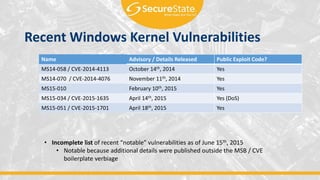
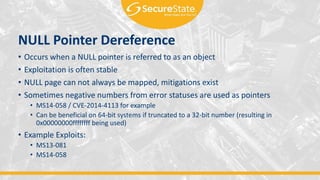
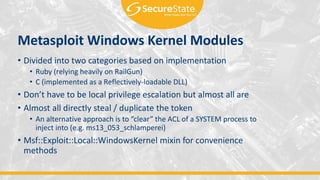
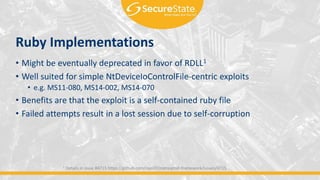
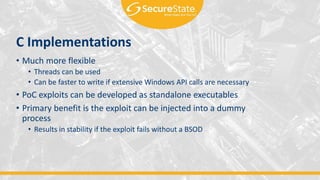
The document discusses kernel exploitation on Windows systems. It provides an overview of common vulnerability classes like write-what-where and use-after-free. It also covers techniques for executing code, mitigation technologies, writing exploits for Metasploit, and sources of instability. The speaker's background and agenda are introduced at the start.