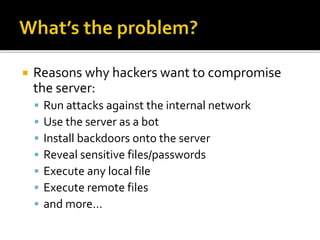
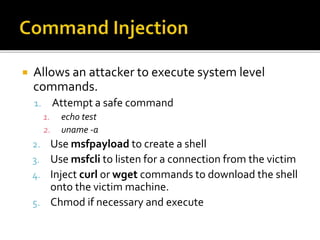
The document discusses exploiting vulnerabilities in web applications using Metasploit. It describes using Kali Linux as the attacker machine, Metasploit for exploits, payloads and establishing sessions, and Metasploitable2 as the vulnerable web server victim. Various exploitation techniques are covered like SQL injection, file uploads, and command injection. Metasploit modules, payloads, and usage are also outlined.