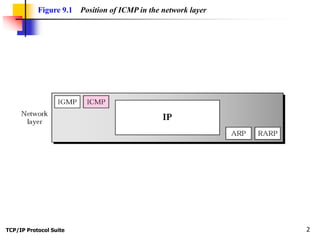
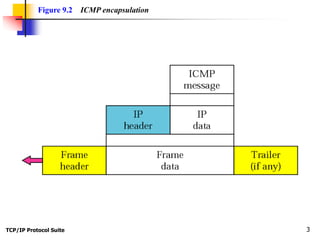
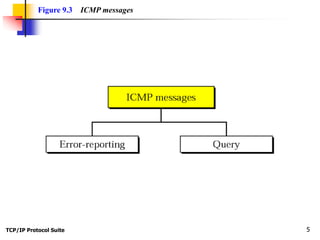
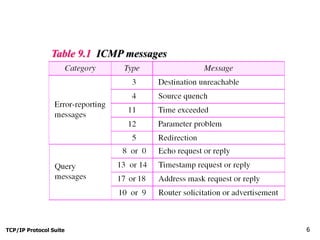
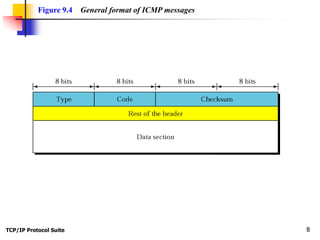
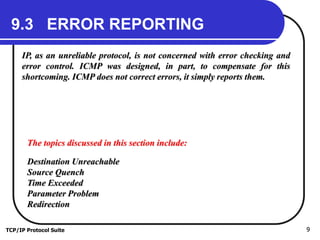
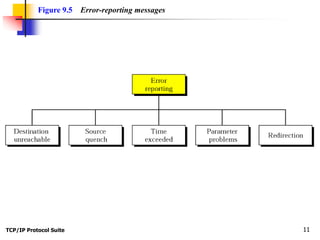
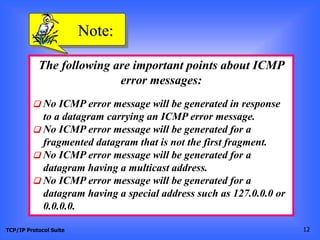
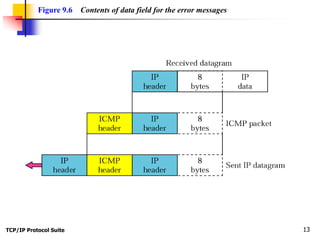
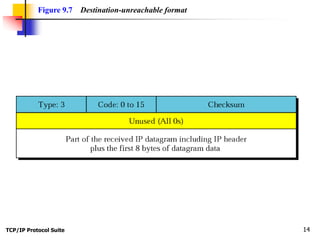
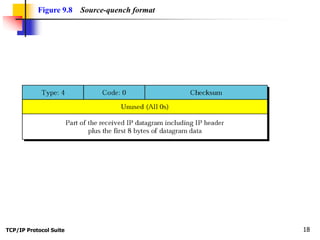
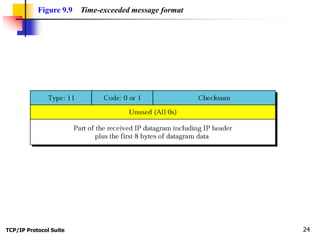
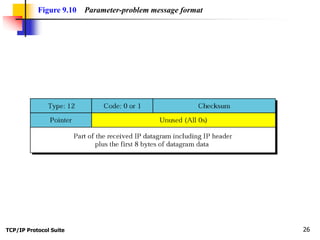
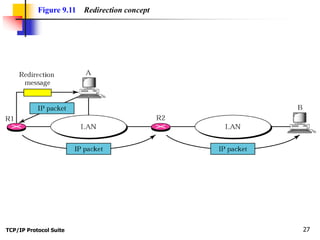
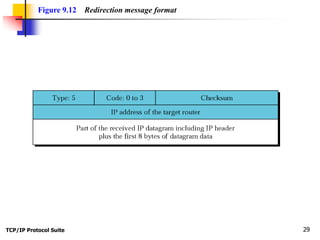
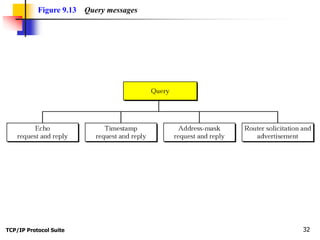
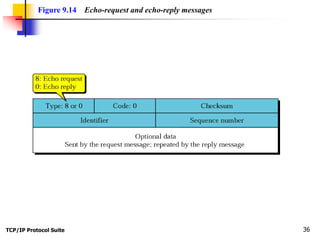
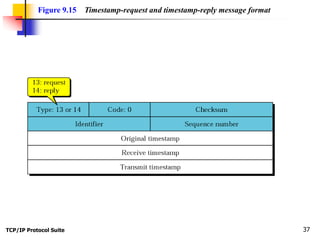
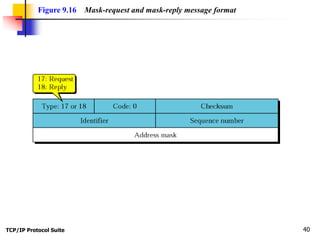
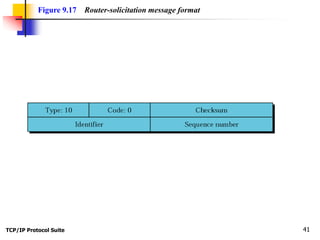
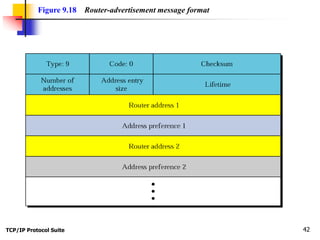
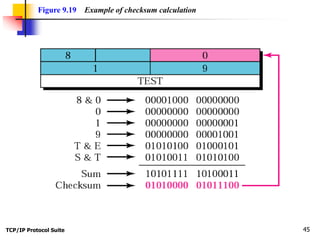
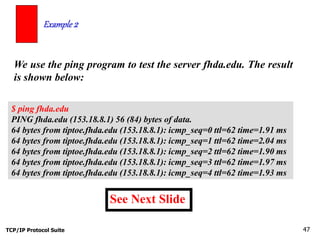
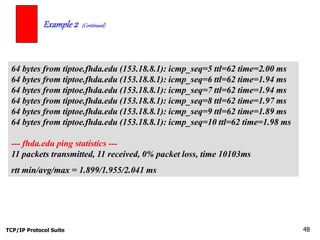
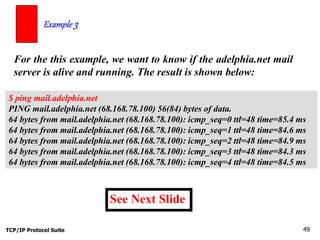
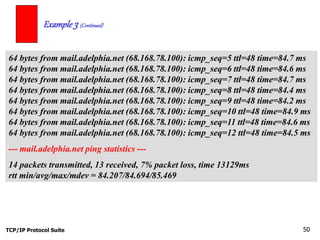
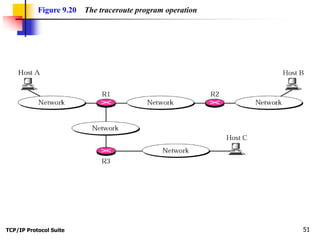
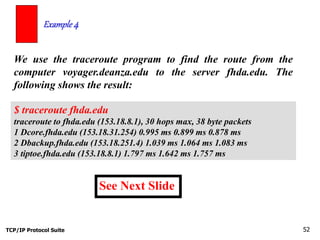
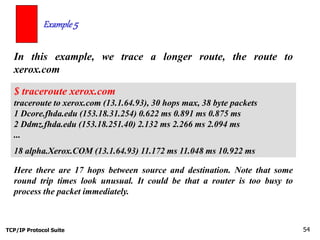
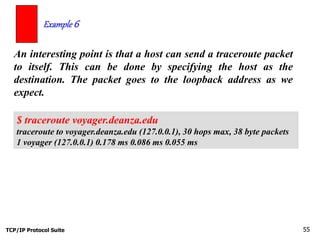
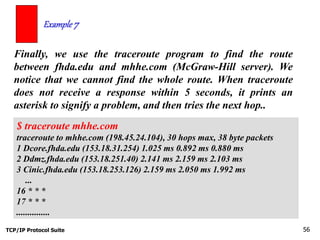
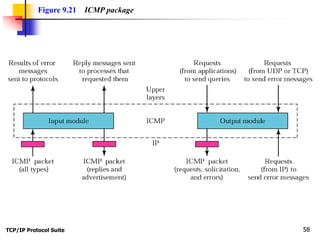
This document discusses the Internet Control Message Protocol (ICMP). It begins by listing the chapter objectives and explaining ICMP's position in the TCP/IP protocol suite. It then describes ICMP's message formats, types including error reporting and query, and the ICMP checksum. The document also explains how tools like ping and traceroute use ICMP to debug networks and examine routes. It provides examples of using these tools and interpreting their output.