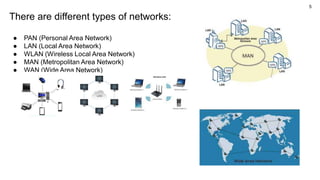
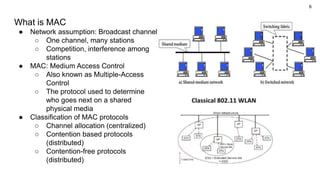
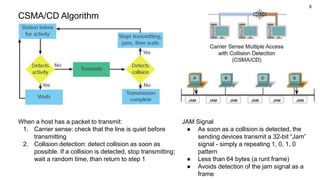
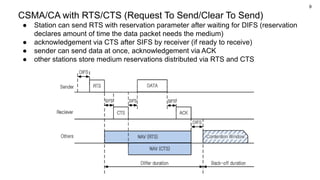
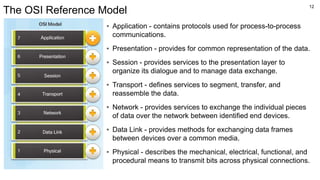
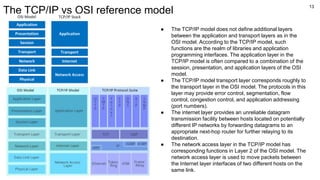
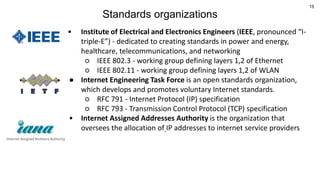
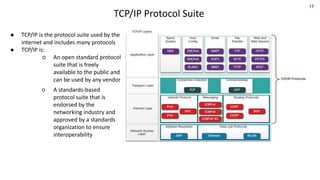
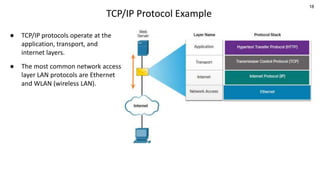
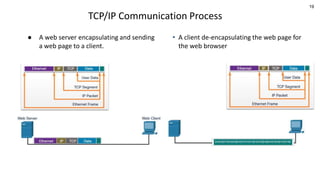
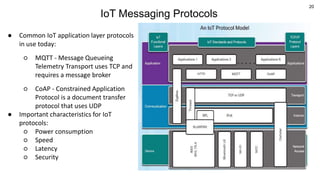
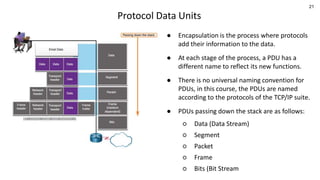
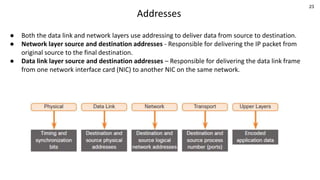
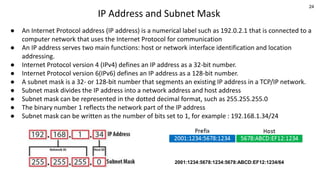
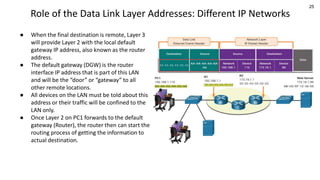
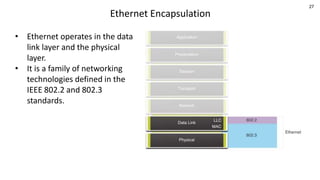
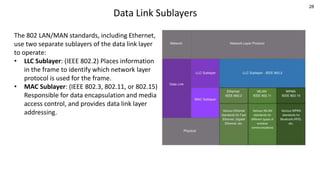
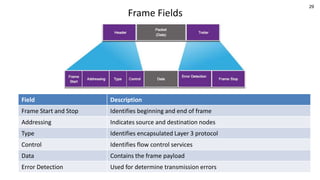
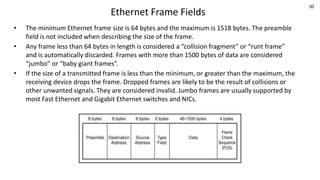
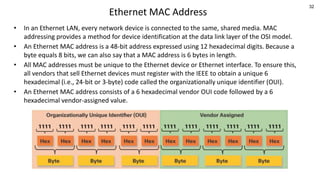
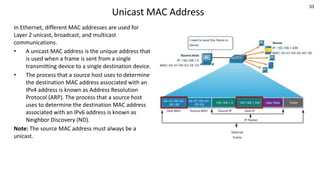
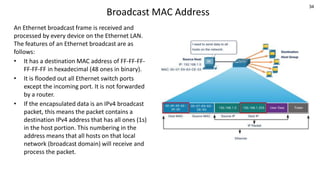
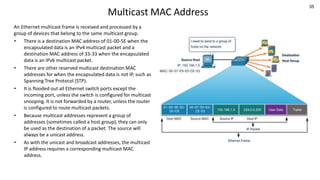
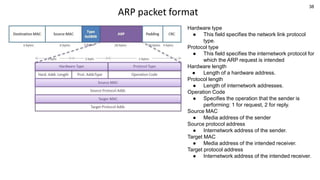
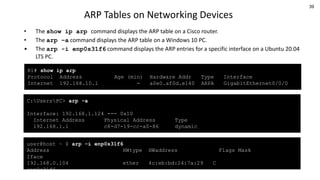
This document provides an overview of networking concepts including network types, medium access control protocols, TCP/IP protocol suite, addressing, Ethernet frames, ARP, and standards organizations. It begins with an agenda that lists these topics and includes diagrams to illustrate CSMA/CD, the OSI model, TCP/IP encapsulation, and Ethernet encapsulation. Examples are provided for different network devices, addressing formats and protocols.