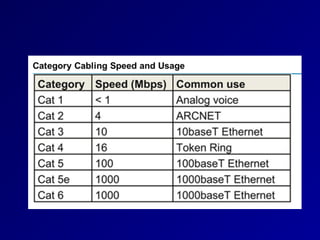
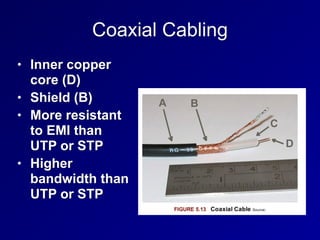
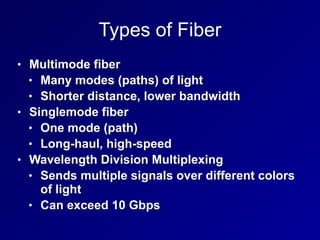
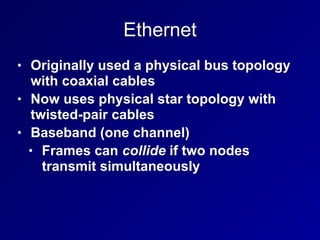
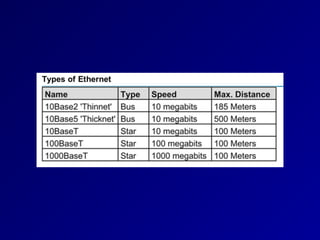
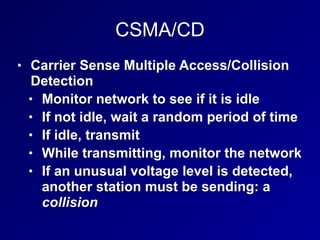
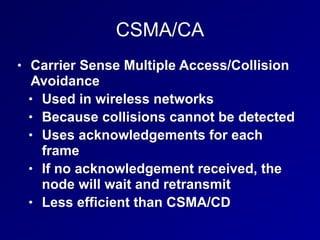
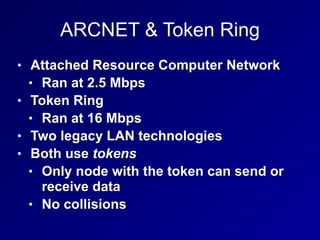
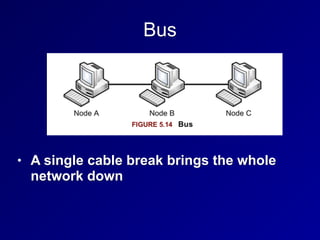
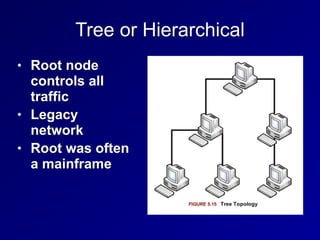
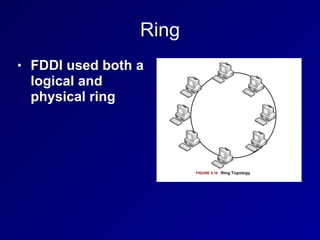
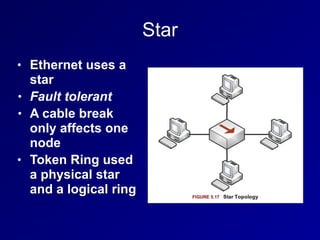
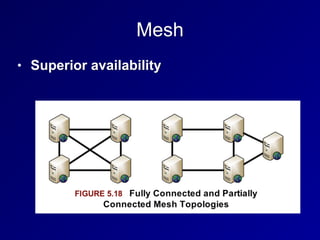
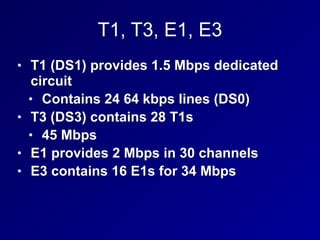
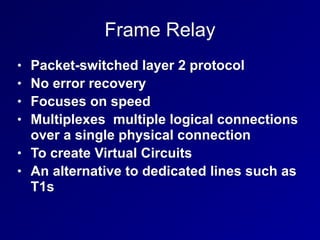
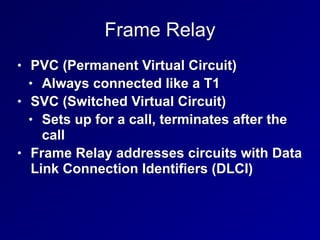
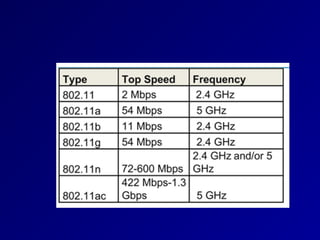
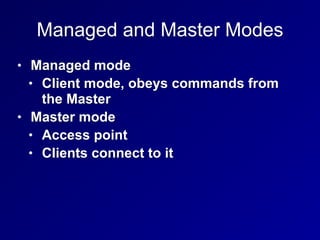
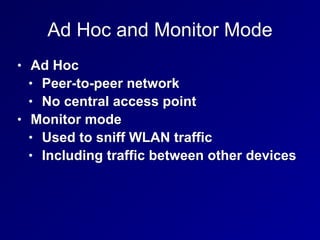
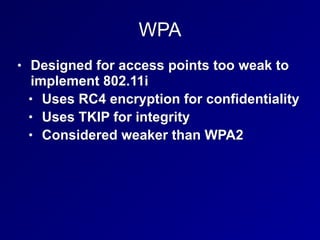
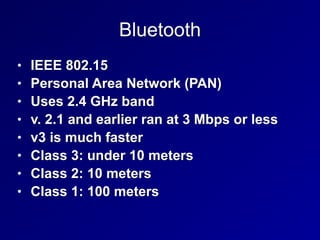
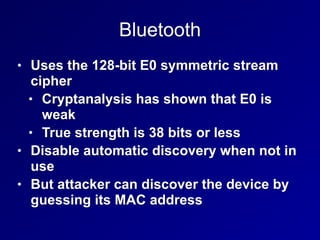
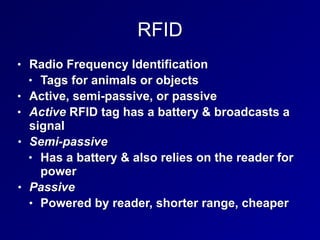
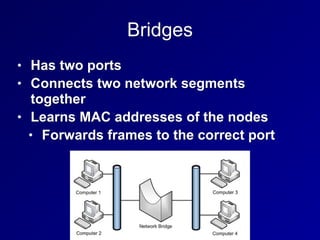
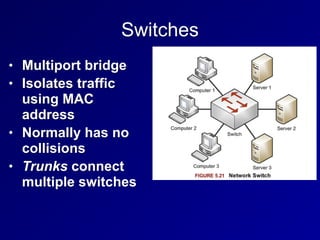
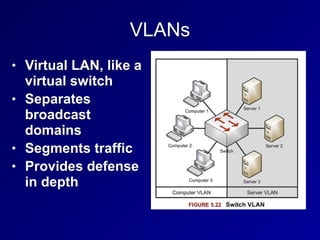
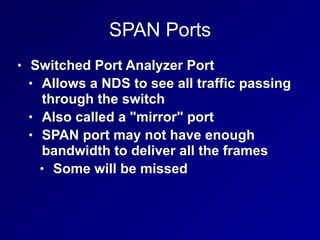
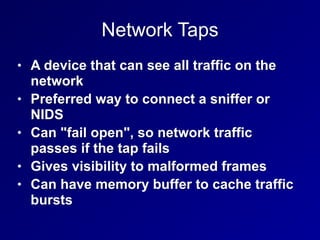
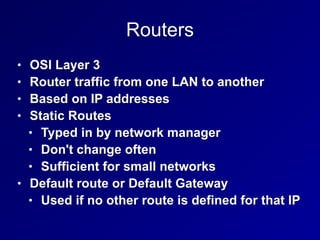
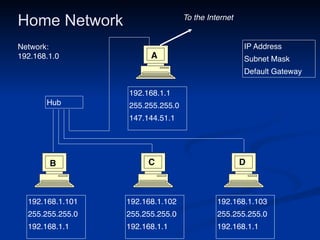
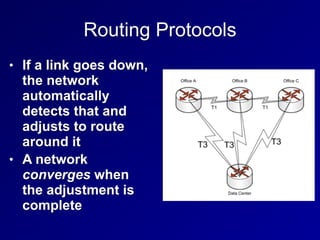
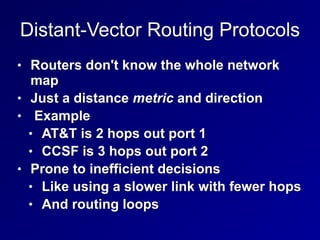
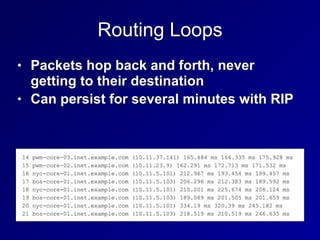
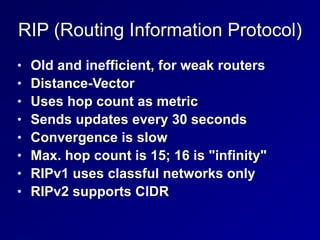
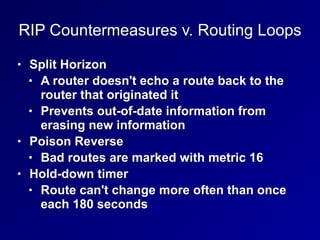
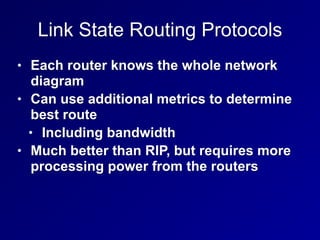
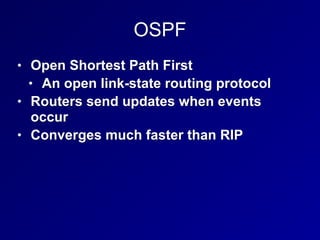
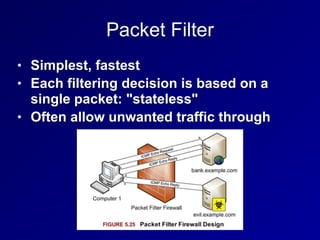
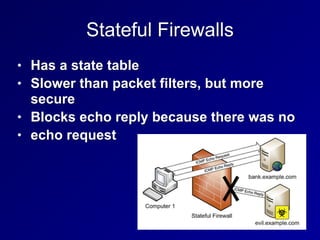
This document provides an overview of networking concepts related to communication and network security. It discusses common cabling types used to physically connect networks like twisted pair, coaxial, fiber optic and their characteristics. It also covers common LAN technologies and protocols like Ethernet, token ring, FDDI, physical network topologies and WAN protocols. The document then discusses wireless LANs, Bluetooth, RFID and secure network devices like switches, routers, firewalls and routing protocols.