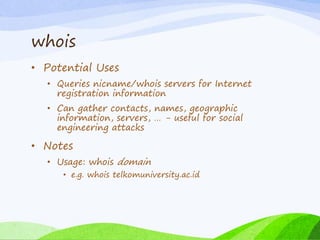
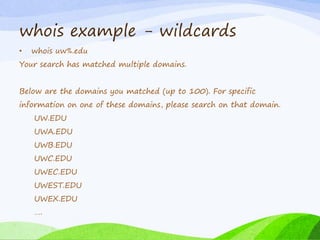
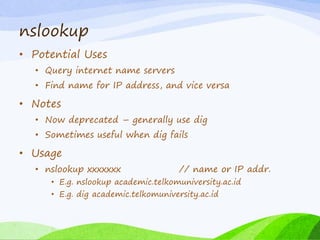
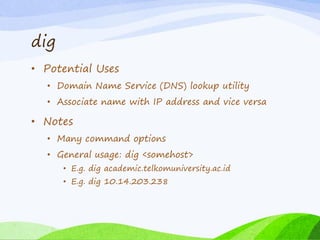
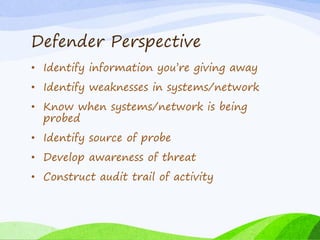
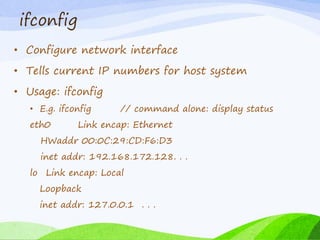
This document discusses footprinting and information gathering techniques for network security. It defines footprinting as gathering information about potential target systems and networks. Both attacker and defender perspectives are considered. Basic Linux and Windows tools are covered, such as hostname, ifconfig, who, ping, traceroute, dig, nslookup, whois, arp and netstat for gathering system, network topology and user information. Packet sniffers like Wireshark are also introduced for analyzing network traffic. The document emphasizes that even basic tools can provide a lot of useful information to attackers, so defenders should aim to minimize what they reveal.


![last
• Show last N users on system
• Default: since last cycling of file
• -N: last N lines
• Useful for identifying unusual activity in recent past
• Usage: last [-n]
• E.g. last -3
wagnerpj pts/1 137.28.253.254 Sat Feb 5 15:40 still logged in
flinstf pts/0 137.28.191.74 Sat Feb 5 15:38 still logged in
rubbleb pts/0 c48.someu.edu Sat Feb 5 14:38 - 15:25 (00:46)](https://image.slidesharecdn.com/chapter3footprinting-160211014509/85/Chapter-3-footprinting-12-320.jpg)
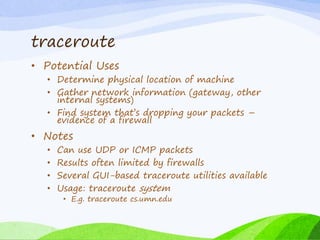
![traceroute example - Success
C:UsersTemp>tracert telkomuniversity.ac.id
Tracing route to telkomuniversity.ac.id [10.14.203.238]
over a maximum of 30 hops:
1 1 ms <1 ms <1 ms 192.168.60.1
2 6 ms 6 ms 4 ms 10.11.221.1
3 7 ms 3 ms 2 ms 10.0.0.254
4 3 ms 1 ms 1 ms 10.14.203.238
Trace complete.
C:UsersTemp>](https://image.slidesharecdn.com/chapter3footprinting-160211014509/85/Chapter-3-footprinting-15-320.jpg)
![traceroute example - blocked
C:UsersTemp>tracert detik.com
Tracing route to detik.com [203.190.242.69]
over a maximum of 30 hops:
1 1 ms 1 ms 2 ms 192.168.60.1
2 5 ms 2 ms 2 ms 10.11.221.1
3 4 ms 9 ms 3 ms 10.0.0.254
4 * * * Request timed out.
5 * * * Request timed out.
Trace complete.
C:UsersTemp>](https://image.slidesharecdn.com/chapter3footprinting-160211014509/85/Chapter-3-footprinting-16-320.jpg)