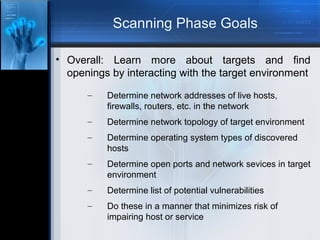
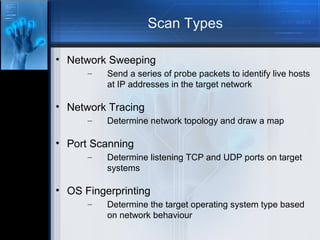
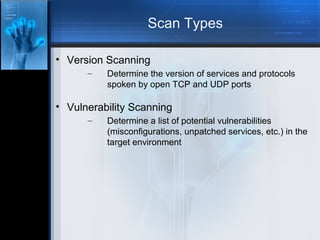
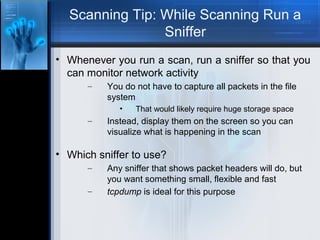
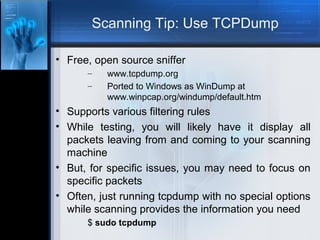
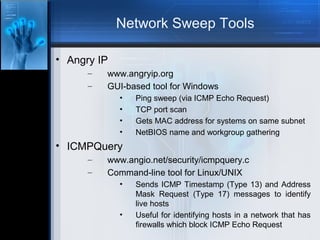
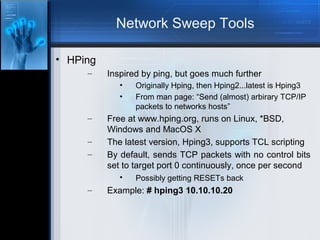
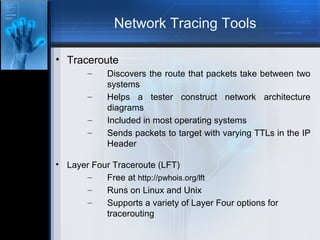
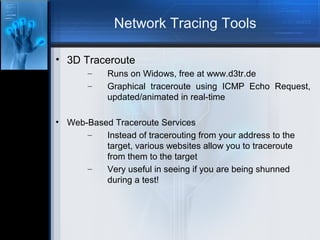
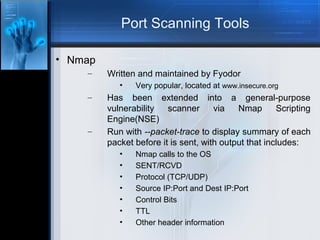
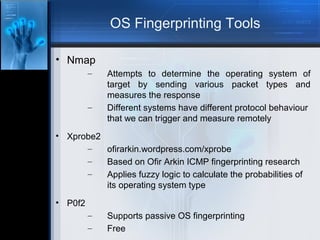
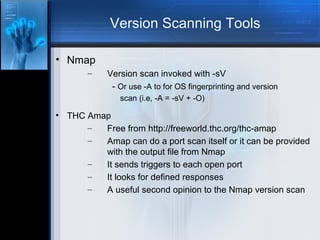
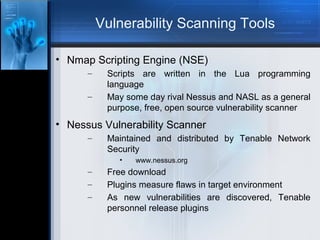
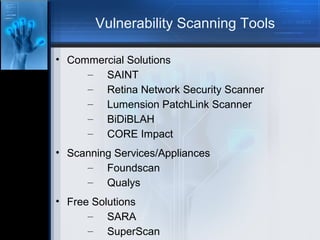
The document outlines various phases of network scanning, including goals, types of scans, and tools used for network sweeping, tracing, port scanning, OS fingerprinting, and vulnerability assessment. It emphasizes the importance of minimizing risks during scans and suggests using tools like tcpdump, nmap, and various free utilities for effective scanning. Additionally, it provides tips for gathering information about network environments while maintaining security and efficiency.