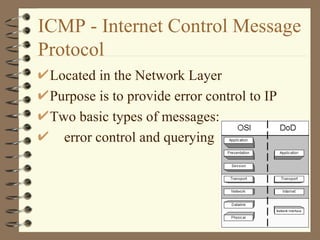
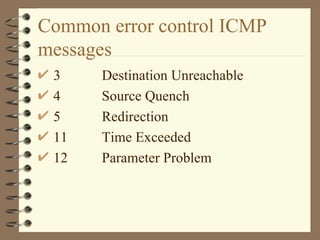
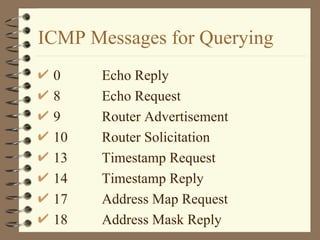
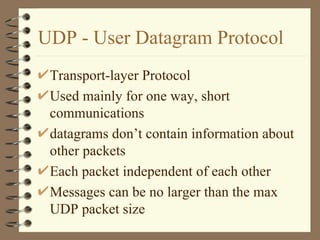
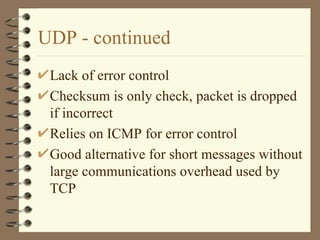
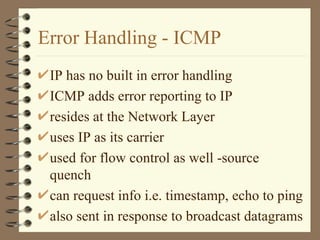
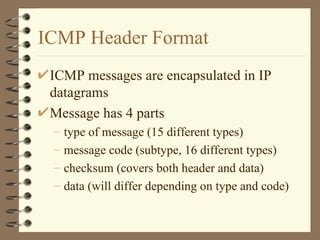
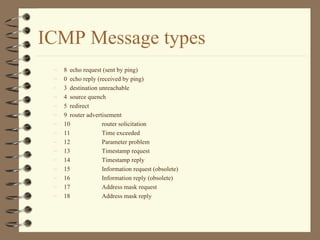
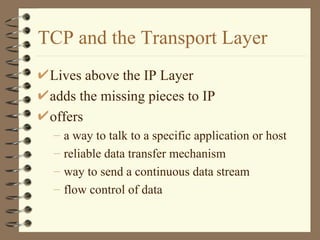
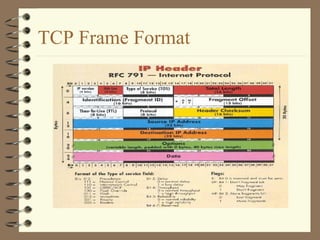
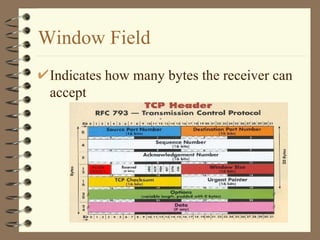
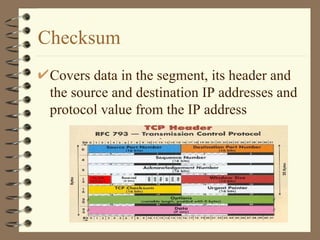
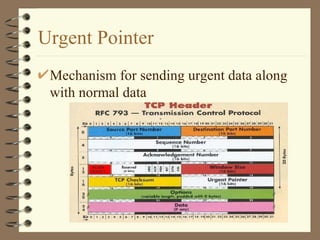
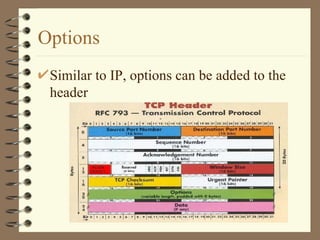
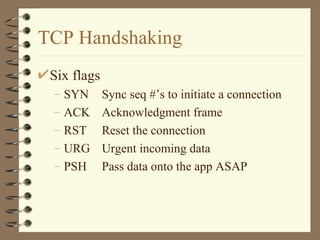
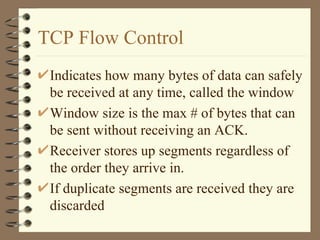
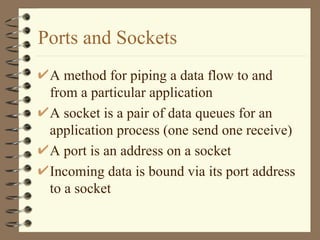
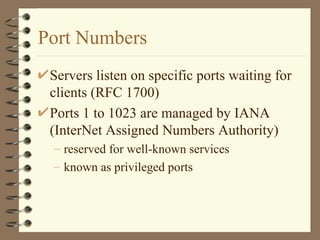
This document summarizes several internet protocols including IP, TCP, UDP, and ICMP. It describes key aspects of each protocol such as their purpose, packet structure, error handling mechanisms, and how they interact to enable communication over the internet. IP is a connectionless protocol that forwards packets based on destination addresses. TCP and UDP are transport layer protocols, with TCP providing reliable connections and UDP being connectionless. ICMP provides error reporting and control for IP. Port numbers and sockets are used to direct communication to specific applications.