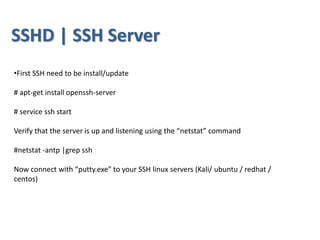
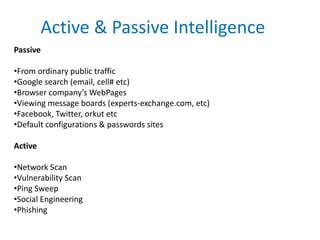
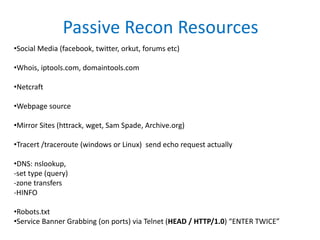
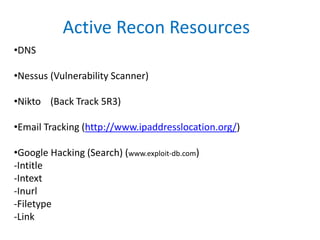
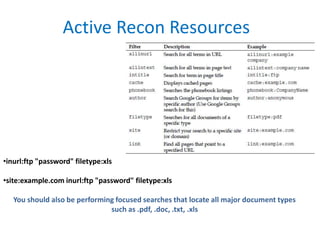
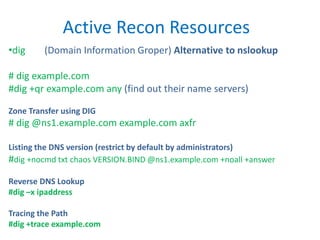
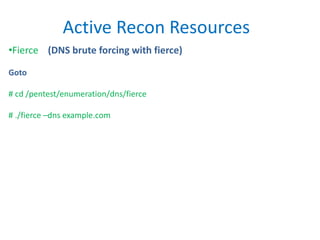
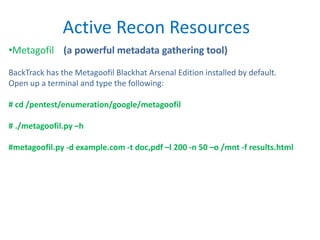
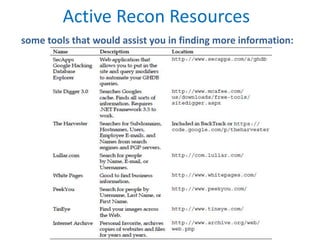
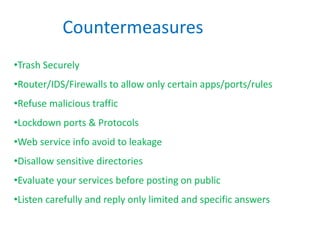
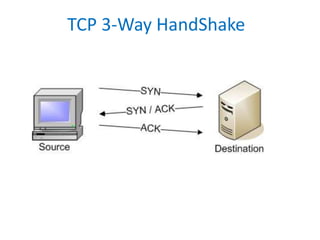
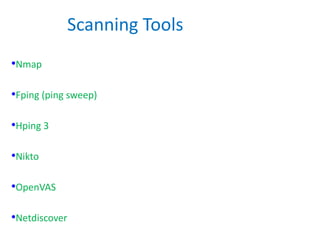
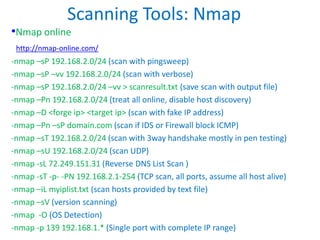
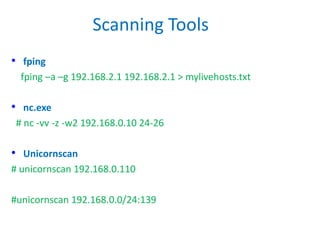
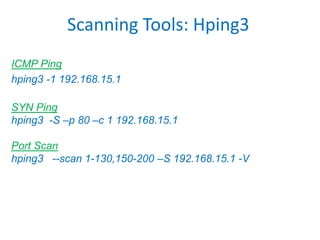
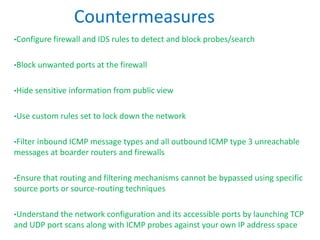
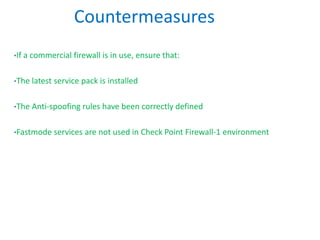
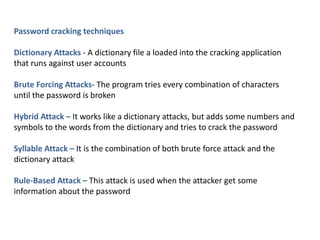
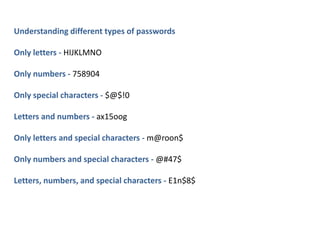
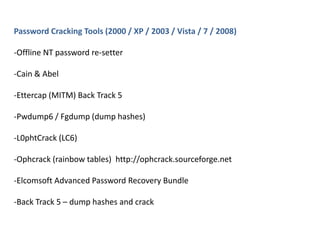
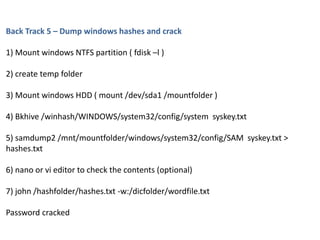
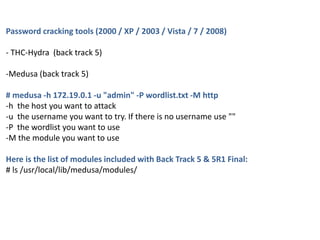
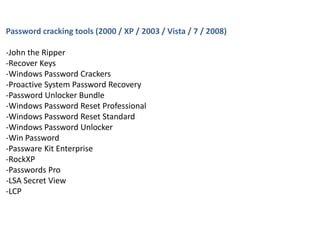
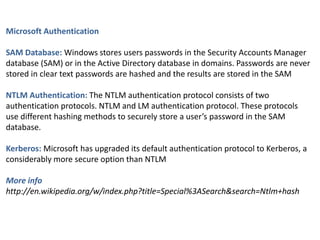
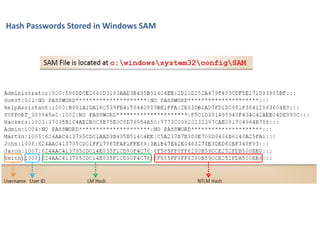
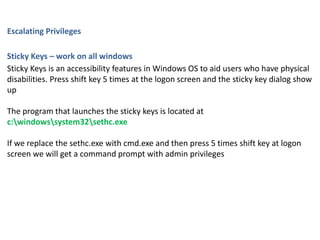
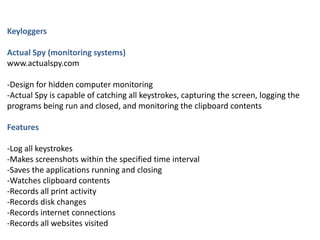
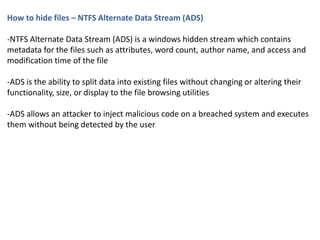
The document provides instructions on how to configure an SSH server on Linux, perform footprinting and reconnaissance, scanning tools and techniques, enumeration tools and techniques, password cracking techniques and tools, privilege escalation methods, and keylogging and hidden file techniques. It discusses active and passive footprinting, Nmap port scanning, NetBIOS and SNMP enumeration, Windows password hashes, the sticky keys method for privilege escalation, ActualSpy keylogging software, and hiding files using NTFS alternate data streams. Countermeasures for many of these techniques are also outlined.