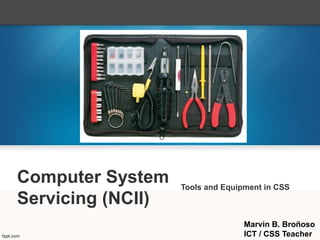
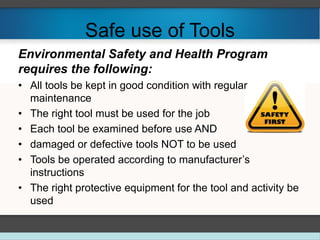
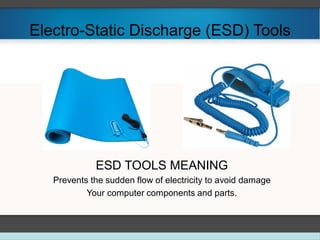
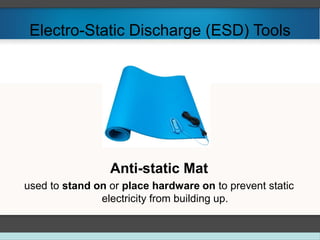
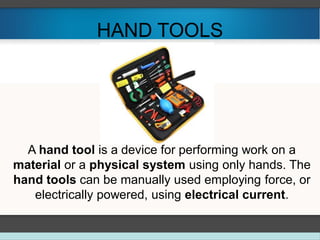
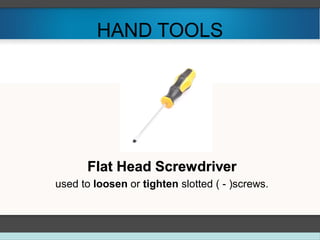
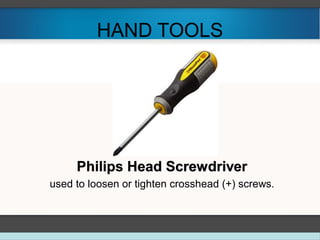
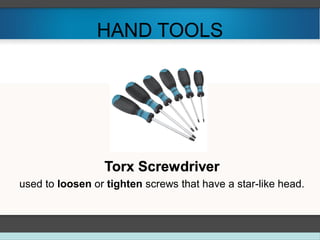
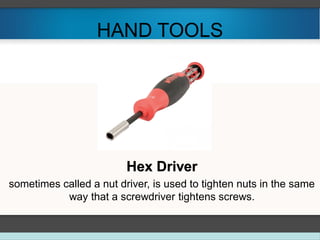
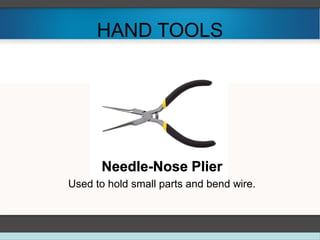
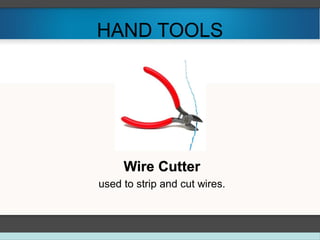
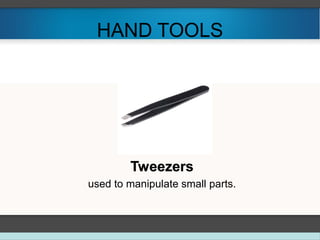
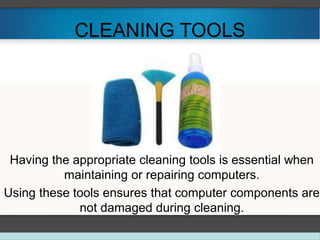
The document discusses tools and equipment used in computer system servicing (CSS). It describes proper tool selection, preparation for tasks, safe tool use, and different types of tools including ESD tools, hand tools, cleaning tools, and diagnostic tools. Examples are provided for each tool type, such as anti-static wrist straps, screwdrivers, tweezers, compressed air, and multimeters. Maintaining tools and selecting the right tool for each job is important for safety and completing repairs efficiently.