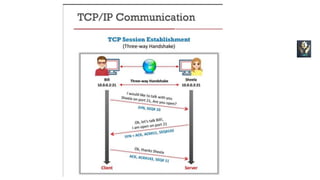
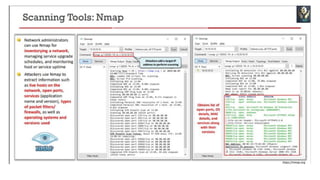
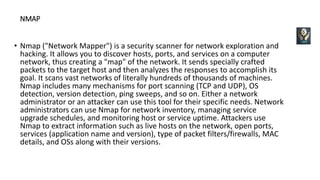
Network scanning is the process of gathering detailed information about targets on a network through complex reconnaissance techniques. It identifies active machines, operating systems, open ports and services. This enables attackers to profile organizations by discovering specific IP addresses, OSs, system architectures and services running on each computer. Common types of scanning include port scanning to identify open ports and services, network scanning to find active hosts and IP addresses, and vulnerability scanning to detect known weaknesses. The objectives of network scanning are to discover live hosts and open ports, identify OSs and applications to determine the best means of entry and exploit vulnerabilities. Nmap is a widely used security scanner that sends crafted packets to analyze responses and map networks by identifying hosts, ports, services, firewalls