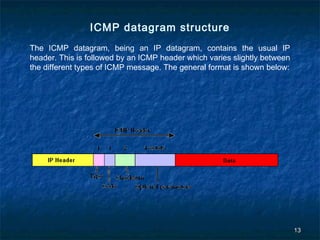
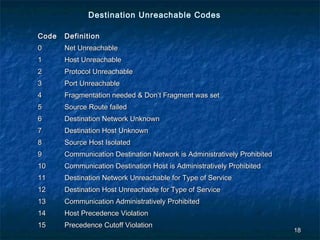
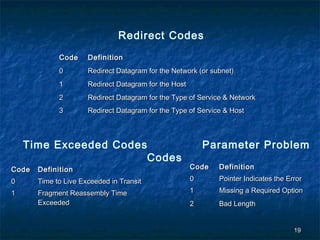
The Internet Control Message Protocol (ICMP) is used to report issues with the delivery of IP packets. It allows devices on the network to check connectivity and diagnose routing problems. ICMP messages are transmitted as IP packets and used by ping and traceroute utilities. It supports functions like announcing network errors, congestion, and assisting troubleshooting. While providing important feedback, ICMP redirect messages can potentially direct traffic to unauthorized systems if not restricted to trusted sources.