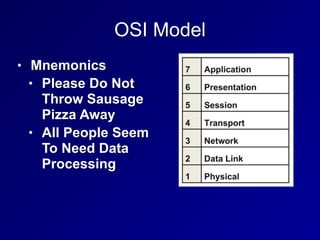
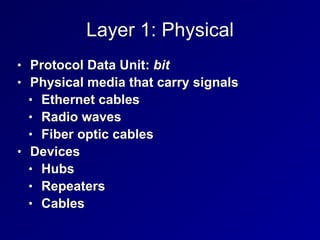
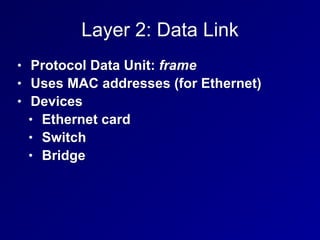
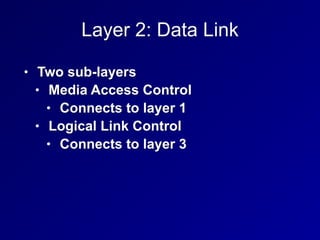
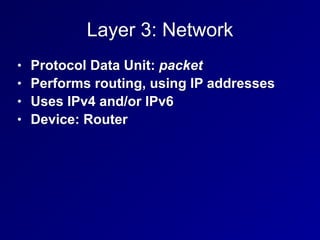
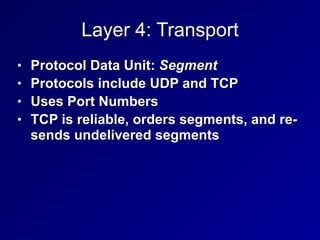
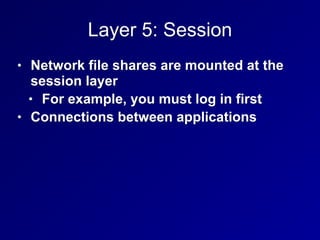
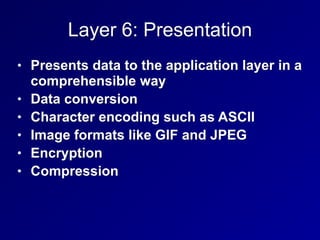
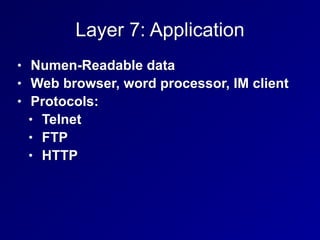
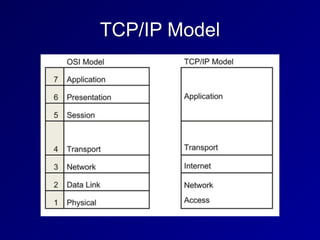
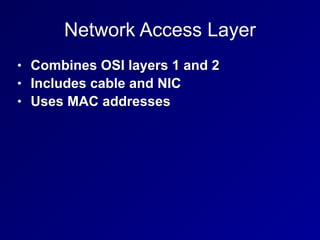
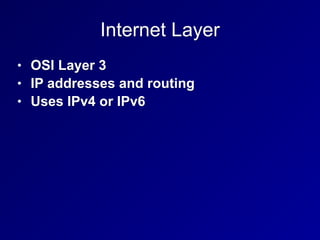
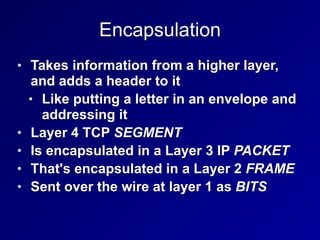
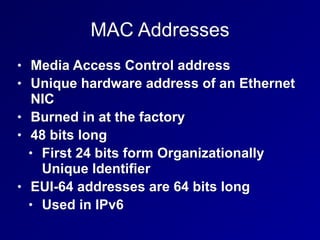
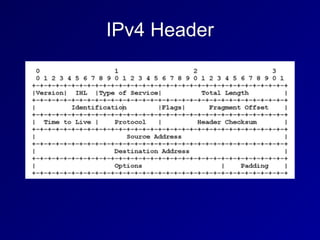
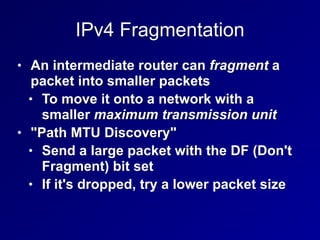
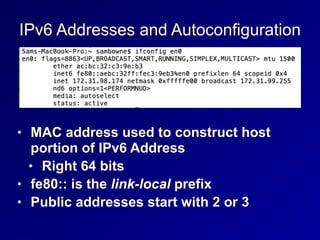
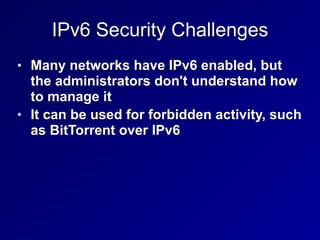
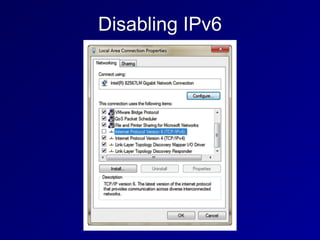
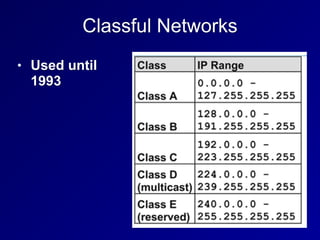
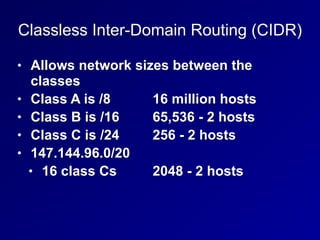
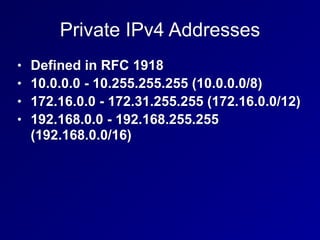
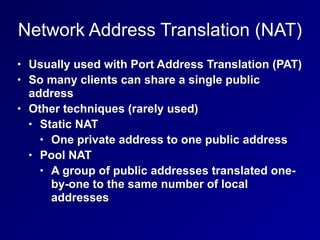
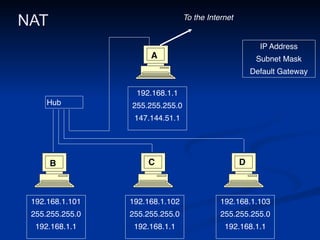
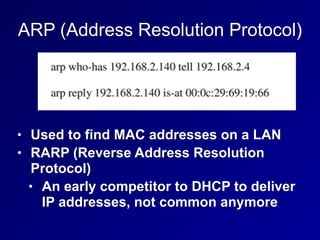
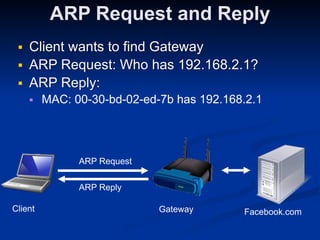
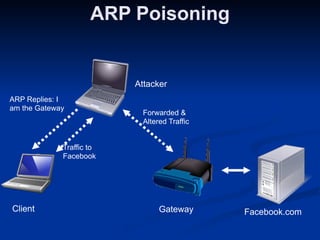
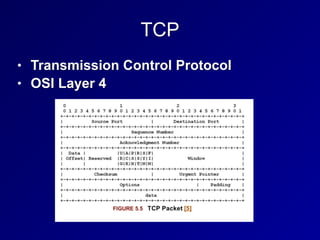
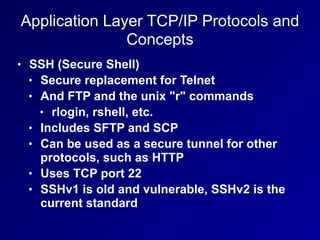
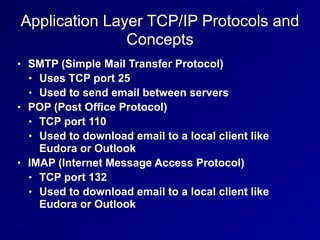
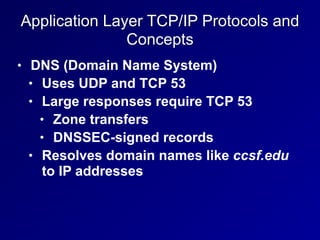
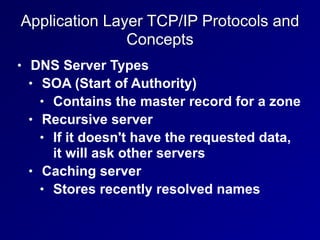
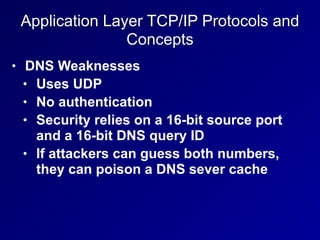
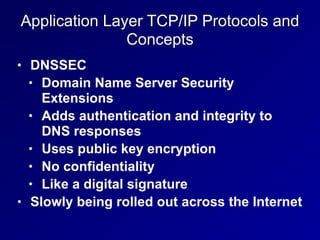
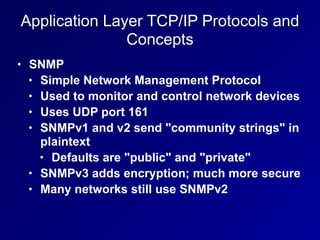
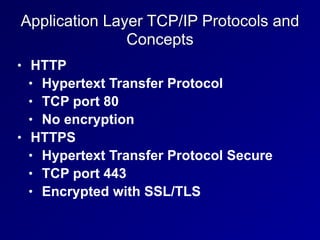
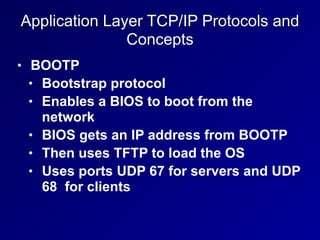
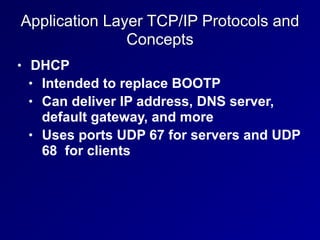
This document provides an overview of communication and network security concepts, covering fundamental network architectures such as simplex, half-duplex, and full duplex, and various network types including LAN, WAN, and MAN. It discusses crucial protocols and models like OSI and TCP/IP, detailing the layers, corresponding data units, and key concepts including encapsulation and network addressing like IPv4 and IPv6. Security challenges related to DNS and network management protocols such as SNMP and DHCP are also addressed.