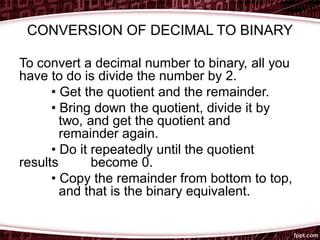
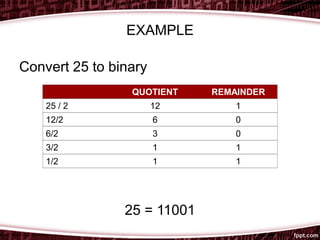
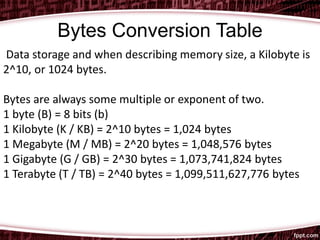
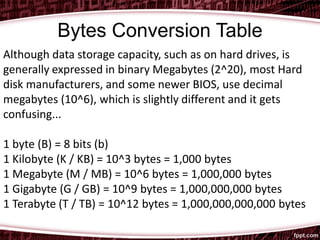
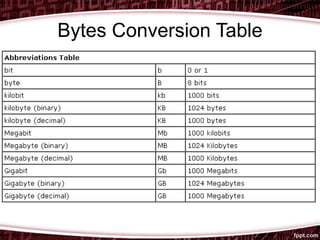
This document discusses digital representation and binary conversion. It defines a bit as the basic unit of data in computing and explains how ASCII uses binary codes to represent letters, numbers, and characters. It then demonstrates how to convert between decimal and binary numbers through long division and provides an example of converting 25 to its binary equivalent of 11001. Finally, it includes tables defining bytes, kilobytes, megabytes, gigabytes and terabytes in terms of bits and bytes.