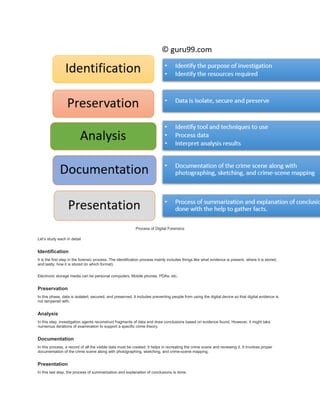
Digital forensics is the process of preserving, identifying, and analyzing digital evidence found in devices like computers, networks, and mobile phones for use in legal cases. It involves identifying and collecting potential evidence, preserving the integrity of the evidence, analyzing the evidence found, documenting the findings, and then presenting results in court. The history of digital forensics dates back to the late 20th century. Today it helps investigate various cases like intellectual property theft, fraud, and cybercrime. Challenges include the growing amounts of digital data and changes in technology requiring updated tools and methods.