The document provides an overview of the Metasploit framework, including its architecture, key components, and how it can be used to run exploits and payloads. Some key points include:
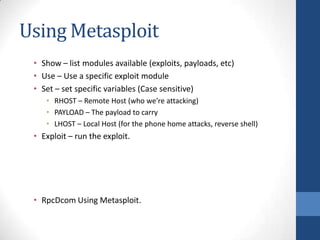
- Metasploit is an open-source platform for developing, testing, and using exploit code, with over 600 exploits and 200 payloads.
- It allows attackers to easily customize payloads to specific exploits and test exploit research.
- Meterpreter is a post-exploitation tool that avoids creating new processes or files, and provides an extensible command shell.
- The framework simplifies running attacks by automating matching exploits to payloads and testing configurations.